Category filter
How to securely bypass Factory Reset Protection for Android devices
Google Factory Reset Protection (FRP) is a feature that is enabled by default on Android devices running version 5.1 or higher to prevent unknown sources from using the device if it is reset to factory settings without your permission. If an unauthorized person attempts to reset the device, it will still require a log-in with the previously configured Google username and password. This means that if your device is lost or stolen, no one else will be able to reset or use it.
However, despite being useful, this feature can cause serious problems and give rise to a situation in which Google Account verification needs to be bypassed to use the phone. Once enabled, FRP only allows a user with a Google Account password to factory reset and activate the device. With enterprises, this is inconvenient since the company-provided devices lock into an employee’s Google Account. Furthermore, if the employee leaves the company, then the device becomes unusable as a company asset. With Hexnode UEM, you can add a Google Workspace email ID and google+ profile ID to log in to your devices to bypass FRP in situations where you forget/don’t know the previously configured Google Account credentials.
What is Factory Reset Protection?
Data protection or Factory Reset Protection (FRP), is a security feature on Android devices with Lollipop 5.1 and higher. Once FRP is activated, it prevents the use of a device after a factory data reset, unless you log in with a Google username and password that was previously set up on the device. When you perform a Factory Reset, all settings are returned to the factory default settings. All data is erased, including files and downloaded apps. If you have a Google Account set up on the device, the FRP is active. This means that after the reset, you’ll be required to log in to the Google Account using the username and password. If you have multiple Google Accounts set up on the device, you can log in using any of them.
Enable Google Factory Reset Protection using Hexnode UEM
To enable FRP:
- Login to your Hexnode portal.
- Navigate to Policies.
- Select an existing policy or create a new one by clicking on New Policy.
- From Android, select Advanced Restrictions and click on Configure.
- Go to Factory Reset Protection (Google Account Verification).
- There are three options in the drop-down list:
- Default: If this option is selected, the default settings on the device will work.
- Bypass Factory Reset Protection: Select this option to bypass Factory Reset Protection. If selected, you can log into your device locked in factory reset protection mode by entering a Google Workspace or Google Account ID instead of Google Account verification.
- Disable Factory Reset Protection: You can disable Factory Reset Protection by selecting this option. When selected, the user can skip the Google Account verification step during the set-up process.
Choose Bypass Factory Reset Protection.
- Add a Google Workspace Account and Google Account ID to sign in to your devices in situations where you forget/don’t know the previously configured Google Account credentials.
How to find your Google Account ID?
Google Account ID refers to the 21-digit ID of your Google Account.
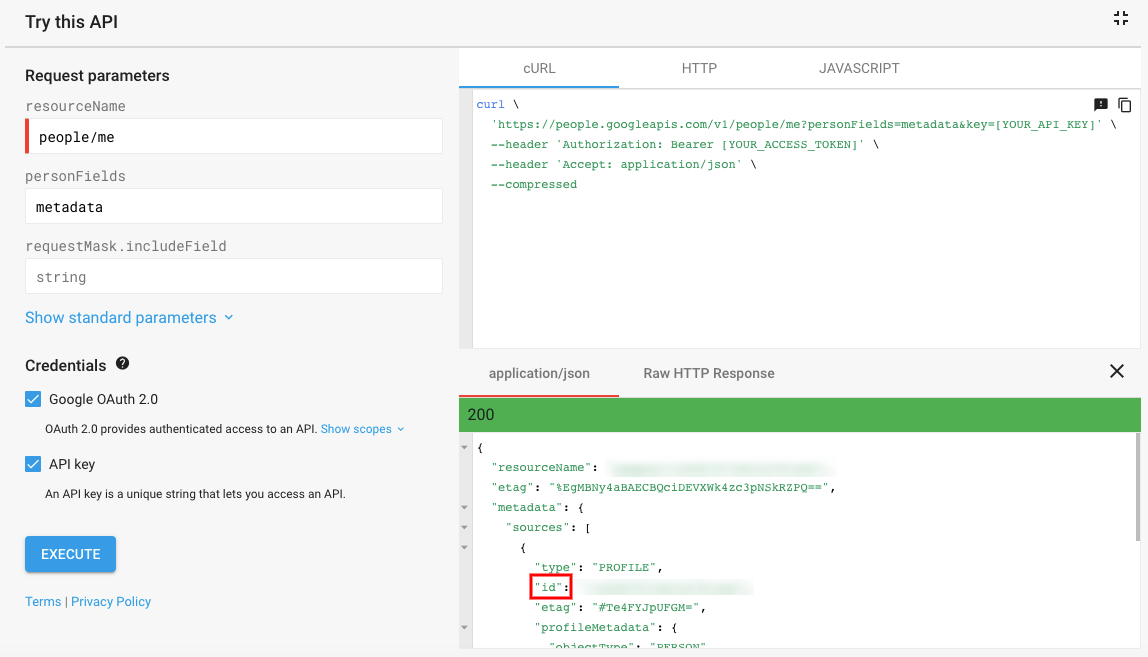
To find your Google Account ID:
- Click on this link.
- Under Request parameters, enter people/me under resourceName and metadata under personFields.
- Click on Execute.
- Login using your Google Account.
The 21-digit ID corresponding to id under application/json is your Google Account ID.
How to associate the policy to a device?
If the policy is not saved
- Go to Policy Targets > Click on Add Devices.
- Select the device to which the policy is to be associated > Click OK.
- Save the policy.
If the policy is already saved
- Check the required policy from the Policies tab.
- Click on Manage > Associate Targets.
- Select the device > Associate.
Apart from devices, policies can also be attached to device groups, domains, users and user groups.
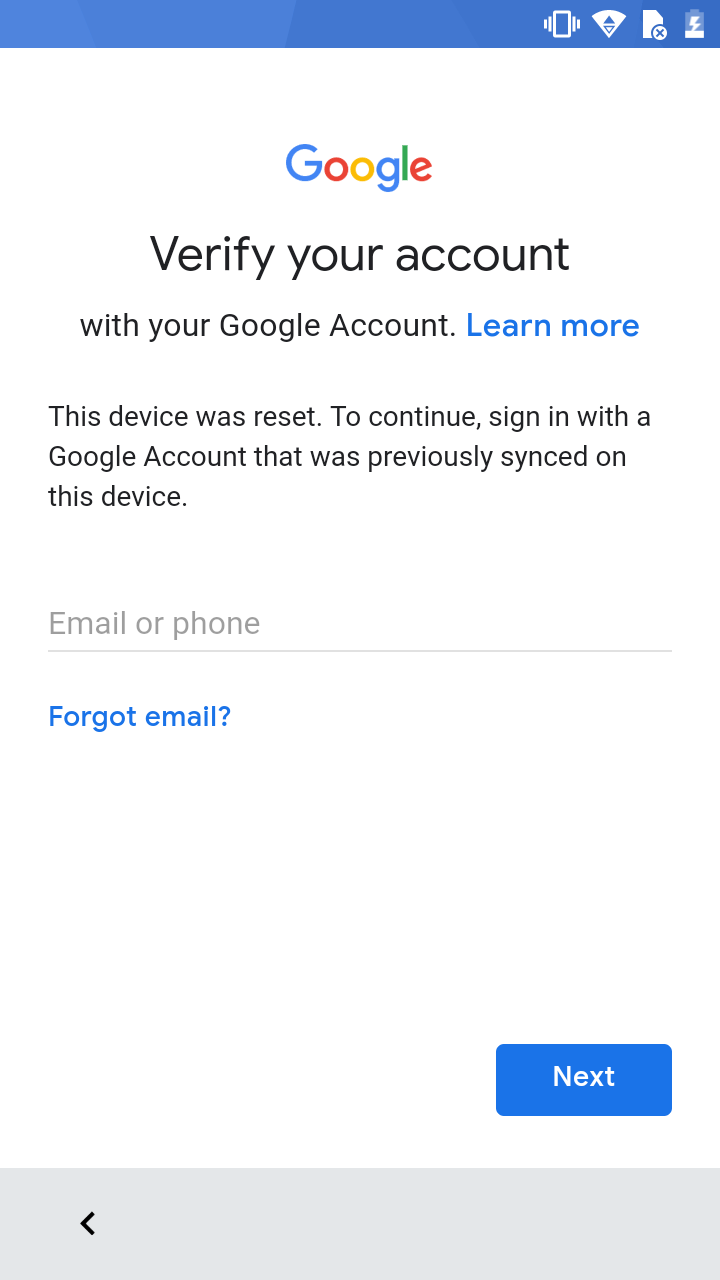
To securely bypass Factory Reset Protection using Hexnode UEM
Suppose you forget or don’t know the credentials of the Google Account configured on the device before reset, Hexnode provides you options to securely bypass the account verification step during the initial setup process. Use the credentials of the Google Workspace Account or Google Account ID added to the configured policy to bypass FRP.