Category filter
How to set up Wi-Fi for iOS devices?
Hexnode UEM allows administrators to remotely configure and push Wi-Fi network settings to iOS devices. This ensures devices connect to secure networks automatically without requiring manual user intervention or password disclosure.
Configuration Steps: iOS Wi-Fi Policy
To deploy Wi-Fi settings, follow these steps in the Hexnode UEM portal:
- Navigate to Policies: Go to the Policies tab.
- Create Policy: Navigate to New Policy > Create a fully custom policy.
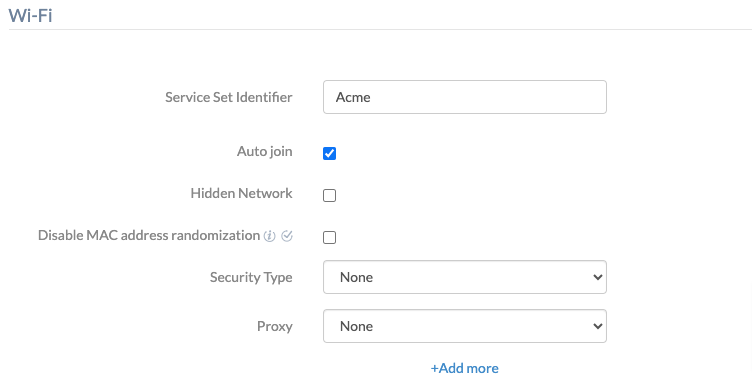
- Access Wi-Fi Settings: Navigate to iOS > Network > Wi-Fi and click Configure.
- Add Networks: You can configure multiple Wi-Fi networks within a single policy by clicking the +Add more button.
Wi-Fi Configuration Parameters
| Parameter | Description |
| Service Set Identifier (SSID) | The unique name of the Wi-Fi network. |
| Auto join | Allows the device to connect automatically when within range. (Default: Enabled) |
| Hidden Network | Enable this if the SSID is not broadcasting. (Default: Disabled) |
| Disable MAC address randomization | Disables MAC address randomization for the specific network. Note: Supported on iOS 14+. |
| Security Type | Defines the encryption method (e.g., WEP, WPA/WPA2, WPA3, Enterprise options). |
| Proxy | Configuration for network proxies (None, Manual, or Automatic). |
Network Security Types & Requirements
The configuration requirements vary based on the selected Security Type:
1. Open and Personal Networks
- None: Used for open Wi-Fi networks; no password required.
- WEP, WPA/WPA2, Any (personal), WPA2/WPA3, or WPA3: Admins must provide the Password. Users will join automatically without seeing or entering the credentials.
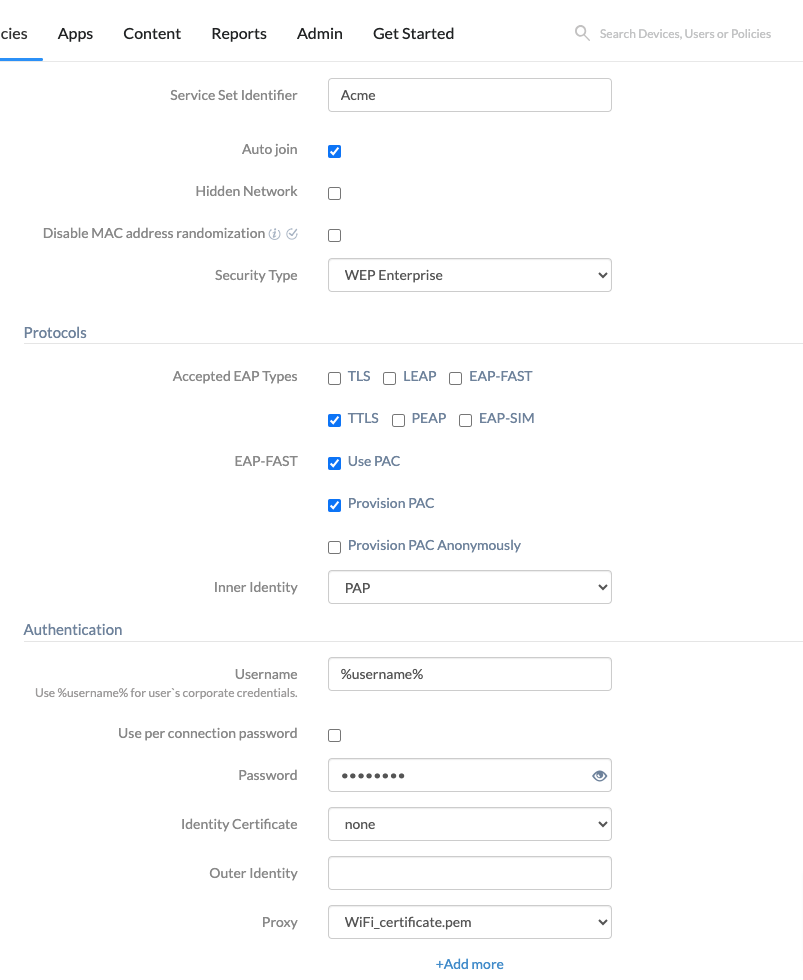
2. Enterprise Security Options (802.1X)
Used for Enterprise-grade security. Key options include:
| Option | Description |
| Accepted EAP types | TLS, LEAP, EAP-FAST, TTLS, PEAP, EAP-SIM. (TTLS is accepted by default). |
| Inner identity | (TTLS only) Authentication processes: PAP (default), CHAP, MS-CHAP, or MS-CHAPv2. |
| Username | Enterprise network username. Supports the %username% wildcard. |
| Identity certificate | SCEP or PKCS certificate profiles uploaded via Policies > Security > Certificates. |
Proxy Settings
- None: Default state. No proxy server is utilized.
- Manual: Requires Server, Port, and optional Authentication details.
- Automatic: Requires a Proxy PAC URL to the configuration file.
Policy Association and Deployment
- In the policy window, go to Policy Targets.
- Select Devices, Device Groups, Users, User Groups, or Domains.
- Choose the specific targets and click Save.
Expected Device Behavior
- Silent Connection: The Wi-Fi profile is pushed silently to the device.
- Automatic Connection: If “Auto join” is enabled, the device connects immediately when in range.
- Security: Users cannot view the stored Wi-Fi password in the device settings.
Frequently Asked Questions (FAQs)
- Can multiple Wi-Fi networks be configured in a single policy?
Yes. By clicking the +Add more button, multiple SSIDs can be added to a single policy for seamless transitions between office locations.
- Is it possible to prevent users from seeing the Wi-Fi password?
Yes. Credentials are encrypted within the configuration profile. The user can connect, but the password remains hidden.
Troubleshooting
| Issue | Resolution |
| Fails to connect to hidden network | Ensure the Hidden Network checkbox is enabled in the policy. |
| Enterprise (802.1X) fails | Verify that the SCEP/PKCS certificate is valid and the Root CA is trusted. |
| “Unable to join network” error | Confirm the Security Type matches the router’s actual configuration. |