Category filter
Disable macOS App Store using configuration profile
The App Store offers a convenient way for users to discover, download, and install applications on their Apple devices. Organizations looking to implement strict application management and maintain accurate application compliance on macOS devices can choose to disable the App Store. Disabling the App Store helps manage unauthorized app installations, possibly reducing distractions from non-essential applications for users in an organization. This document provides a way to disable the macOS App Store using a configuration profile. IT administrators can deploy this configuration profile using Hexnode’s Deploy Custom Configuration feature.
Disable App Store
The following configuration profile uses the restrict-store-softwareupdate-only key to disable App Store on a macOS device. This key supports two input values:
true – To disable the App Store.
false – To enable the App Store.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
<?xml version="1.0" encoding="UTF-8"?> <!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" http://www.apple.com/DTDs/PropertyList-1.0.dtd> <plist version="1.0"> <dict> <key>PayloadContent</key> <array> <dict> <key>PayloadDisplayName</key> <string>App Store settings</string> <key>PayloadIdentifier</key> <string>com.apple.appstore.CE39D334-09A8-4D3C-B227-D32E14AFC941</string> <key>PayloadType</key> <string>com.apple.appstore</string> <key>PayloadUUID</key> <string>CE39D334-09A8-4D3C-B227-D32E14AFC941</string> <key>PayloadVersion</key> <integer>1</integer> <key>restrict-store-softwareupdate-only</key> <true/> </dict> </array> <key>PayloadDisplayName</key> <string>App Store disable</string> <key>PayloadIdentifier</key> <string>MacBook-Air.89A4DD0D-AC3D-4237-ADFE-717CEEE1F921</string> <key>PayloadType</key> <string>Configuration</string> <key>PayloadUUID</key> <string>89A4DD0D-AC3D-4237-ADFE-717CEEE1F921</string> <key>PayloadVersion</key> <integer>1</integer> </dict> </plist> |
What happens at the device end?
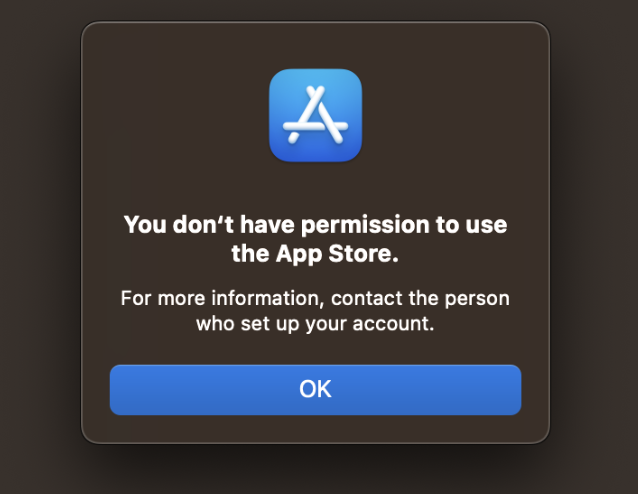
Upon successful installation of the configuration profile on a macOS device, the App Store will be disabled and inaccessible to the user. When a user attempts to access the App Store, they will be shown an error message stating, “You don’t have permission to use the App Store”.