Loved by all. Recognized by the best.
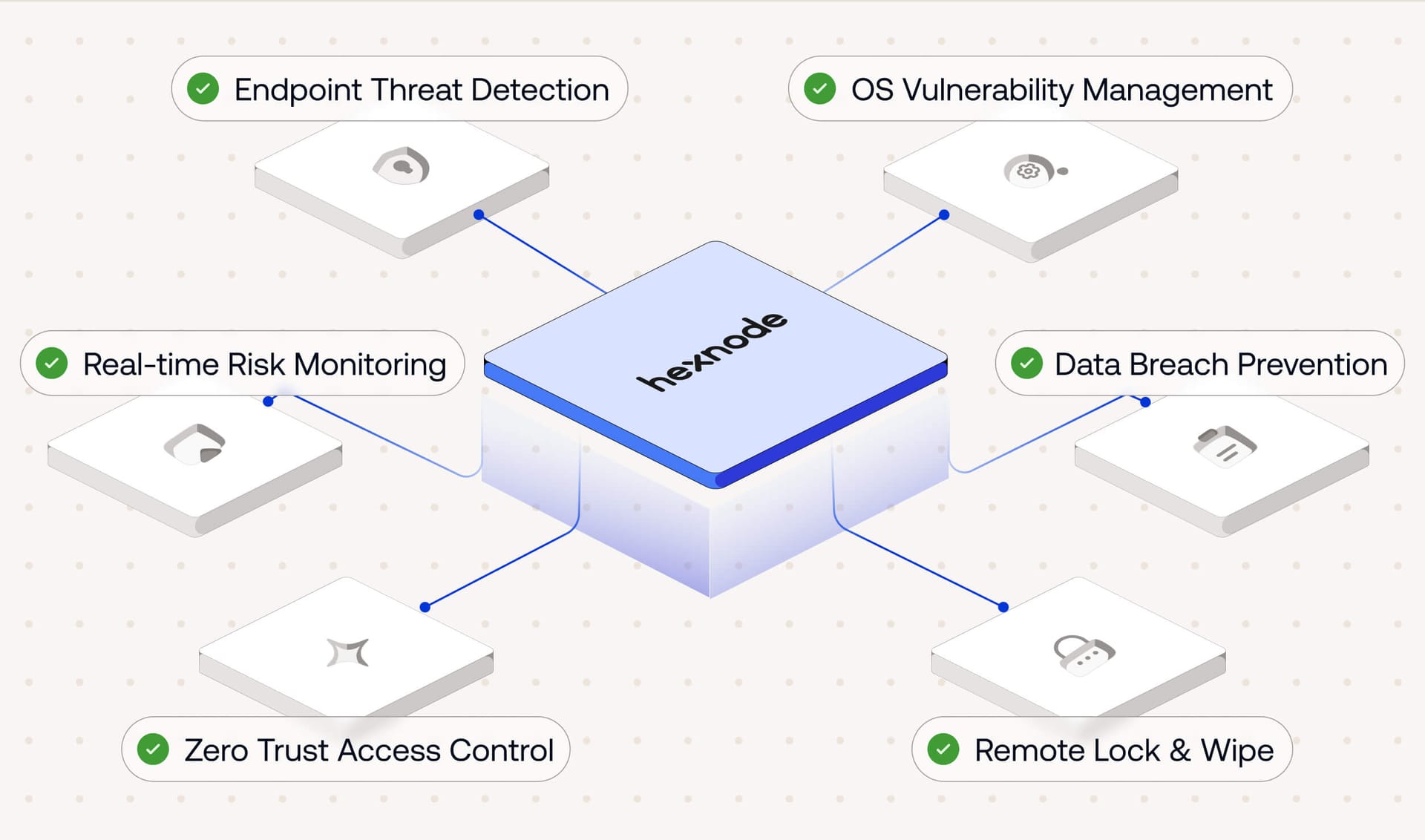
Reduce risk by preventing attacks at the source

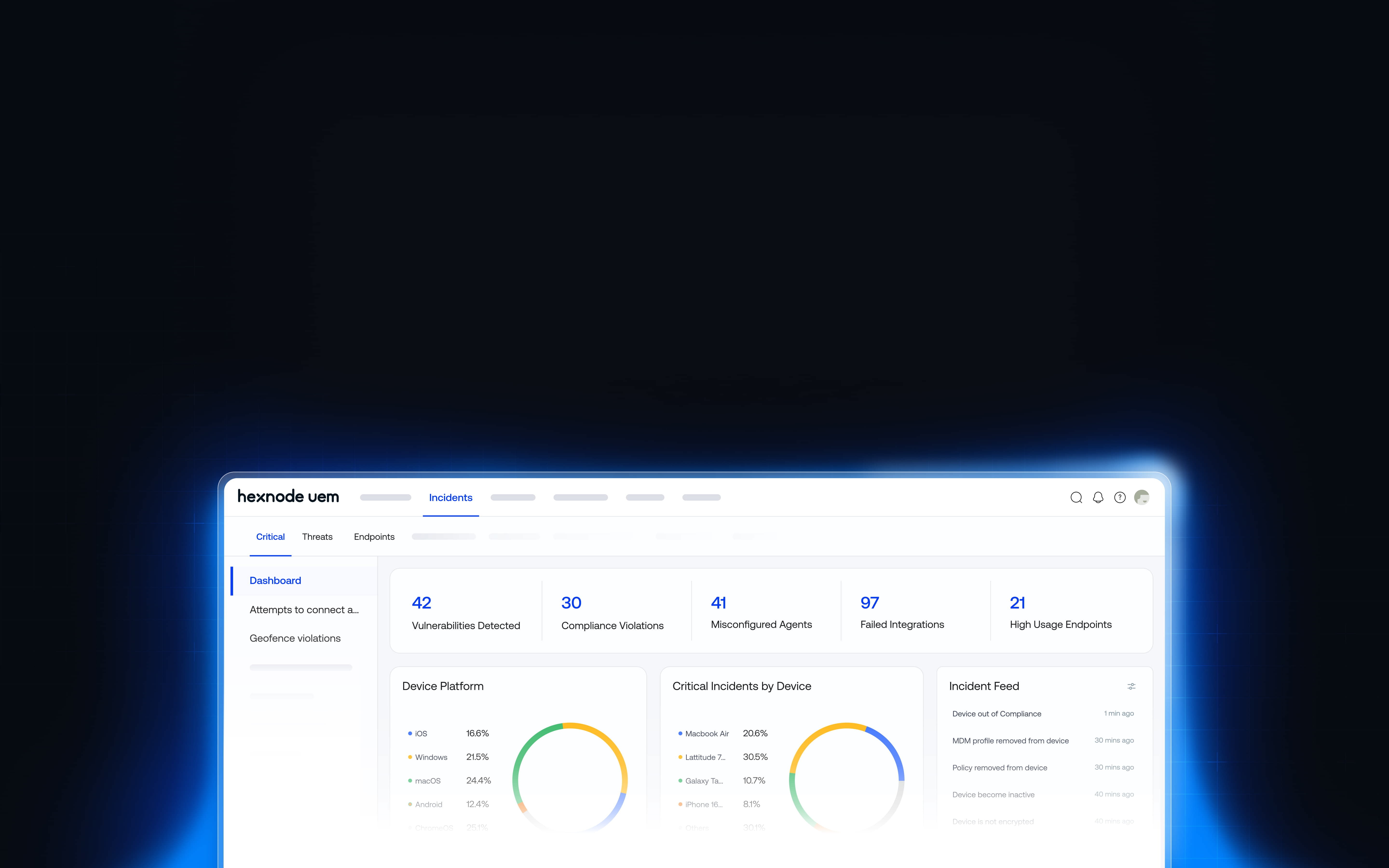
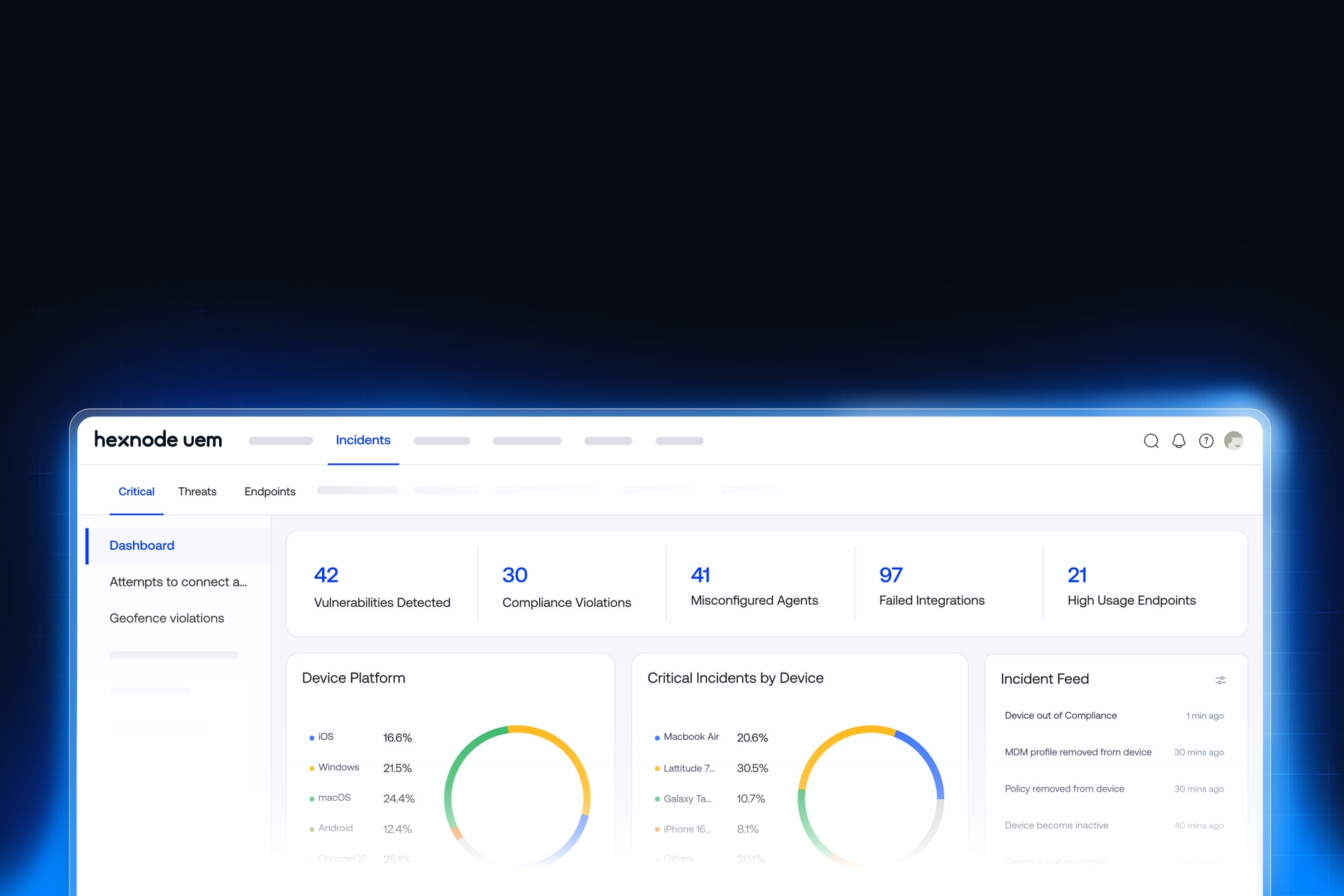
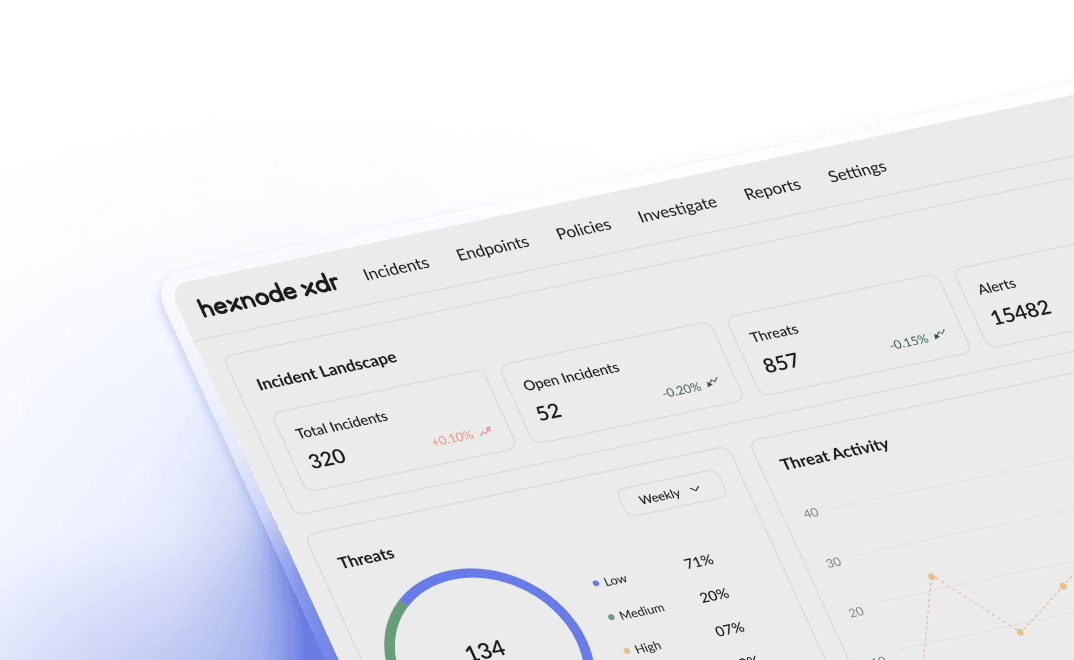
Complete endpoint security with Extended Detection & Response
Correlate signals from devices, apps, and integrations with Henode XDR to uncover attacks in advance that traditional tools miss. Paired with Hexnode UEM, it equips your endpoints and device groups to contain and resolve complex security risks instantly.
Features that keep your devices safe
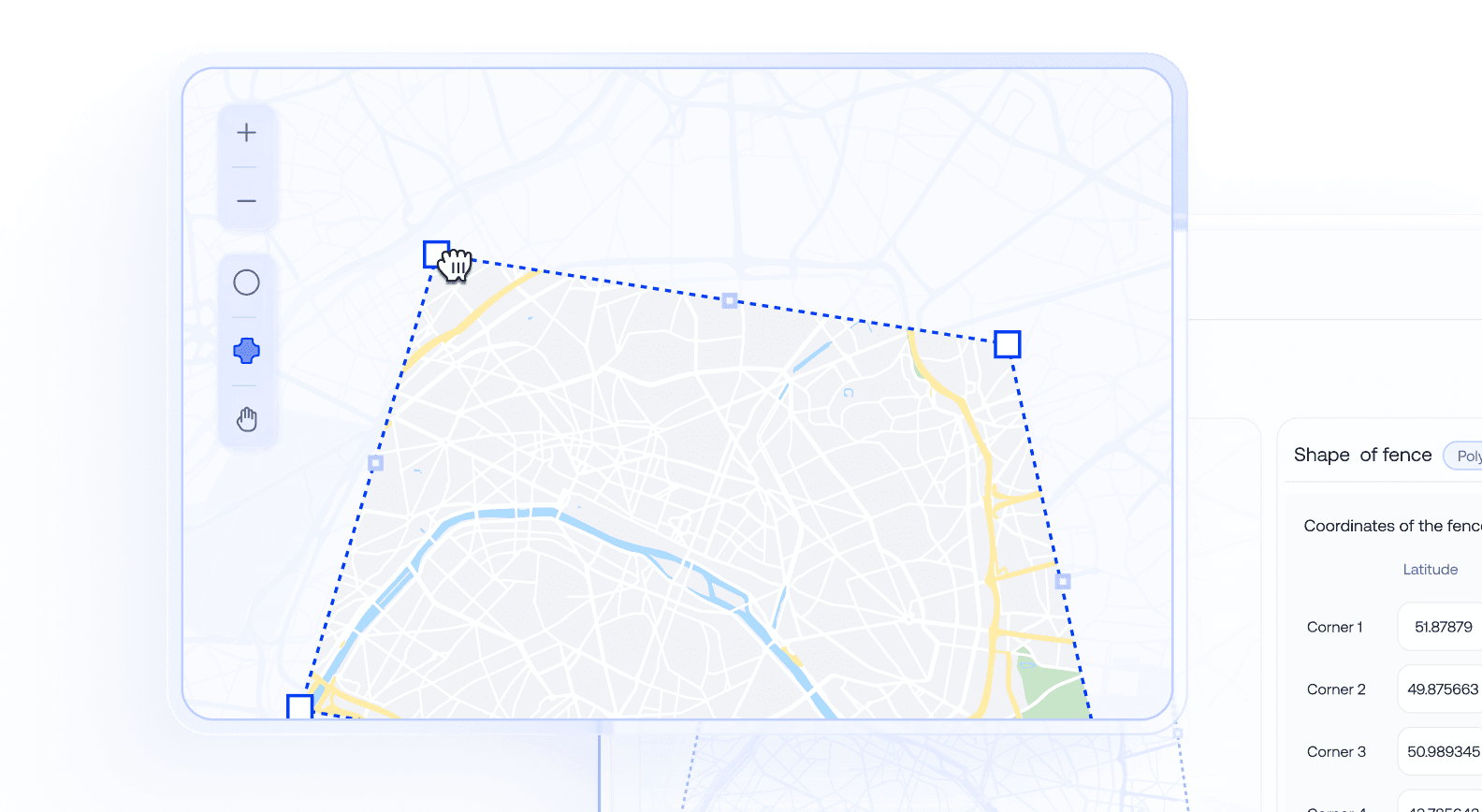
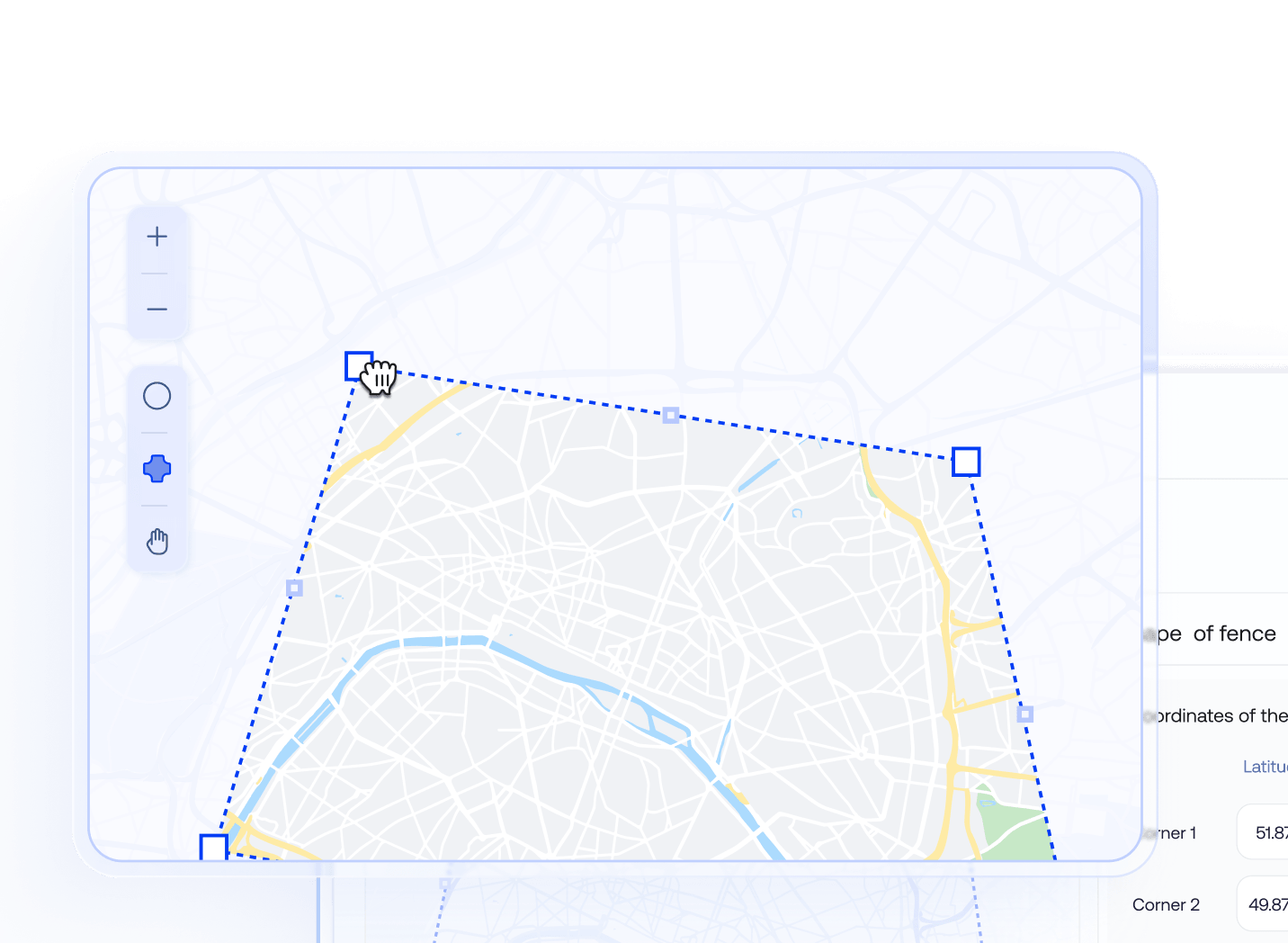
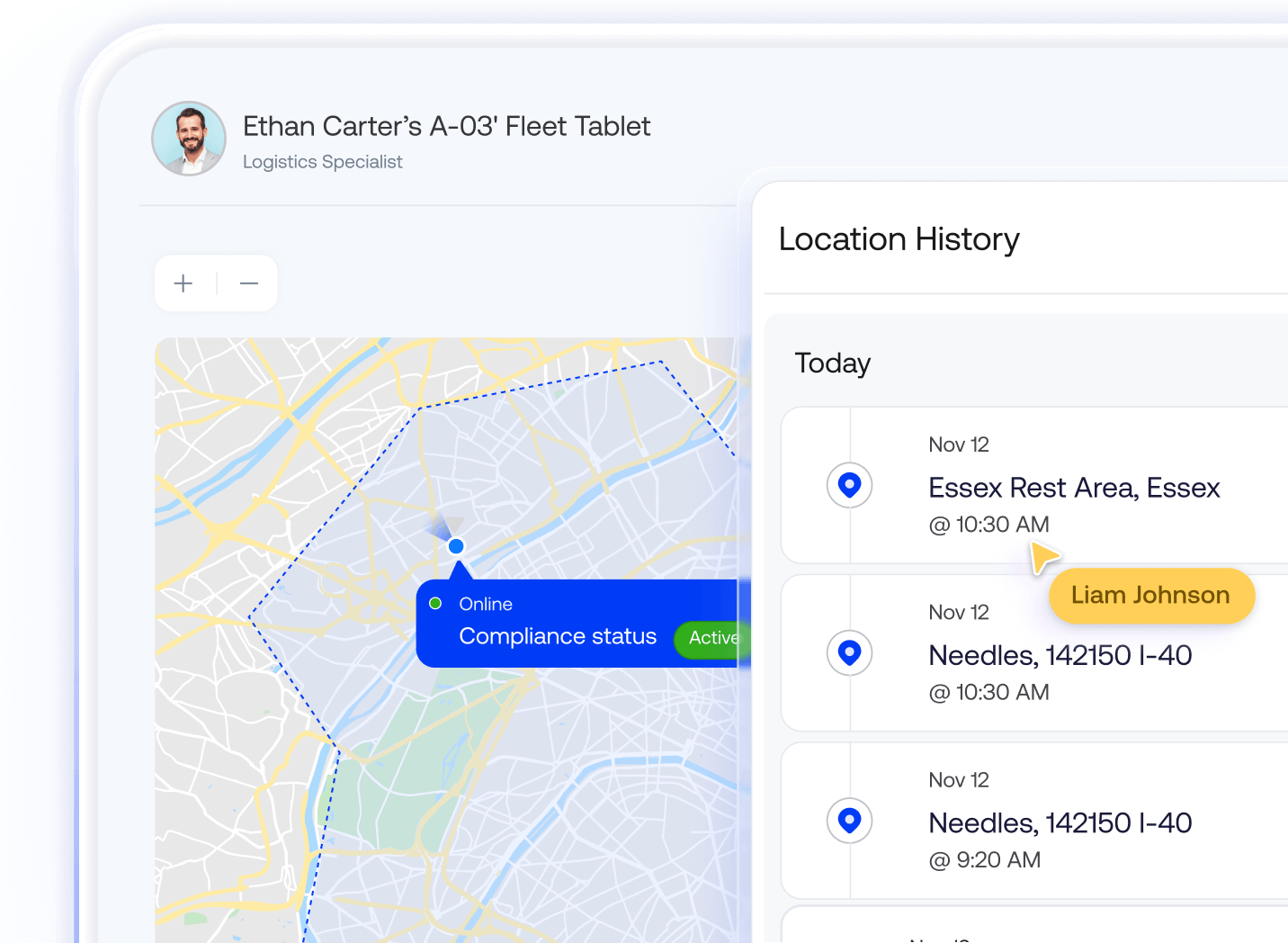
Custom geofencing
Build precise, custom-shaped geofences directly from the Hexnode console using a simple UI. Devices entering or leaving a zone can be dynamically assigned to groups, triggering pre-defined policies the moment devices enter or leave a geofence.
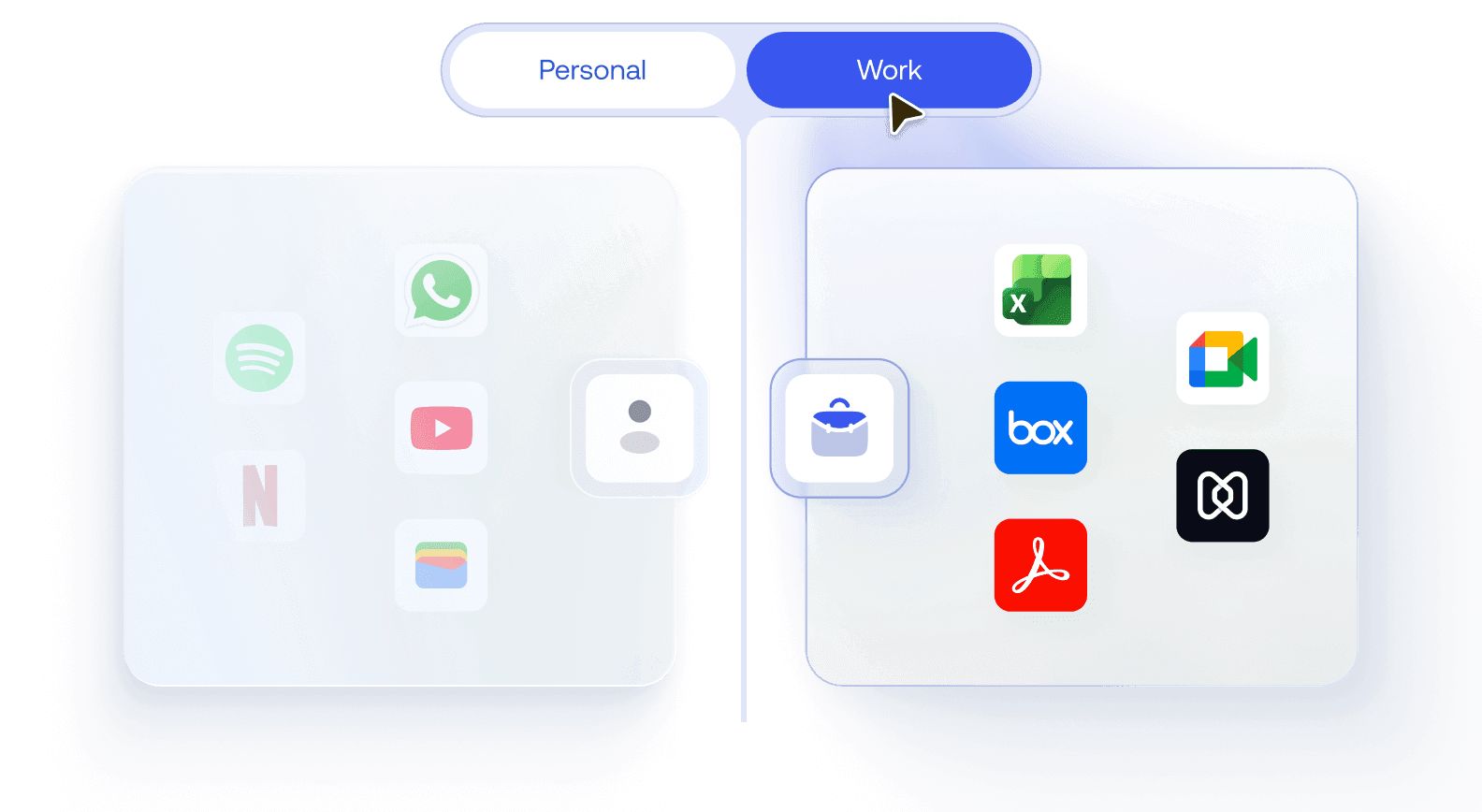
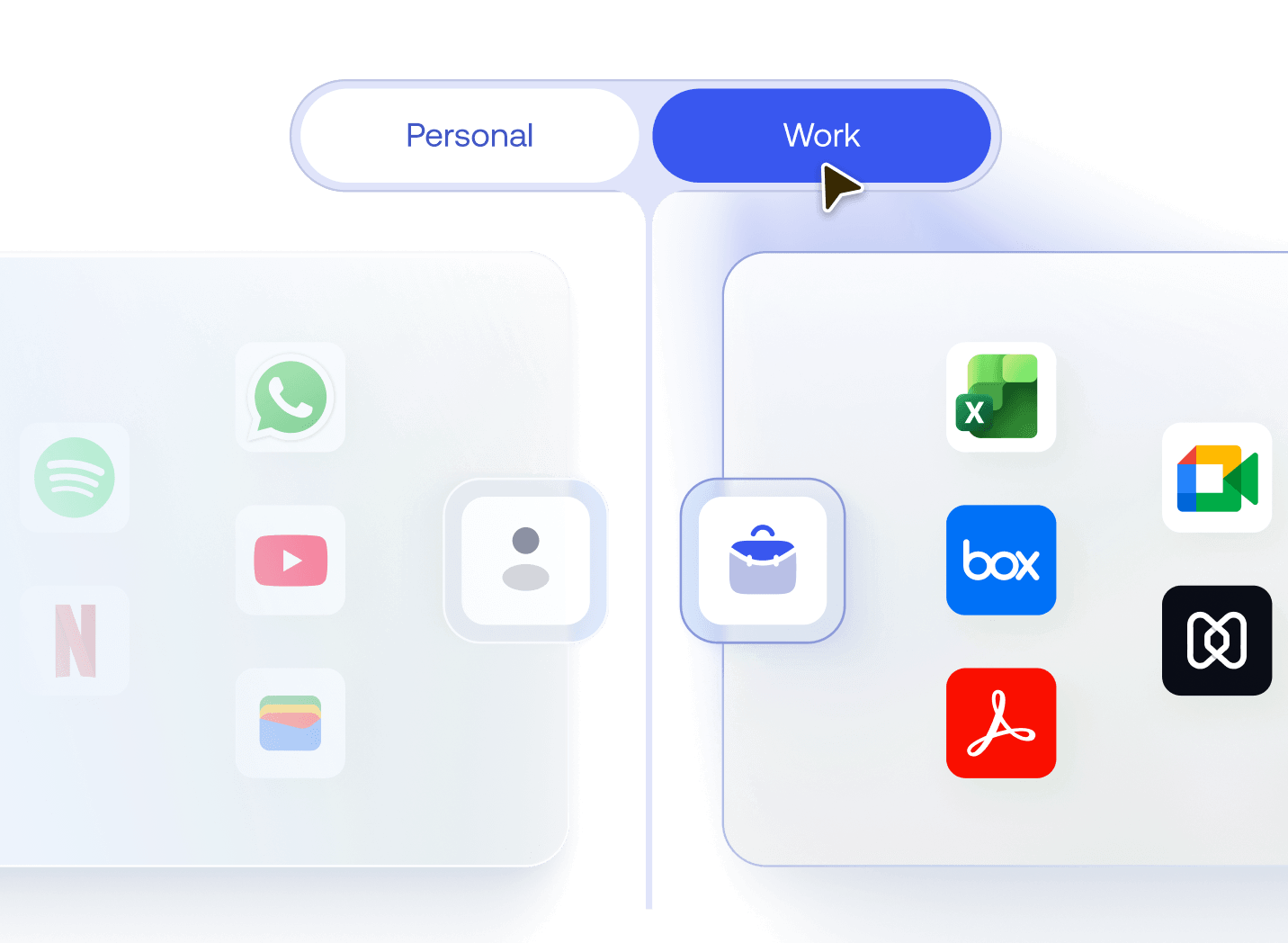
Containerization
Isolate corporate apps and data from personal use on BYOD or shared devices using containerisation. Enforce policies like Open-In restrictions and managed domains, ensuring corporate data never mixes with unmanaged apps or storage.
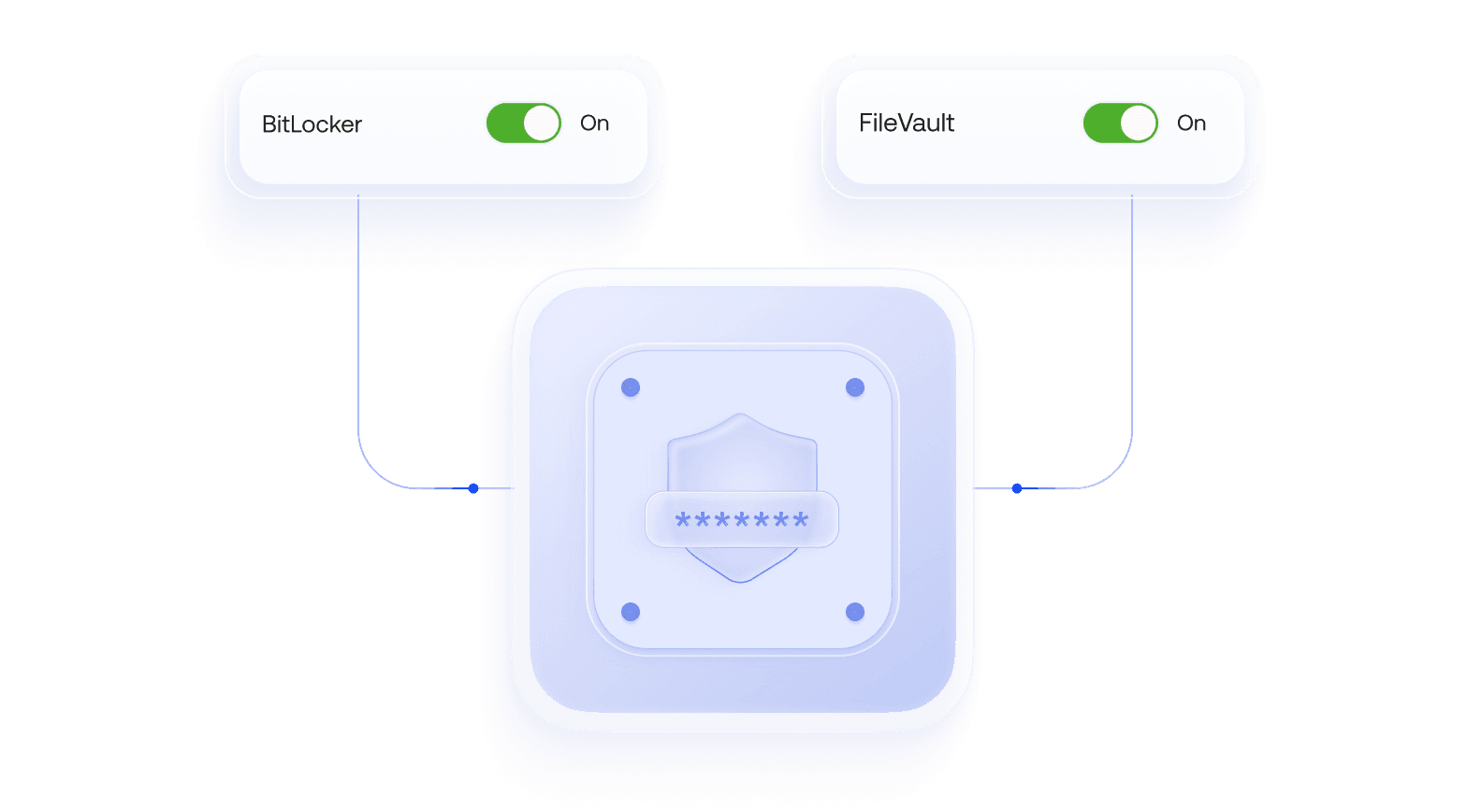
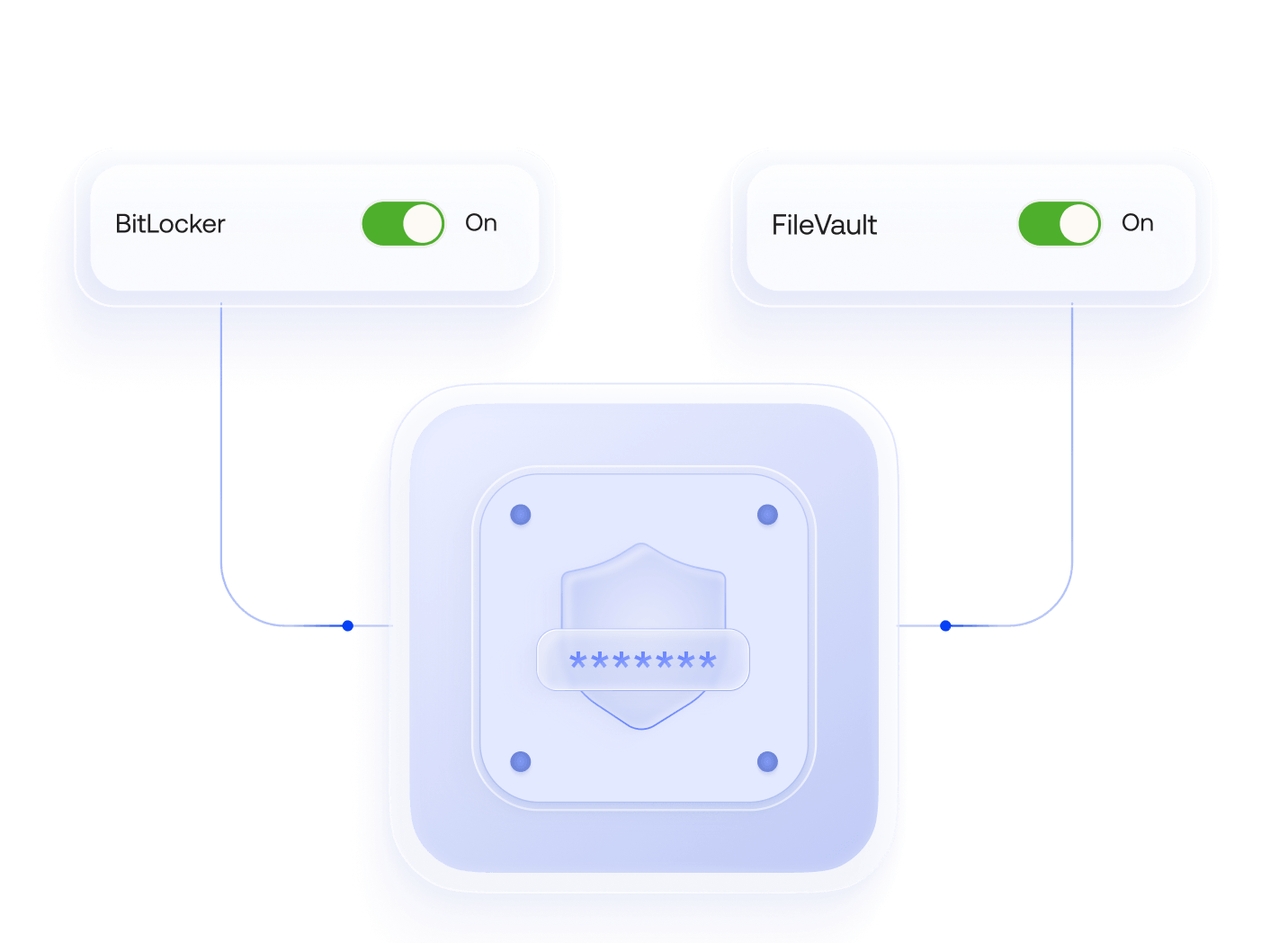
Encryption & password policies
Enforce full-disk encryption with BitLocker on Windows and FileVault on macOS, and require strong device passcodes across platforms. Safeguard data at rest and ensure only authorized users can access corporate devices.
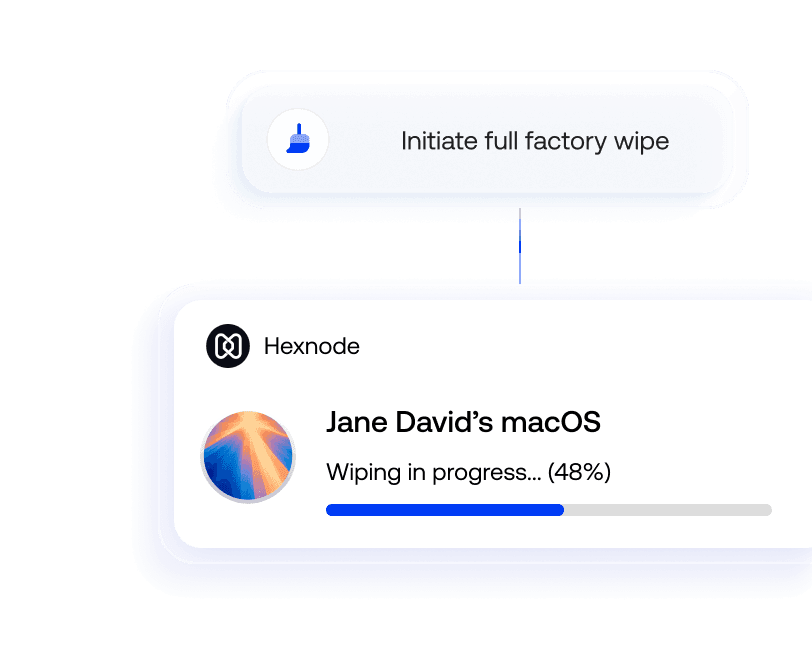
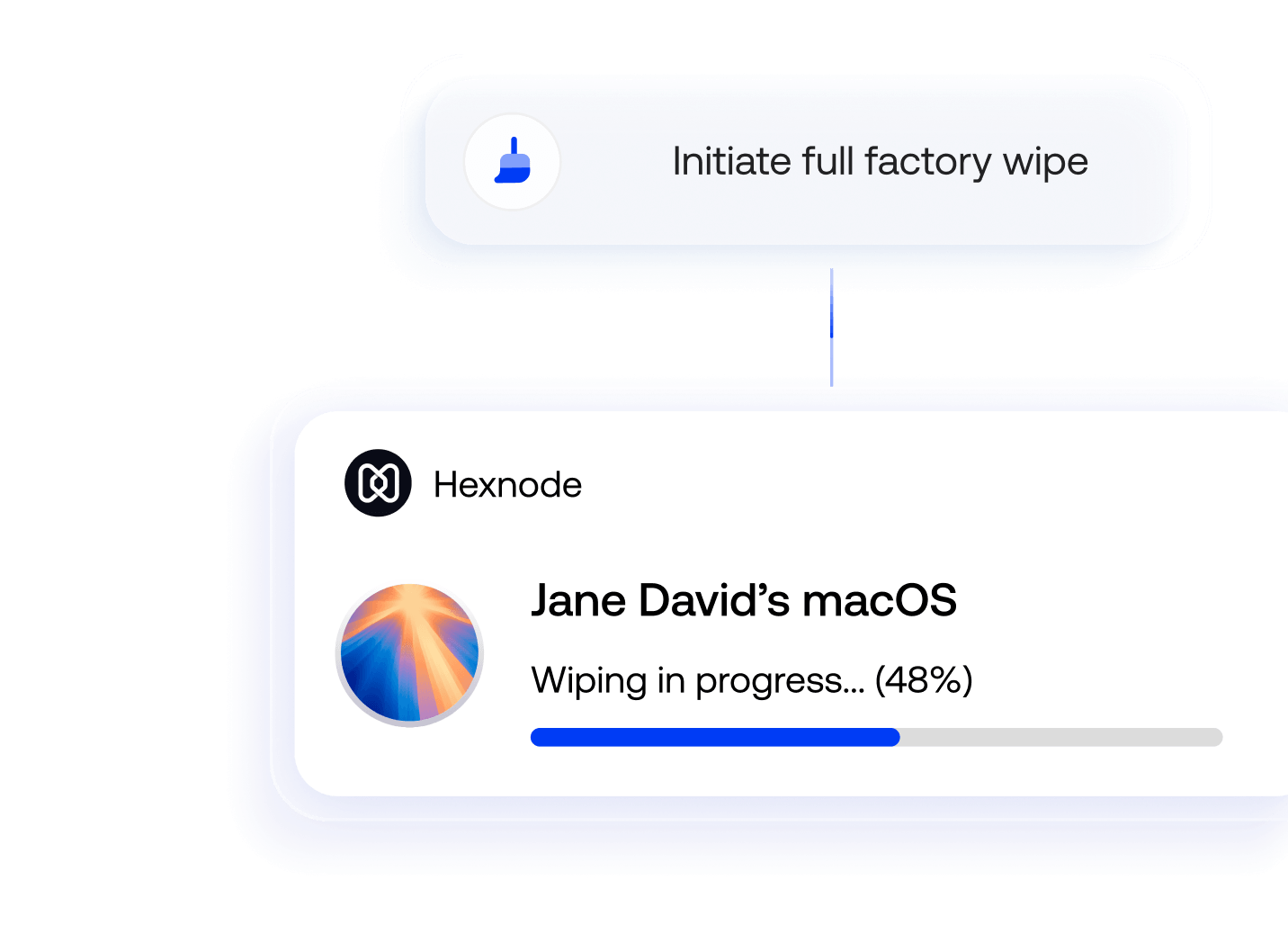
Remote lock & wipe
Instantly lock a lost device or trigger a full factory wipe from the Hexnode portal. Admins can choose between a selective wipe of corporate data or a complete device reset based on device ownership.
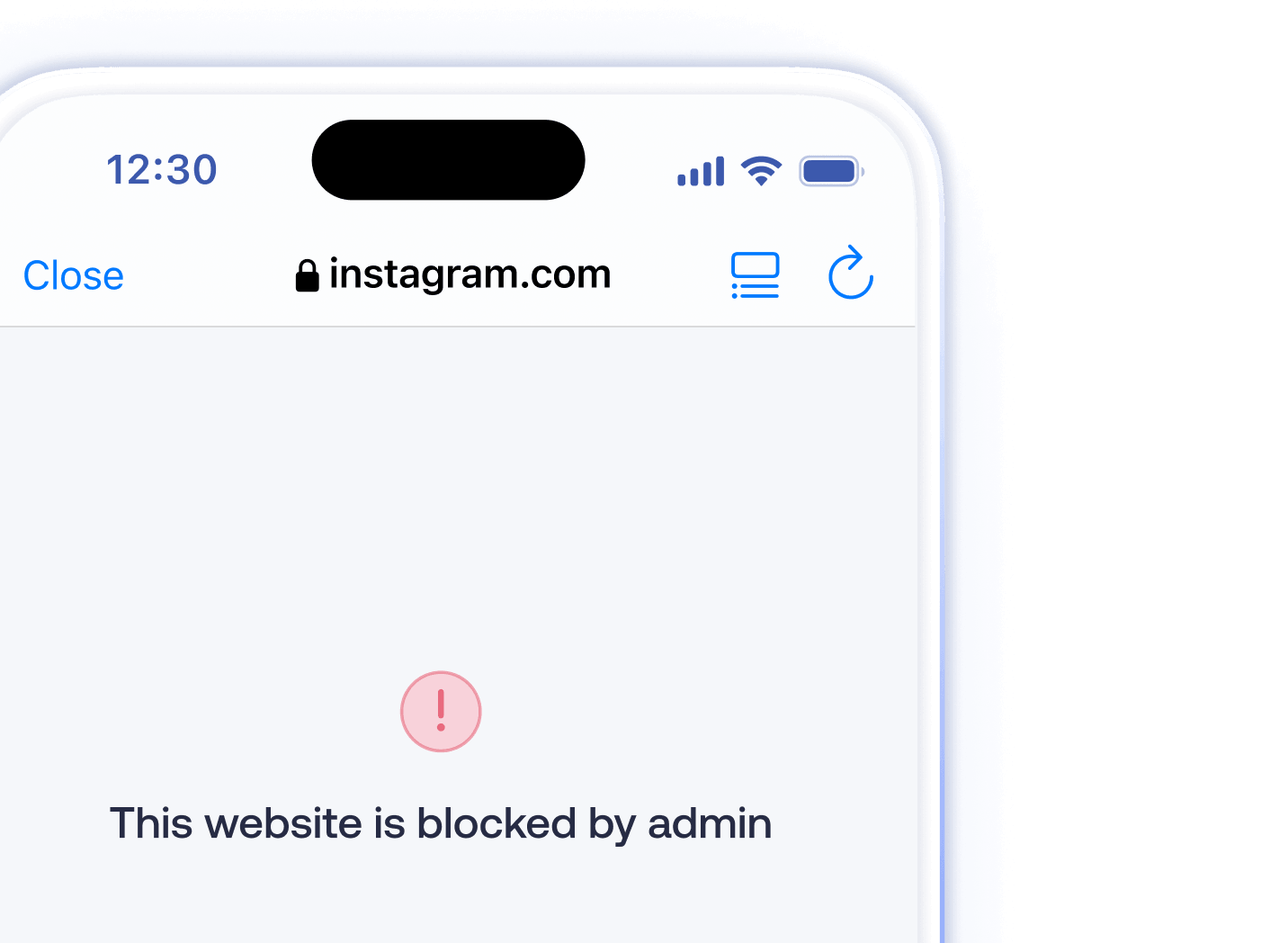
Secure web browsing
Restrict browsing to trusted domains and block unsafe sites with web content filtering and Hexnode’s kiosk browser. You can blocklist and allowlist URLs, and lock devices down to web-based kiosk mode.
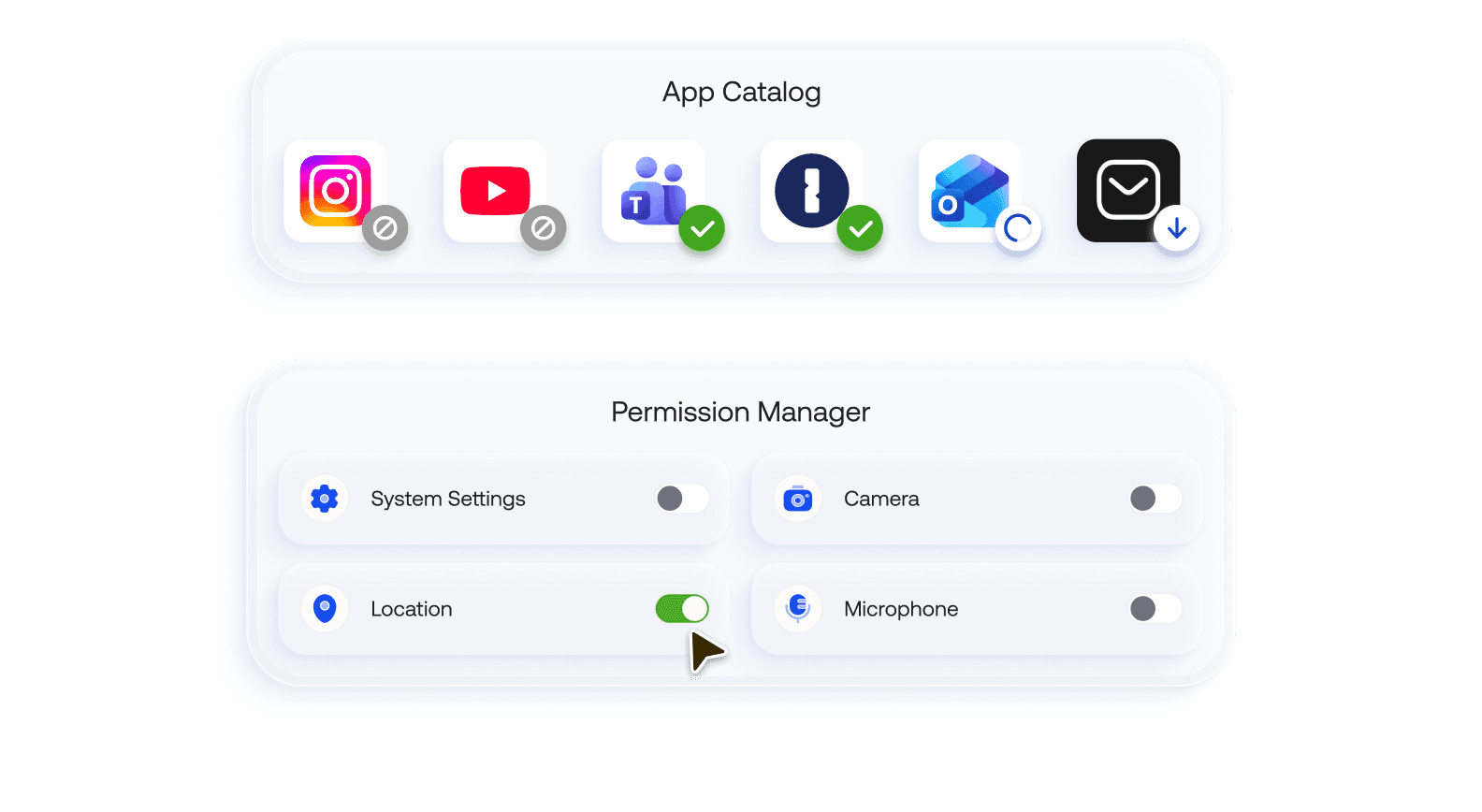
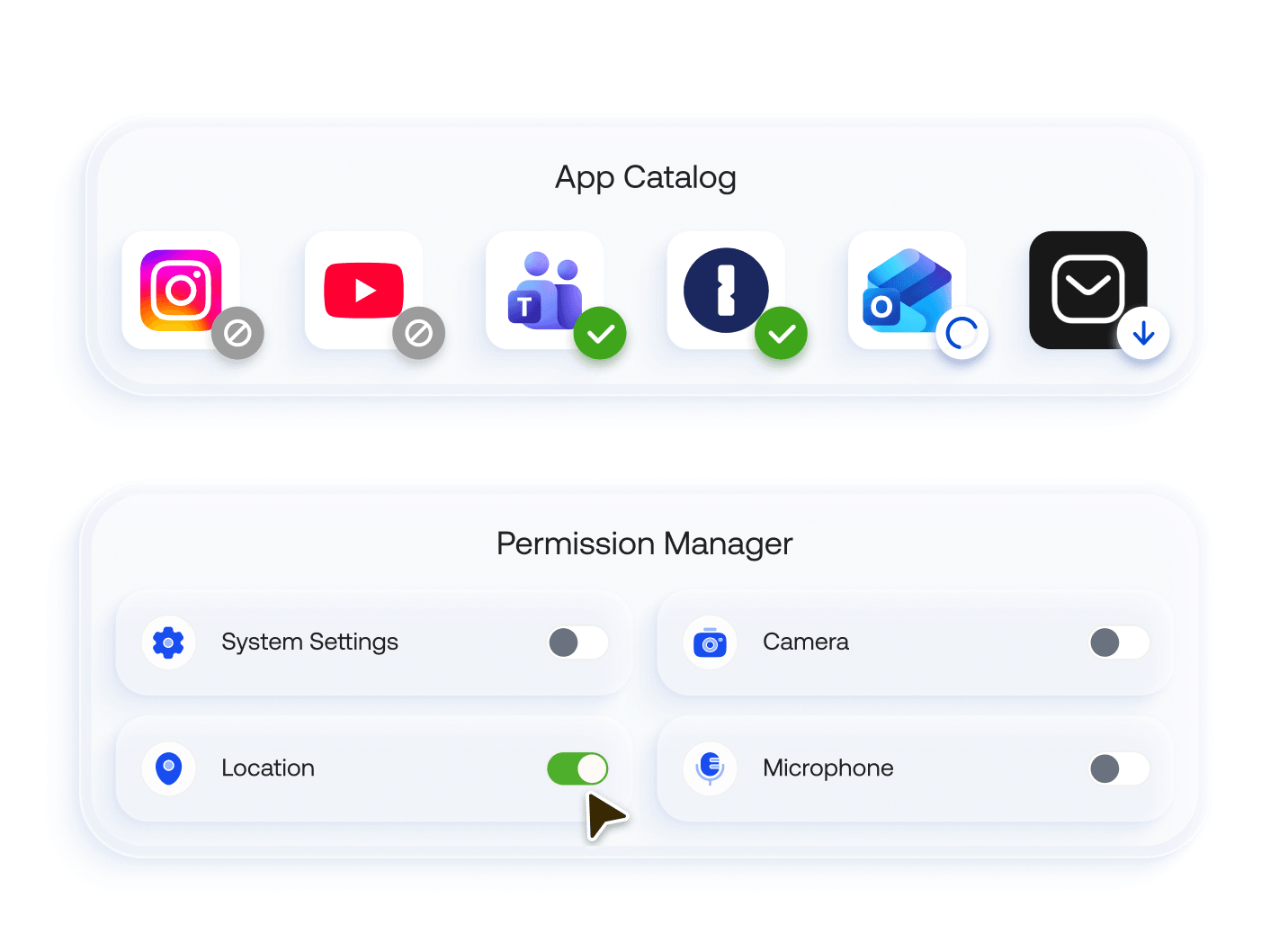
App and content security
Manage which apps your users can install, and restrict permissions like location, microphone, or camera. Use work containers, managed domains, and Open-In policies to separate corporate and personal data and block data loss through unmanaged apps or cloud sync.
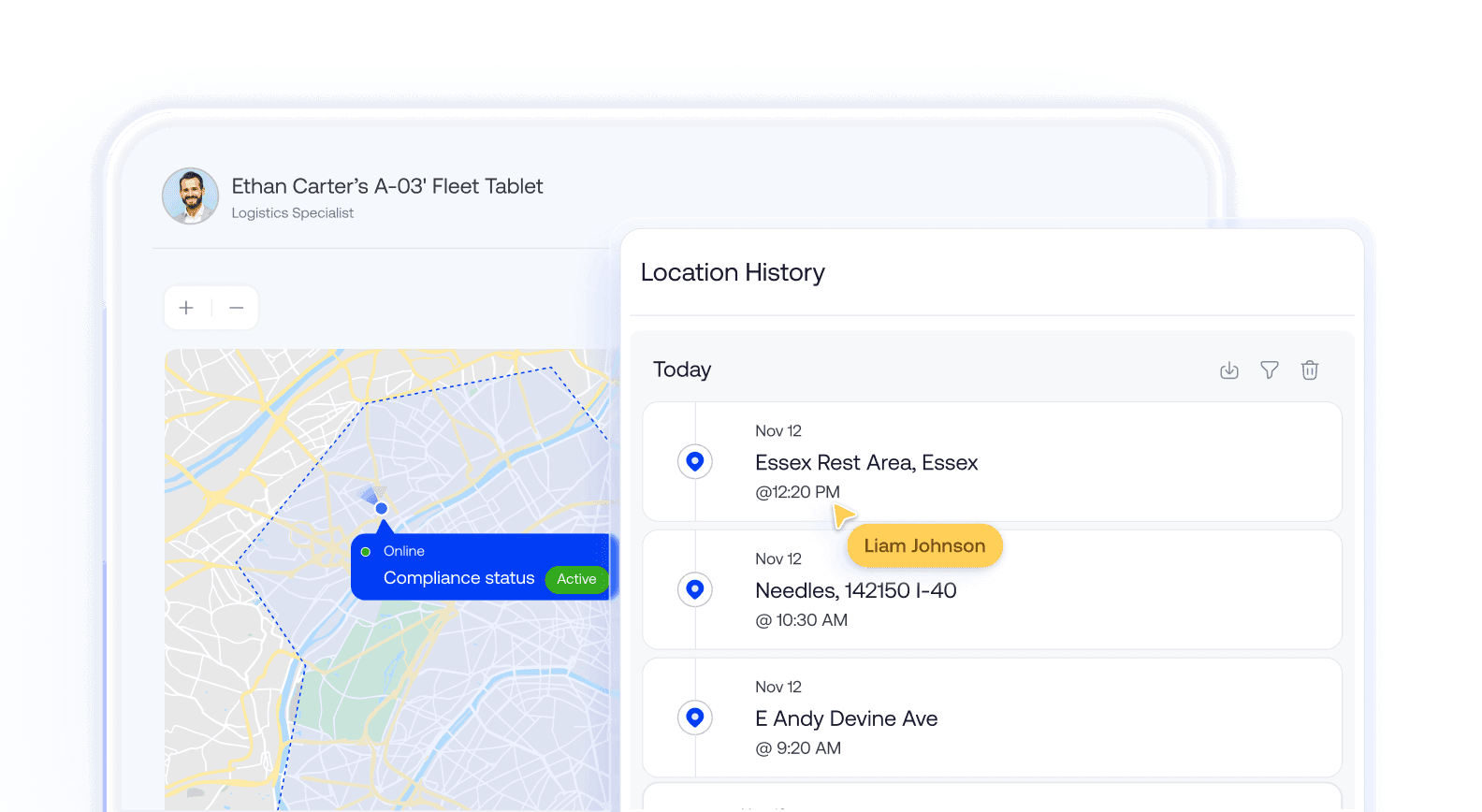
Real time location tracking
Track device locations in real time and view location history logs. Hexnode’s location tracking features help recover lost devices and validate compliance with location-based policies.

14 day free trial
No credit card