Category filter
Manage Windows Update Preferences and Settings from Hexnode UEM
Learn how to manage Windows Updates Preferences and Settings with Hexnode. The Windows Update Preferences policy allows administrators to manage and configure Windows Updates, ensuring efficient handling of OS updates and maintaining performance across all devices. This feature consists of various options that help to set the network constraints for updates, the capability to defer updates, the option to specify targeted products and versions, and the option to configure the update channel. The configurations for the major updates from Microsoft, that includes Feature Updates and Quality Updates, can be setup using this feature. While Feature Updates introduce new features, visual changes, and security enhancements to devices, Quality Updates are minor and do not include new features. Instead, Quality Updates focus on addressing bugs, and errors, and improving reliability and security. With Hexnode UEM’s Windows Update Preferences policy, administrators can manage Windows updates settings and preferences.
How to manage Windows updates settings and preferences?
The following steps will guide you on how to manage Windows Update settings from Hexnode UEM.
- Log in to your Hexnode UEM portal. Navigate to the Policies tab. Click on New Policy to create a new one. Enter the Policy Name and Description in the provided fields. Or click on any policy to edit an existing one.
- Navigate to Windows. Select Windows Update Preferences under Patches & Updates.
- Click on Configure to manage Windows update settings.
Windows Update Preferences
There are various options in the Windows Update Preferences policy that will help you manage Windows Updates settings in your organization. Let’s discuss each option in depth.
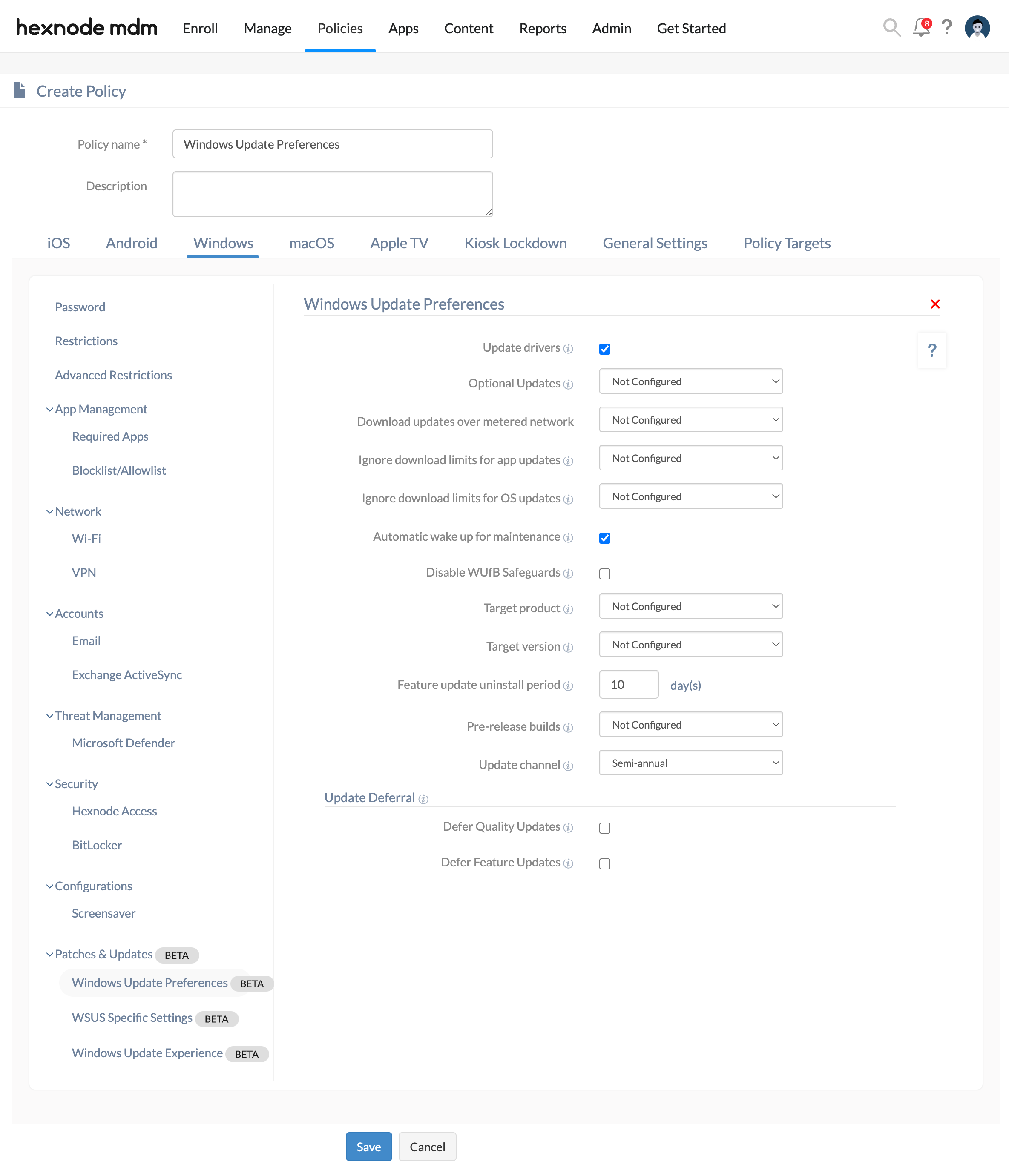
Update drivers
Check this option to include updates that have a driver classification along with the Windows Quality Updates. By default, this option is enabled. If not enabled, Windows Updates will not include updates that have a driver classification.
Optional Updates
Optional updates are part of regular device maintenance, including non-security updates, features, or improvements that do not affect the functionality or security of a device. Admins can choose to install these updates based on their preferences. The default setting for this option is “Disabled” if it is not configured.
| Settings | Description |
|---|---|
| Disabled (default) | The device will not receive any Optional Updates. |
| Automatically receive Optional Updates | The device will only get optional cumulative updates automatically, in line with the quality update deferrals. |
| Automatically receive Optional Updates (including CFRs) | The device will get the latest Optional Updates automatically in line with the configured quality update deferrals. This includes optional cumulative updates and gradual feature rollouts (CFRs). |
| Users can select which Optional Updates to receive | Users can select which Optional Updates to get by navigating to Settings > Windows Update > Advanced options > Optional Updates on the device. |
Download updates over metered network
Allows users to decide how updates are downloaded when the device is connected to a metered network (cellular data). The default setting for this option is “Disallowed” if it is not configured.
| Settings | Description |
|---|---|
| Allowed | Allows the download of updates over metered networks. |
| Disallowed (default) | Prevents the download of updates over metered networks. |
Ignore download limits for app updates
This option specifies whether to ignore the download limit (allow unlimited downloading) over a cellular network for apps and their updates. These download limits are controlled by external policies imposed by mobile operators. The default setting for this option is “Don’t Ignore” if it is not configured.
| Settings | Description |
|---|---|
| Ignore | Imposes no download limits for apps and their updates over the cellular network.
|
| Don’t Ignore (default) | Restricts users from downloading apps and their updates over cellular data. |
Ignore download limits for OS updates
This option specifies whether to ignore the download limit (allow unlimited downloading) over a cellular network for Windows OS updates. These download limits are controlled by external policies imposed by mobile operators. The default setting for this option is “Don’t Ignore” if it is not configured.
| Settings | Description |
|---|---|
| Ignore | Imposes no download limits for OS updates over the cellular network.
|
| Don’t Ignore (default) | Restricts users from downloading OS updates over cellular data. |
Automatic wake up for maintenance
Automatic Maintenance is a feature that performs various background maintenance tasks to keep the system running smoothly. These maintenance tasks are designed to run when the device is not in use. By default, this option is enabled.
Check this option to activate the automatic maintenance wake-up feature. This will send a wake request to the OS daily for the scheduled maintenance.
Unchecking this option will apply the settings configured in the Security and Maintenance or Automatic Maintenance under the Control Panel on the device end.
Disable WUfB Safeguards
WUfB Safeguard prevents the release of a new OS version to a device that has a known compatibility issue. The update will only be provided once the issue is fixed and verified on the device. Safeguards aim to protect the device and user from a failed or poor update experience. By default, the WUfB option is enabled.
Target product
Let the administrators choose which product they want their devices to switch to or remain on until the product reaches the end of service. Enter the product name as listed on the Windows Update target version page.
Admin can choose either of the options from Windows 10, Windows 11, or the “Other” option. If the “Other” option is selected, then specify a valid product name. For example, specify the name as 11 or Windows 11. The device will request the specified Windows Update product in subsequent scans. If no product is specified, the device will continue receiving newer versions of the Windows product it is currently on.
Target version
Let the administrators choose which product version they want their devices to switch to or remain on until the specified version reaches the end of service. Enter the product version as listed on the Windows Update target version page. The device will request the specified Windows Update product version in subsequent scans. If no product version is specified, the device will continue receiving newer versions of the Windows product it is currently on.
Feature update uninstall period
Use this option to configure a time (in days) after which Feature Updates can’t be uninstalled. After this period, the device can no longer roll back to the previous updated version. The value can be chosen between 2-60 days (by default, it is set to 10 days).
Pre-release builds
Select this option to configure how the pre-release build is distributed. Windows Update won’t offer any pre-release updates if this option is not configured; instead, such content will be received once it is released to the public.
| Settings | Description |
|---|---|
| Disabled | The device will not get any pre-release builds. |
| Disabled once the next release is public | Prevent the pre-release builds from installing once the next release is public. |
| Enabled | The device will get pre-release builds. |
| Users can choose (default) | The users have the flexibility to decide whether they want to participate in the Windows Insider Program and they can choose pre-release builds. |
Update channel
Select this option to configure which update channel a device receives its updates from. By default, this is set to the “Semi-annual” option and the admin can choose either of the options from the following:
- Canary
- Windows Insider – Fast
- Windows Insider – Slow
- Windows Insider – Release Preview
- Semi- annual (default)
- Release Preview – Quality Updates only
Update Deferral
This option lets the admin choose how many days to defer an update once it is released. During the deferral period, the device will not receive the updates following their release from Microsoft.
Defer Quality Updates
Check this option to enforce Quality Updates deferral. The Quality Update fixes and improves the existing Windows functionality. You can choose the deferral period after checking this option. The deferral period for Quality Updates is 30 days, i.e., the admin can defer the Quality Updates for up to 30 days.
Defer Feature Updates
Check this option to enforce Feature Updates deferral. The Feature Update contains the newest version of Windows OS. You can choose the deferral period after checking this option. The deferral period depends on the Update channel selected.
Apply the policy to devices/groups to manage Windows updates settings
There are two ways by which you can associate the policy to manage Windows updates settings with devices.
If you haven’t saved the policy yet,
- Navigate to Policy Targets.
- Click on + Add Devices, search and select the required device(s) to which you need to apply the policy. Click OK.
- Click on Save to apply the policies to the devices.
If you’ve already saved the policy and taken to the page which displays the policy list,
- Select the required policy.
- Click on Manage and select Associate Targets.
- Search and select the devices/ users/ device groups/ user groups/ domains to which you need to apply the policy.
- Click Associate.
Related topic
Frequently Asked Questions
1. Can the “Target Version” setting be used to downgrade a device to an earlier Windows build?
No. The Target Version setting is designed to lock a device to a specific version. It cannot be used to perform a downgrade or rollback to a version lower than what is currently installed on the hardware.
2. What happens if the specified “Target Version” reaches its End of Service (EoS)?
If the specified version reaches EoS, the device will ignore the target version constraint and resume receiving the next available stable updates to ensure the security of the operating system. The admin should monitor Microsoft’s lifecycle dates to update the policy accordingly.
3. Does “Download updates over metered network” setting apply to Wi-Fi connections?
Yes. If a Wi-Fi network or hotspot is toggled as a Metered connection in the device’s local network settings, Windows will enforce the configuration defined for this setting in the Windows Update Preferences policy to manage update downloads over that connection.
Troubleshooting
1. “Target Version” is set to 22H2, but the device remains on 21H1.
Probable Cause:
The version number entered in the Target Version field does not match Microsoft’s naming convention exactly.
Solution:
The admin should ensure that the value is exactly as listed by Microsoft (e.g., “22H2”).
2. The device performs an immediate, unscheduled reboot after the Windows Update Preferences policy is associated.
Probable Cause:
A modification was made to the Update Channel setting (e.g., moving from Semi-Annual to Windows Insider) within the Windows Update Preferences policy. Modifying the Update Channel triggers a reconfiguration of the underlying registry hives associated with the Windows Update service. To re-initialize the update agent under these new channel parameters, the operating system may force an immediate restart to apply the registry changes.
Solution:
Administrators should perform Update Channel migrations during scheduled maintenance windows to prevent unexpected downtime for active users.
Best Practices
- Maintenance Wake-Up: Enable Automatic wake up for maintenance for desktop fleets. This allows updates to install overnight, reducing the performance impact on employees during the day.
- Monitor “Feature Update Uninstall Period”: Set this to at least 10-15 days. This provides a sufficient safety net for users to report niche software bugs that might not have been caught during the pilot phase.