Category filter
How to deploy OEM configurations to Kyocera devices?
Most organizations employ OEMConfig as a business standard to enhance corporate compliance of the devices provisioned in the workspaces. OEMConfig is an administrative tool used to deploy OEM-specific settings to devices enrolled in the Android enterprise program. Device manufacturers that support OEMConfig develop their OEMConfig app to deploy managed configurations to their devices. Kyocera’s OEMConfig application – Device Config Plugin helps you configure advanced functionalities for Kyocera devices. It allows you to exert granular control over the hardware and software features of Kyocera devices. With the help of App Configurations, Hexnode facilitates you to create OEM-specific policies for such devices quickly.
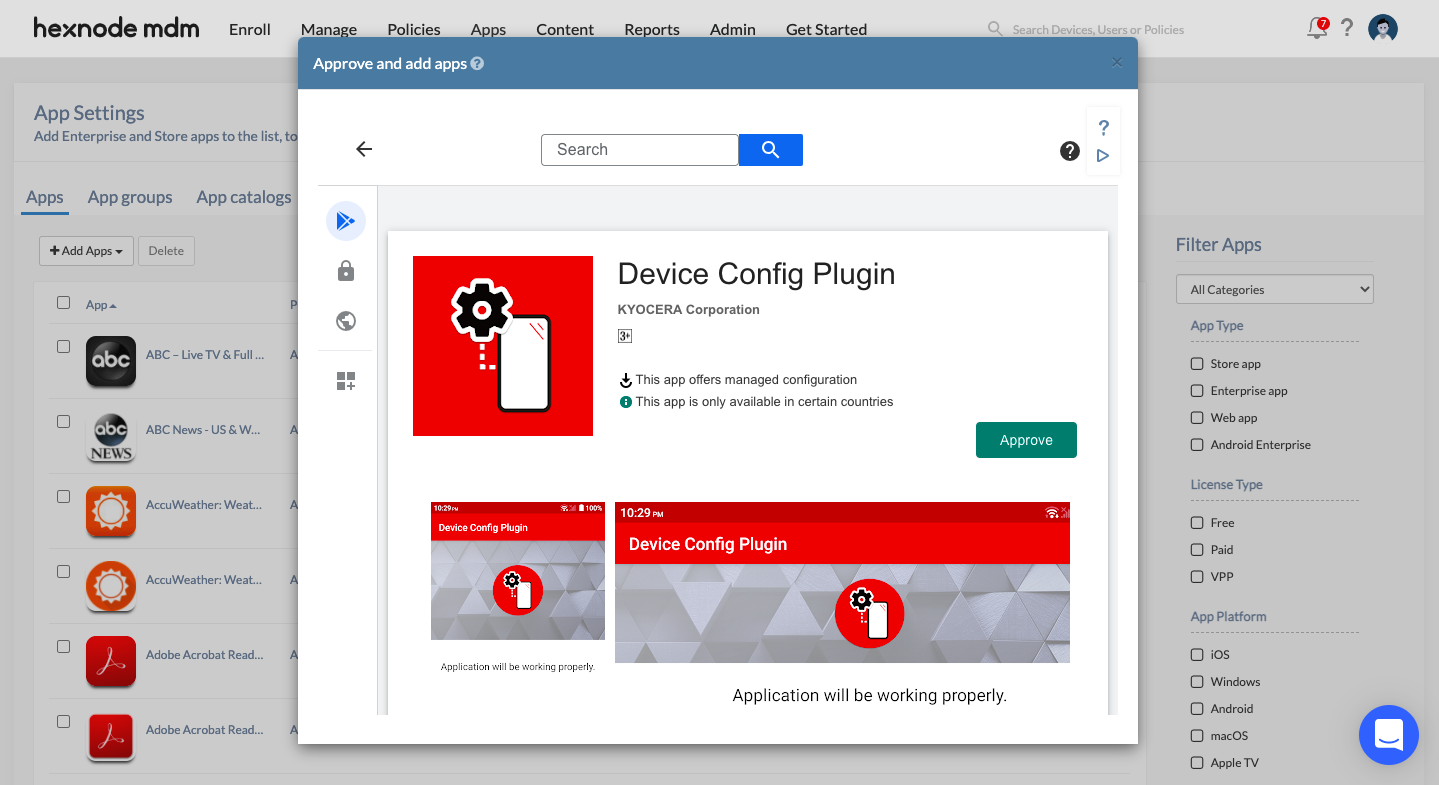
Approve and add Kyocera OEMConfig app to Hexnode inventory
Kyocera’s OEMConfig app – Device Config Plugin should be installed on the devices to configure settings for Kyocera devices. The app provides the interface for distributing the app configurations onto the device from the Hexnode console.
- Navigate to Apps.
- Go to +Add Apps > Managed Google Apps.
- Search for the Device Config Plugin app and click on Approve.
- A pop-up appears listing a set of permissions required for the app. Verify them and click Approve.
- Next, you will be asked to configure Approval Settings and Notifications when Kyocera’s Device Config Plugin app requests new app permissions. Make the necessary changes on how new app permissions are to be handled and click Done.
Set-up OEM configurations for Kyocera Business phones
- Go to Policies.
- You may choose the existing policy used to push OEMConfig app to devices or create a New Policy.
- Navigate to Android > App Management > App Configurations.
- Click Configure > Add new configuration.
- From the list of approved apps, select the Device Config Plugin app and click Add.
- Configure the required settings and click Done.
| Settings | Description |
|---|---|
| Applications Allowed to Manage Contacts | Specify the package name of the applications that will be allowed to manage contacts on the device. This option is enabled, if ‘Disable Manage Contacts’ is enabled. |
| Disable Power off by User | Enable this option to disallow device power-off. |
| Disable Mock Location | Specify whether to disable mock location option available on the device. |
| Disable App Shortcut on Lock Screen | Specify whether to disable app shortcuts on lock screen. This prevents app shortcuts from being placed on the device lock screen. |
| Disable USB Debug | Specify whether to disable USB debugging option on the device. |
| Disable USB Host | Toggle this option to disable USB host. It prevents device user from connecting any external USB devices. |
| Disable Default Launcher | Toggle this option to disable all the launcher applications that comes pre-installed on the device. This option can be enabled when other launcher applications is installed on the device. |
| Restrict Incoming Call | Set restrictions for incoming calls on the device. Available options are:
|
| Whitelist Phone Numbers for Incoming Call | Enter phone numbers to accept the incoming calls from. This is enabled when ‘Restrict Incoming Call’ is set to Without Whitelist or Without Contacts and Whitelist. This field takes the phone number specified in the country calling code format, excluding the prefix ‘+’ sign. |
| Restrict Outgoing Call | Configure restrictions for outgoing calls on the device. Available options are:
|
| Whitelist Phone Numbers for Outgoing Call | Enter phone numbers to allow outgoing calls. This is enabled when ‘Restrict Outgoing Call’ is set to Without Whitelist or Without Contacts and Whitelist. |
| Disable Clipboard | Toggle the option to disable clipboard. Disabling clipboard prevents cut, copy, paste functions on the device. |
| Settings | Description |
|---|---|
| Disable Voice Roaming | Toggle this option to disable voice roaming on the device. Allowing voice roaming may incur data charges. |
| Disable Mobile Data | Specify whether to disable mobile data. Disabling this option prevents the use of mobile data on the device. |
| Disable USB Tethering | Toggle this option to prevent users from sharing mobile data with other devices using USB. |
| Disable Bluetooth Tethering | Specify whether to disable Bluetooth Tethering. This disallows device user from sharing mobile data with other devices over Bluetooth. |
| Disable Wi-Fi | Wi-Fi option is disabled on the device, if this option is enabled. |
| Disable Open Network | Specify whether the access to non-secure Wi-Fi networks from the device is to be disabled. |
| Disable Wi-Fi Tethering | Toggle this option to prevent device user from tethering Wi-Fi. |
| Settings | Description |
|---|---|
| Disable NFC | Toggle this option to disable NFC on the device |
| Disable OTA update | Toggle this option to disable OTA update on the device. |
| Disable SIM card lock | Toggle this option to disable SIM card lock. |
| Disable Emergency alert | Specify whether to disable emergency alerts on the device. |
| Disable Vibrate | Toggling this option disables all forms of vibration on the device. |
| Disable Battery Shortcut | Specify whether to disable battery shortcuts on notification. |
| Disable Edit Quick settings | Specify whether to disable editing of Quick Settings on the device. |
| Disable Manage Contacts | Specify whether to prevent device user from managing contacts on the device. |
| Disable Recovery Mode | Enable this option to prevent device from booting to Recovery Mode. |
| Disable Doze Mode | Specify whether Doze Mode is to be disabled on the device. |
| Force SD card Encryption | Specify whether to force encryption on SD card. |
| Alert Notification Control – AMBER | You can choose to Enable or Disable AMBER alert notifications from appearing on the device. |
| Alert Notification Control – SEVERE | You can choose to Enable or Disable SEVERE alert notifications from appearing on the device. |
| Alert Notification Control – EXTREME | You can choose to Enable or Disable EXTREME alert notifications from appearing on the device. |
| Active Bluetooth Profile | Choose a Bluetooth profile to be active on the device. Available options are: HFP, Audio, and Data. If no item is selected, all profile is active. If HFP is selected, only HFP, HSP, MAP, and PBAP are allowed. If Audio is selected, only A2DP, AVRCP, HFP, and HSP are allowed. If Data is selected, only GATT, HID, MAP OPP PAN, and PBAP are allowed. |
| Bluetooth Class of Device | Enter the Bluetooth class of device. Based on the power and range capabilities, devices fall into one of the following bluetooth classes: class 1, class 2, or class 3. |
| Launcher Application | Enter the package name of the application which is to be set as the default launcher application. |
| Doze Mode Whitelist | Create a whitelist of applications that will bypass the Doze Mode settings configured on the device. Specify the package name of those applications to be whitelisted. |
| Data Saver Whitelist | Create a whitelist of applications that should bypass the Data Saver restrictions configured on the device. Specify the package name of those applications to whitelist them. |
| Restrict Carkit Power settings | Suppose the users employ hands-free carkit while driving. You can determine whether the device should be powered on/off automatically when the vehicle’s engine is turned on/off. The available options are:
|
| Settings | Description |
|---|---|
| Recent key | Enable this option to restrict recent key. |
| Power key | Enabling this option restricts power key. |
| Volume Up key | Select this option to restrict the usage of volume up key. |
| Volume Down key | Select this option to disable volume down key. |
| Long Home Press | Enable this option to restrict long home press action on the device. |
| Camera key | Camera key is restricted if this option is enabled. |
| Programmable key | Enable this option to restrict programmable key. |
| Speaker key | Speaker key will be restricted if this option is enabled. |
| SOS key | SOS key will be restricted when the option is enabled. |
| Exchange Key Event | Enabling the option sends specific broadcast intent when any of the restricted key event specified above occurs. |
| Settings | Description |
|---|---|
| Name | Specify the identifier name of the VPN. |
| Server address | Specify the domain name or IP address of the VPN server. |
| Username | Enter the username of the VPN server |
| Password | Enter the password to authenticate the username. |
| IPSec pre-shared Key | Enter the IPSec pre-shared key for your VPN gateway. |
| Type | Select the connection type for the VPN. Choose from the following options: PPTP, L2TP/IPSec PSK, L2TP/IPSec RSA, IPSec Xauth PSK, IPSec Xauth RSA, or IPSec Hybrid RSA. |
| DNS servers | Specify the internal DNS servers to be used for the VPN connection. |
| DNS search domains | Set the internal DNS search domains to be used for the VPN connection. |
| Forwarding Routes | Configure the forwarding routes to send the traffic to the destination through the VPN interface. |
| PPP Encryption (MMPE) | Toggle this option to enable Point-to-Point Protocol encryption. |
| L2TP Secret | Enter the L2TP secret or the pre-shared key used to establish a VPN connection. |
| IPSec identifier | Enter the IPSec identifier to authenticate the VPN connection. |
| IPSec user cert | Specify the IPSec User certificate. The certificate assures user identity for remote VPN access. |
| IPSec CA cert | Specify the IPSec CA certificate to authenticate the device for the VPN connection |
| IPSec server cert | Specify the IPSec server certificate. |
| Proxy hostname | Enter the hostname of the VPN proxy. |
| Proxy port | Enter the port number of the VPN proxy server. |
Associate Policies with Devices / Groups
If the policy has not yet been saved.
- Navigate to Policy Targets.
- Click on +Add Devices.
- Choose the devices and click OK.
- Click on Save to apply the policies to devices.
Apart from devices, you can also associate the policies with device groups, user and user groups from Policy Targets.
If the policy has been saved, you can associate it with another method.
- From Policies tab, check the policies to be associated.
- Click on Manage > Associate Targets and choose the device.
- Click on Associate to apply policy to the devices.