Category filter
How to bind macOS devices to Active Directory
To set AD as the identity provider, an IT administrator have to usually bind each Mac machine with the Active Directory manually. With Hexnode’s AD Asset Binding policy, administrators can remotely bind the macOS devices with the AD domain. This allows users to log in to their devices with their AD credentials.
With AD Asset Binding policy, you can bind AD, Apple Open Directory, and OpenLDAP with your Mac.
Configure Mac AD Asset Binding in Hexnode
To configure AD asset binding in macOS devices,
- On your Hexnode portal, go to Policies.
- Click on New Policy to create a new policy or select an existing policy. If you are creating a new policy, provide a suitable policy name and description.
- Go to macOS > Network > AD Asset Binding and click Configure.
You will have the following options to be configured.
| Basic Settings | Description |
|---|---|
| Active Directory Domain | Specify the IP address or the Fully Qualified Domain Name (FQDN) of the server. The Mac device will get bound to this domain. Hexnode supports the use of the wildcard %domain% to fetch the AD FQDN. |
| Username | Enter the username of the administrator account used to authenticate and bind the device to the AD domain. Hexnode supports the use of wildcards %username%, %email% and %name%. |
| Password | Enter the password of the AD administrator account. |
| Organizational Unit | Enter the distinguished name of the organizational unit to which the joining computer is to be added. Distinguished name will be in the format CN=CommonName, OU=OrganizationalUnit, DC=DomainComponent. For example: CN=User, OU=Sales, DC=acme, DC=corp |
| Advanced Settings | Description |
|---|---|
| Create mobile account at login | Check this option to enable users to login to their Mac device with their AD credentials even if they are not connected to the organization’s AD server. If checked, user’s data will be stored locally and will get automatically logged into the mobile account. |
| Require confirmation before creating a mobile account | Check this option to send a confirmation message to the end user on creating a mobile account, when a user logs in to the Mac machine using the AD user account or as a network user. |
| Force local home directory creation on the startup disk | If enabled, forces the local home directory to be created on the startup disk of the user. This helps users access the network user account remotely.
|
| Use UNC Path specified in the Active Directory to derive the network home location | Check this to use the AD standard attribute for the home directory location. If unchecked, uses the macOS attribute for the home folder location. |
| Use the Network Home Protocol | Choose either afp or smb protocol for accessing the home folder. This can only be configured if “Use UNC Path specified in the Active Directory to derive the network home location” is checked. By default, afp is selected. |
| Any domain in the forest can authenticate | If checked, macOS automatically searches all domains for user authentication. If you uncheck this option, only the domains to which the device is bound to will be allowed to authenticate. |
| Default user shell after device log in | Enter the default shell for the user after logging in to the Mac machine. By default, “/bin/bash” is used. |
| Map UID to attribute | To map an AD attribute to the unique user ID, check this option and enter the name of the AD attribute. |
| Map user GID to attribute | To map an AD attribute to the user group ID in user account, check this option and enter the name of the AD attribute. |
| Map group GID to attribute | To map an AD attribute to the GID in group account, check this option and enter the name of the AD attribute. |
| Prefer this Domain Server | Enable to specify the name of the preferred domain server for authentication.
By default, Mac identifies the authentication domain server based on site information and domain controller responsiveness. If a domain controller specified here is unavailable, Mac returns to its default behaviour. |
| Allow administration by | Check this option and add groups to the list. All members of the specified group will have administrative privileges on their Mac. You should specify the display name of the required security groups.
If Allow Administration by is enabled, all the domain and enterprise admins are granted administrative privileges by default. |
| Namespace | Enable to set the primary account naming convention as either Domain or Forest.
By setting namespace as Forest, if multiple domains in the same forest contains several users with the same user name, then those users can login with the name of the domain followed by the login name (domain\login name). In a normal case, user can login using username\password. If Domain is selected users have to enter their domain name to login. |
| Packet Signing | Checking this option allows to choose how to ensure data security. The available drop-down values are Allow, Require and Disable. If Require is selected the LDAP connection required to communicate with the AD must be signed by the Open Directory client. |
| Packet Encryption | Enable to choose how to encrypt the data. The available drop-down values are Allow, Require, Disable and SSL. If Require is selected the LDAP connection must be encrypted by the Open Directory client. |
| Restrict DDNS | Enable to specify which interface to use when updating the Dynamic Domain Name System. Specify the BSD name of the interface.
Run the command “networksetup -listallhardwareports” in the terminal, BSD name is same as the returned Device field value. For example: en0, en1, etc. |
| Password trust interval | Enable to specify how often the computer trust password is to be changed.
|
Associate Policies with macOS devices
If the policy has not been saved,
- Navigate to Policy Targets.
- Click on Devices/ Device Groups/ Users/ User Groups/ Domains.
- Choose the targets and click OK and then Save.
If you have the policy saved already,
- Go to Policies tab and choose the desired policy.
- Click on the Manage drop-down and select Associate Targets.
- Choose the target entities and click Associate.
You can choose devices, users, groups, and domains as the policy targets.
What happens at the device end?
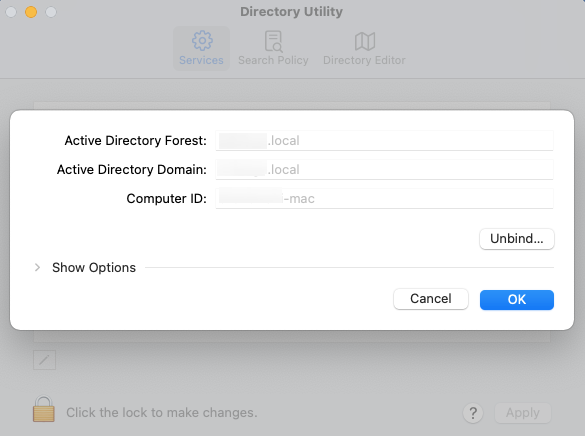
Once the policy is associated with the device, the Disk Utility app establishes trusted binding between the macOS device and the organization’s Active Directory server.