Endpoint Patch Management: Reducing Security Risk Across Devices
Learn how endpoint patch management reduces vulnerabilities, speeds CVE response, and secures your devices.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.
The cybersecurity landscape has been shaken by a critical discovery: CVE-2026-21643, a high-severity SQL injection vulnerability in Fortinet’s FortiClient Endpoint Management Server (EMS).
With a CVSS score of 9.1, this is not just another vulnerability. It provides a direct path for unauthenticated attackers to achieve Remote Code Execution (RCE)—on systems designed to secure your enterprise.
The situation is even more serious now that this flaw has been added to the CISA Known Exploited Vulnerabilities (KEV) catalog. This confirms that the threat is active, weaponized, and already being exploited.
CVE-2026-21643 is caused by improper sanitization of user input in SQL queries within FortiClient EMS.
In simple terms, an attacker can send a specially crafted HTTP request to the EMS management interface. Because the input is not properly validated, the system executes malicious SQL commands.
This can lead to:
The risk is amplified by the role of EMS. It acts as the central control system for thousands of endpoints.
If the server is compromised, attackers can:
In effect, the system meant to protect your endpoints becomes the attacker’s most powerful tool.
Fortinet has released patches for affected versions (7.0, 7.2, and 7.4), and applying them should be your top priority.
However, patching alone is not enough.
Security teams should also:
Just as important—never expose the EMS management interface to the public internet.
Strengthen your defenses by:
In situations like this, visibility and control are everything.
Hexnode UEM enables IT teams to respond quickly and at scale.
With Hexnode, you can:
By enforcing Compliance Rules, Hexnode can automatically quarantine any device that fails to update within a 24-hour window, effectively sealing off the network from potential lateral movement originating from an unpatched endpoint.
Discover how Hexnode simplifies patch management with automation, real-time compliance, and full device visibility.
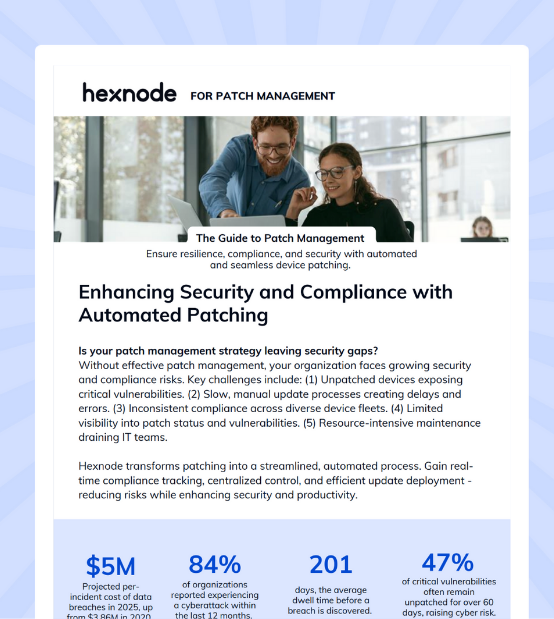
Featured Resource
Hexnode UEM for Patch Management
Get actionable security insights, patch strategies, and threat alerts to keep your endpoints protected.
Start your 14-day free trial today!