How Companies Boost Productivity with IT Automation Using Hexnode
Learn how Hexnode’s IT automation capabilities streamline endpoint tasks and management workflows.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

Endpoint workflow orchestration can become fragile when tools require administrators to build long sequences of conditions and scripts. When the fleets grow and environments change, those sequences break, and the automation layer becomes yet another system that needs maintenance.
This problem matters because managing endpoints already takes up a large portion of IT teams’ time. A 2024 Forrester Consulting study commissioned by Google reported that respondents spent, on average, 19% of their time on endpoint security, 15% on endpoint management, and 14% on endpoint deployment. That is real operational load, and orchestration should reduce it, not increase it.
In this article, we examine why endpoint orchestration fails in real-world environments and how a state-driven, logic-based model can deliver reliable, scalable automation without adding operational overhead.
Endpoint orchestration fails in predictable ways, regardless of platform.
The strongest model for workflow orchestration in endpoint management is not a step-by-step flow. It is state-based automation, where you define the desired state and let the system continuously converge devices toward it.
Instead of issuing a long sequence of imperative commands, you define what should be true. The platform enforces that truth based on context such as OS, role, ownership, compliance posture, and location.
Endpoints benefit from this philosophy. Rather than encoding “how to get there” in fragile workflow chains, you define the intended state and let logic-based UEM automation maintain it consistently.
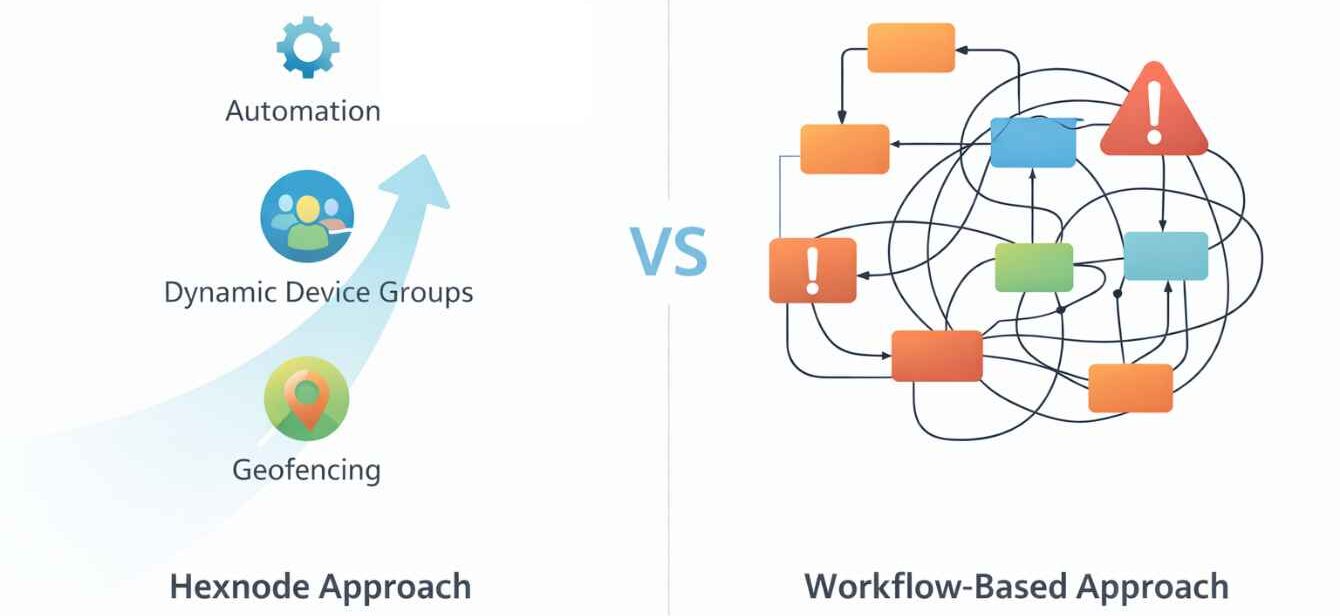
Hexnode Automation let you automate device management tasks with clear triggers and scope, including real-time event-based execution. You can use automation to apply configurations, deploy apps, and standardize repetitive work without rebuilding long multi-step workflows every time requirements change.
Dynamic groups automatically add and remove devices based on defined conditions, which reduces manual group maintenance and keeps targeting aligned. Instead of building orchestration as a long chain of conditional branches, you express logic once as group criteria and attach the relevant policies, apps, and actions.
Geofencing in Hexnode lets you create virtual boundaries around locations and apply restrictions or actions when devices enter or exit those boundaries. This capability is particularly useful for kiosks, warehouse tablets, retail devices, and field fleets where “where the device is” should influence what it can do.
Consider a common enterprise setup where a new Windows laptop is enrolled for a Sales employee. The device must remain compliant with endpoint protection, and if it leaves a designated warehouse or office location, restrictions must apply automatically.
Many teams attempt to model this as multiple branching workflows. One flow handles onboarding, another monitors security posture, and a third reacts to location changes. Over time, workflow orchestration grows complex, interdependent, and difficult to maintain.
With Hexnode, you implement this as a unified, state-driven process by separating execution, targeting, and context.
Step 1: Configure baseline policies and required configurations
Administrators first define the policies, applications, and restrictions required for devices. These can include security policies, required applications, configuration profiles, and compliance settings that establish the device’s baseline state.
Step 2: Apply policies dynamically using device groups
Dynamic Device Groups automatically organize devices based on attributes such as operating system, compliance status, user role, or department. Devices that match the defined criteria are automatically added to the group, and the associated policies are applied without manual intervention.
Step 3: Adjust policies based on location and context
For mobile roles like Sales, devices frequently move between locations. Geofencing allows administrators to define virtual boundaries and automatically apply or remove policies when devices enter or leave specific areas. This ensures location-based safeguards without creating additional workflow logic.
Instead of maintaining three separate workflows, you define three states:
Policies attach to state, not to a brittle sequence of steps. When business requirements change, you update criteria or assignments. You do not rebuild orchestration logic.
This is the advantage of logic-based UEM automation. Complexity does not increase security or scalability. Clear state definitions and automatic policy association create an orchestration model that remains predictable, auditable, and easy to evolve.
The best orchestration model supports the full device lifecycle, not just isolated tasks. Automating device lifecycle means treating devices as continuously managed assets from provisioning through repurposing or retirement.
Effective workflow orchestration must support the entire device lifecycle:
By combining automation, policy-based targeting, compliance engines, reporting, remote actions, app management, and integration capabilities, Hexnode delivers workflow orchestration across the entire device lifecycle. You define the desired state of the device across its lifespan, and the platform continuously enforces, monitors, and adapts without forcing you to rebuild workflows every time requirements evolve.
Platform transitions, pricing shifts, and changes in support models often force IT teams to evaluate operational risk. When workflow orchestration becomes tightly coupled to complex workflow design, even minor changes can disrupt operations. Teams increasingly prefer models that reduce dependency on specialist knowledge and brittle sequencing.
The practical takeaway is simple: orchestration should be portable, understandable, and easy to operate. If your automation framework requires deep expertise to modify safely, it becomes a bottleneck during periods of change instead of a driver of agility.
With Hexnode, workflow orchestration becomes predictable, auditable, and easy to evolve. Instead of maintaining workflows, you define outcomes. The platform handles enforcement, remediation, and adaptation across the entire device lifecycle.
Download the White paper to enhance your organization's access management methods and ensure device and data security.
Get the white paper1) What is the difference between workflow automation and a workflow orchestrator?
Workflow automation executes a single task automatically, such as deploying an app or applying a restriction. A workflow orchestrator coordinates multiple tasks into a controlled process, handling conditions, targeting, and sequencing across systems.
2) How do Hexnode Dynamic Groups support logic-based UEM automation?
Hexnode Dynamic Groups automatically adjust membership based on specified conditions. When a device matches the criteria, it enters the group and receives assigned policies and apps. When it no longer matches, it exits and the targeting changes accordingly. This enables state-based orchestration without manual group upkeep.
3) Can Hexnode enforce different policies when a device leaves a site?
Yes. Hexnode geofencing lets you create a virtual boundary around a location and apply restrictions or actions when devices enter or exit that boundary. This is useful for warehouse, retail, kiosk, and field deployments.
Replace fragile workflow chains with state-based automation. Manage dynamic device groups, automate device lifecycle, and enforce policies with clarity and control.
SIGNUP NOW