What is Enterprise Mobility Management (EMM)?
Learn how EMM secures, configures, and manages all mobile devices (BYOD & corporate) using MDM, MAM and MCM tools.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

The question that both the developers and IT admins face, is clear – How can a device be uniquely recognised without invading privacy controls or losing consistency across workflows?
Android’s growing privacy framework when combined with the changing identifier policies, has made it increasingly challenging to balance user identity with the need for reliable device recognition. Whether it’s for app analytics, licensing, or enterprise device management, finding that balance between unique identification and data protection has become central to modern Android development and administration.
This blog discusses the concept of the Android ID, exploring its role, generation logic, and practical implications in modern Android management. It also highlights how UEM platforms like Hexnode leverage such identifiers responsibly, ensuring accurate device tracking, compliance enforcement, and secure lifecycle management across enterprise fleets.
Android ID in definition is a unique 64-bit hexadecimal string that Android generates to identify a device. In other terms, it acts as the Android device ID, allowing a way for apps and services to tell one device apart from another. Hardware identifiers such as IMEI are different from the Android device ID because this is tied to the software ecosystem and created during the device’s first boot.
At the OS level, the Android ID is managed within the system framework and exposed through APIs. This makes it a core element of how Android handles device-level identification across apps, services, and management platforms.
Across development and enterprise, Android ID offers a privacy-conscious, accessible, and relatively stable method of device recognition.
In UEM solutions like Hexnode, the Android ID helps IT teams individually identify and manage enrolled devices. Android ID is a reliable anchor point for device inventory, lifecycle management, and secure access control.
Discover how Android Enterprise makes Android devices secure and productive for work. Learn about its origins, mandatory components, and business value.

Featured resource
Everything you need to know about Android Enterprise program
The Android ID string: It is a 64-bit hexadecimal value assigned by the OS during the device’s initial setup. This is represented as a hex string and is always consistent for the lifecycle of the device, unless specific conditions reset it.
Internally, the system stores the value in the constant Settings.Secure.ANDROID_ID, allowing it to be available through Android’s secure settings to apps and management. For a developer, this makes the Android ID a convenient way to differentiate devices without relying on hardware-based identifiers like IMEI.
The generation of Android device ID is created using random elements. On the first boot, Android creates the ID using a pseudo-random algorithm. The value is then bound to the device’s OS installation.
This behavior is much needed for developers and IT teams to understand, especially when evaluating Android ID for tracking purposes.
The Android ID is stored within the device’s secure settings database and can be retrieved using the Settings.Secure API. Developers usually access this identifier to get Android ID programmatically, and to make sure that the process is both standard and secure.
Here’s a common example:
Java
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
import android.content.Context; import android.provider.Settings; import androidx.annotation.NonNull; import androidx.annotation.Nullable; import java.util.UUID; // Added for generating fallback UUID public class DeviceUtils { /** * Returns the app-scoped Android ID for this device. * * Note: ANDROID_ID is unique per app-signing key and user profile. * It may change after a factory reset or app reinstallation, and is NOT suitable * for tracking users across different apps (use Instance IDs or custom UUIDs if needed). * * @param context The application or activity context. * @return The Android ID, or a newly generated UUID if ANDROID_ID is null (which is rare on real devices). */ @NonNull // Changed to NonNull because it will always return a string now public static String getAndroidId(@NonNull Context context) { String androidId = Settings.Secure.getString( context.getContentResolver(), Settings.Secure.ANDROID_ID ); // Fallback to a generated UUID if Android ID is null (e.g., in some emulators or edge cases). // Returning a UUID makes the fallback useful as a unique identifier for that specific app instance. return androidId != null && !androidId.isEmpty() ? androidId : UUID.randomUUID().toString(); } } |
Kotlin
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
import android.annotation.SuppressLint import android.content.Context import android.provider.Settings import java.util.UUID // Added for generating fallback UUID /** * Returns the app-scoped Android ID for this device. * * Note: ANDROID_ID is unique per app-signing key and user profile. * It may change after a factory reset or app reinstallation, and is NOT suitable * for tracking users across different apps (use Instance IDs or custom UUIDs if needed). * * @param context The application or activity context. * @return The Android ID, or a newly generated UUID if ANDROID_ID is null or empty. */ @SuppressLint("HardwareIds") // Suppress lint warning for using hardware identifiers fun getAndroidId(context: Context): String { // Return type changed to non-nullable String val androidId = Settings.Secure.getString( context.contentResolver, Settings.Secure.ANDROID_ID ) // Fallback to a generated UUID if Android ID is null or empty. // Returning a UUID makes the fallback useful as a unique identifier for that specific app instance. return if (androidId.isNullOrEmpty()) { UUID.randomUUID().toString() } else { androidId } } |
These APIs make retrieving the Android device ID straightforward for both app developers and enterprise mobility tools.
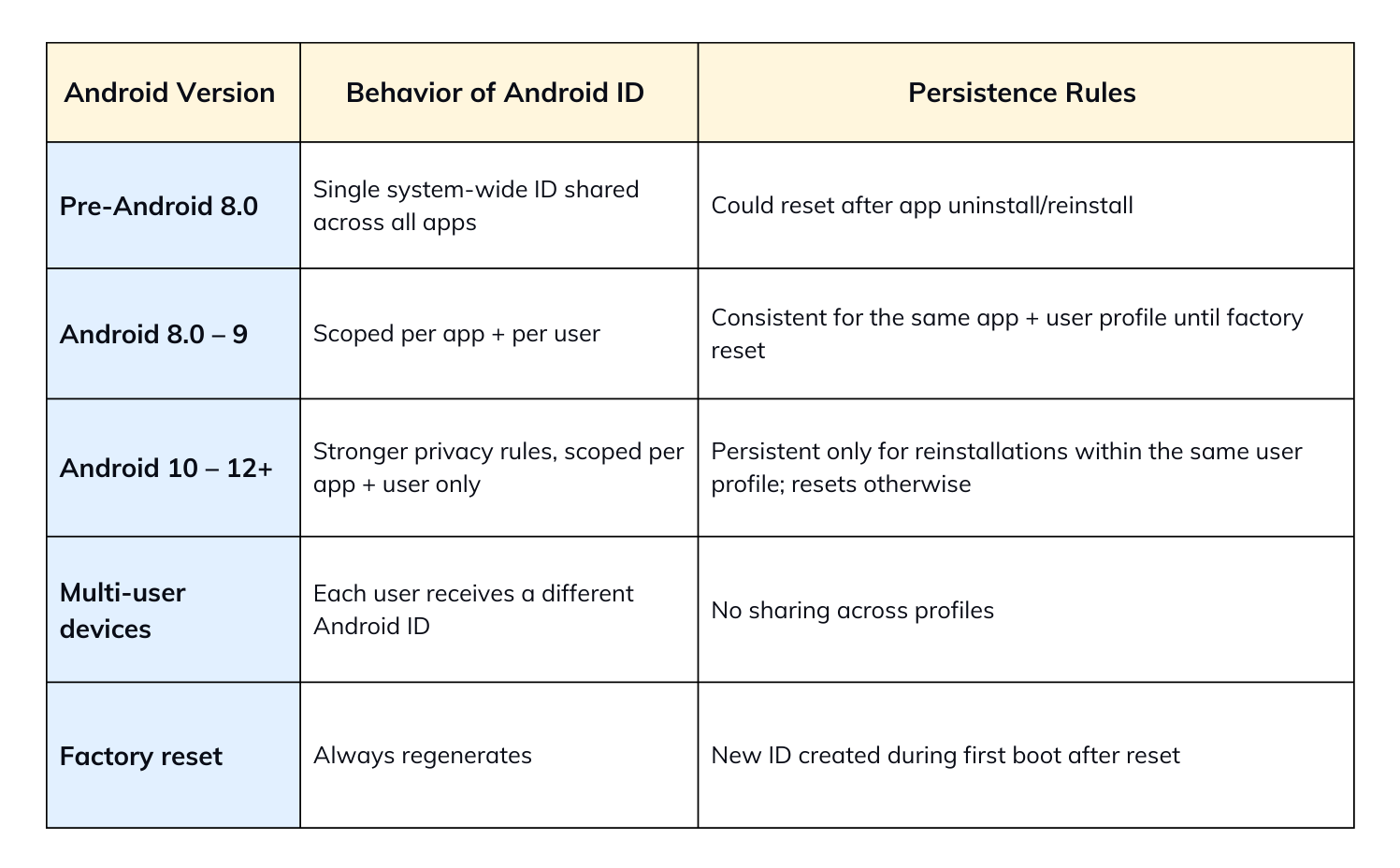
The way Android ID behaves has substantially grown across Android versions, majorly due to Google’s focus on user privacy and data security. Understanding the differences is critical for developers and IT teams who manage enterprise devices through MDM/UEM platforms.
Starting with Android 8.0 (Oreo), the Android device ID was reinvented to level up security and reduce the risk of device fingerprinting.
From Android 10 forth, privacy controls became even more strict:
In Android 11+, Google doubled down on this model by enforcing restrictions that ensured the Android ID could not be used as a stable hardware-equivalent identifier, especially in multi-user or enterprise contexts.
While the Android ID is designed to be persistent under normal conditions, several scenarios force regeneration:
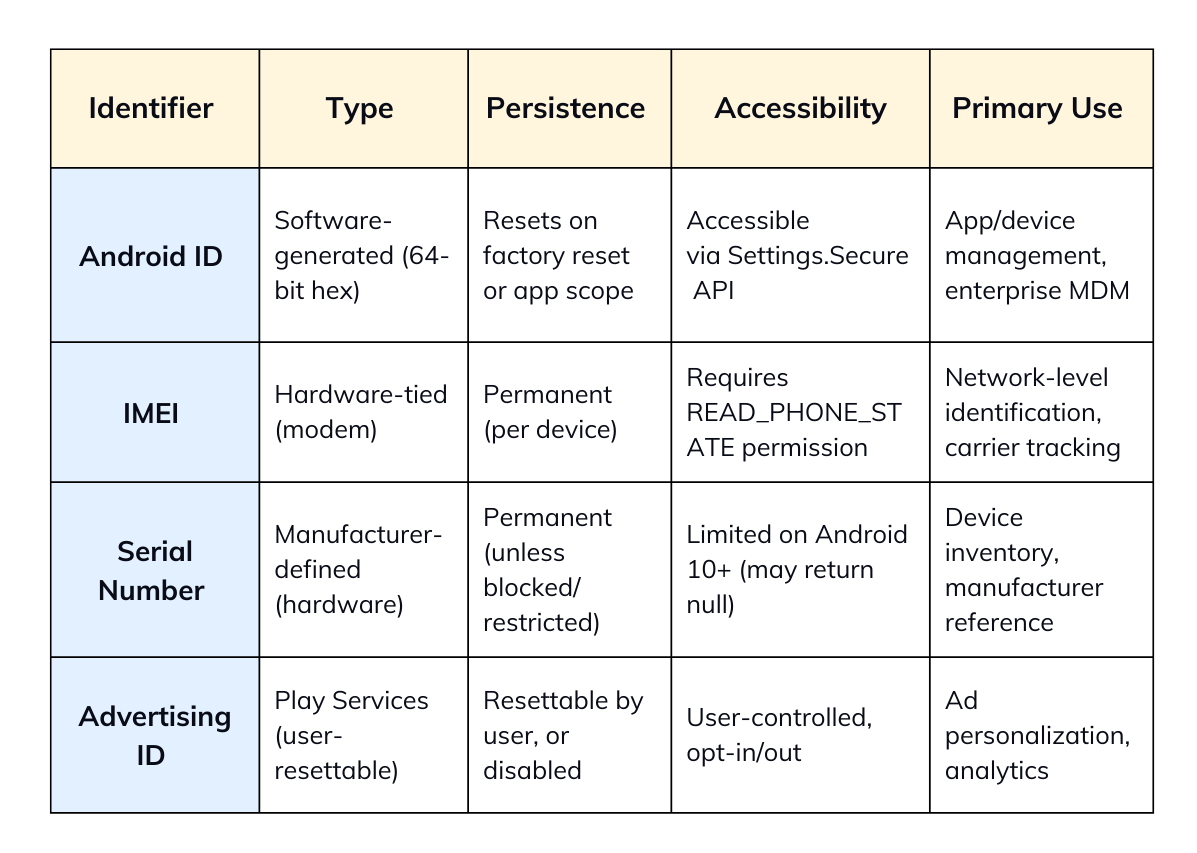
It’s important to know the difference between the Android ID from other device identifiers such as IMEI, Serial Number, and Advertising ID. Each of these has a different purpose, carries different privacy implications, and comes with its own set of access restrictions.
The IMEI (International Mobile Equipment Identity), a hardware-tied identifier embedded at the modem level of mobile devices identifies a physical device across networks uniquely. To access IMEI, The READ_PHONE_STATE permission is required, making it stricter user consent and privacy regulations.
On the contrary, the Android ID is a software-generated during the device’s first boot and scoped by app and user in modern Android versions. It can be accessed programmatically through Settings.Secure.ANDROID_ID without telephony privileges. This makes it more accessible in environments where IMEI collection is not possible.
The Serial Number is a manufacturer-defined, hardware-level identifier typically etched into the device. It was trusted for device-level identification, but with Android releases of today, access to the serial number is increasingly restricted.
On Android 10+, direct access to the serial number is limited to system apps and privileged device management solutions.
The Android device ID, however, is consistently accessible across the application layer, making it a safer and more predictable choice for developers and enterprise MDM platforms.
The Advertising ID (Ad ID) is a Google Play Services-based identifier designed specifically for advertising and analytics. It is user-resettable from device settings and can also be disabled completely by the user. Its primary use is ad personalization and tracking across apps.
The Android ID is non-resettable and is made for system-level and app-level use. It provides a more stable and persistent identifier, which is particularly important in enterprise and MDM contexts.
The Android ID serves as a versatile identifier from app-level personalization to large-scale enterprise mobility management. Its persistence (with limitations) and accessibility make it a practical choice for developers and IT admins who need to identify devices in a controlled manner.
Developers often bridge settings, preferences, or cached data to a specific Android ID, ensuring that the user experience remains consistent across sessions.
For example, a media app can use the Android device ID to associate playback preferences or app themes with the device, making the app remember user configurations without requiring a login.
In analytics, Android ID can be used as an anonymous device identifier for tracking telemetry. Since it is scoped per app, analytics platforms can use it to measure device-level metrics like engagement statistics, or feature adoption without linking to personally identifiable information.
Apps that enforce subscription-based access or media playback restrictions can bind licenses to the persistent Android ID of a device.
Android ID in enterprise environments is used for MDM or UEM platforms and plays a central role in large-scale deployments:
Android ID is widely used for app development and device management, but it comes with important warnings for uniqueness, persistence, and privacy.
The Android ID is not guaranteed to be unique across all contexts worldwide.
Google designed the modern Android device ID model to reinforce user privacy with:
This change aligns with Android’s broader privacy philosophy, balancing the need for identifiers with the user’s right to data protection.
One advantage of getting Android ID programmatically is that it does not require a dangerous runtime permission. The newer Android versions (Android 10+), Google classifies Android device ID as a sensitive identifier:
For organizations deploying hundreds of Android endpoints, this identifier offers a practical alternative to hardware-bound identifiers such as IMEI or Serial Number, which may not always be available or reliable.
Most UEM solutions leverage the Android device ID for:
This ensures that IT teams always have a consistent anchor for device management activities.
Key benefits of the persistent Android ID include:
Hexnode UEM directly uses Android ID to optimize device management and monitoring, making it highly effective for both GMS-enabled and non-GMS devices.
By using Android device ID as its base, Hexnode ensures that the IT teams can maintain consistency, security, and control, regardless of the device type, OS, or GMS availability.
1. Is Android ID unique to each device?
Yes, but its only unique with scope. It’s unique per app and per user profile on a device are not globally unique across all apps.
2. Can Android ID be changed?
It changes if the device is factory reset, if a new user profile is created, or if an app is uninstalled and reinstalled.
3. How to retrieve Android ID in code?
To retrieve the Android ID in code (java):
|
1 |
String androidId = Settings.Secure.getString(context.getContentResolver(), Settings.Secure.ANDROID_ID); |
4. Is Android ID same as device ID?
No. Android ID is software-generated, while “device ID” often refers to hardware identifiers like IMEI or Serial.
5. Is it safe to use Android ID in production apps?
Yes, but only for app-scoped identification. For sensitive tracking, Google recommends alternatives like Firebase Installation IDs.
6. Can Hexnode use Android ID for management?
Yes. Hexnode maps Android ID to devices for enrollment, policy assignment, and kiosk mode management.
7. Can Hexnode identify devices without an IMEI?
Yes. Hexnode can use Android ID to uniquely manage non-telephony devices, custom ROMs, and rugged endpoints.
Learn what Android ID is and why this unique identifier is crucial. Start your free 14-day Hexnode trial now!
Signup now!Android ID
A 64-bit hexadecimal string generated by the Android operating system during the first boot. Scoped per app and user in modern Android versions, it serves as a software-based identifier for device recognition, app personalization, and enterprise device management.
IMEI (International Mobile Equipment Identity)
A hardware-bound identifier embedded at the modem level of mobile devices. It uniquely identifies physical devices across cellular networks and requires the READ_PHONE_STATE permission for access.
GSF ID (Google Services Framework ID)
An identifier generated by Google Play Services and linked to a Google account on the device. Primarily used by Google to manage app installations, updates, and sync across services. Not accessible on non-GMS or AOSP devices.
SSAID (Settings.Secure.ANDROID_ID)
The internal reference constant in the Android framework used to fetch the Android ID. Developers retrieve it through Settings.Secure.getString() for application-level use.
Ad ID (Advertising ID)
A user-resettable identifier managed by Google Play Services. Designed specifically for advertising and analytics, it can be reset or disabled by the user and is not intended for system-level or enterprise use.
AOSP (Android Open Source Project)
The open-source base of the Android operating system. Devices running AOSP without Google Mobile Services (GMS) rely on Android ID as an alternative to Google-dependent identifiers like GSF ID.
Persistent Identifier
This is an identifier that remains stable across reboots and app sessions. Android ID is persistent within an app/user scope but resets when factory reset.
Kiosk Mode
A mode where a device is locked down to a single app or limited functionality, often used in retail, education, or enterprise. Managed through UEM solutions, often identified using Android ID.
Custom ROM
A modified version of the Android OS, often based on AOSP. On such devices, identifiers like GSF ID may not exist, making Android ID more critical.
Telephony Privileges
Permissions required to access hardware-tied identifiers like IMEI. Android ID does not need telephony privileges, making it more accessible in non-telephony devices.
Scoped Identifier
An identifier whose validity is restricted to a specific context (e.g., app + user). Starting from Android 8.0, the Android ID became scoped per app per user.