BYOD and GDPR: The art of crafting GDPR-compliant BYOD policies
Craft GDPR-compliant BYOD policies while securing enterprise data effectively

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

Enterprises increasingly rely on mobile devices to enable productivity, remote work, and seamless collaboration. However, this shift introduces a fundamental challenge: how can organizations balance employee flexibility with complicated security? BYOD (Bring Your Own Device) empowers users but expands the attack surface, while corporate-owned devices offer tighter control but reduce flexibility. This tension forces IT teams to rethink device management strategies. To address this, organizations need a unified approach that enforces security without compromising user experience, and this is where Hexnode plays a critical role.
Enterprises typically adopt one of three device ownership models based on operational and security requirements. Bring Your Own Device (BYOD) allows employees to use personal devices for work, giving users autonomy over hardware and usage. Corporate-owned devices are fully provisioned and controlled by the organization, ensuring standardized configurations. Corporate owned personally enabled (COPE) sits between these models, allowing limited personal use on company-owned devices under defined policies.
Each model represents a different balance between flexibility and control. BYOD prioritizes user convenience but introduces variability, while corporate-owned devices emphasize consistency and enforceability. COPE attempts to combine both by enabling flexibility within a controlled framework. Choosing the right model requires a clear understanding of how each impacts security, compliance, and operational efficiency.
BYOD remains a popular choice because it aligns with modern workforce expectations and reduces organizational overhead. However, its advantages come with security trade-offs that enterprises must actively manage.
The benefits of bring your own device include improved employee satisfaction and productivity, as users prefer working on familiar devices. Organizations reduce capital expenditure by eliminating the need to purchase hardware for every employee. BYOD also accelerates onboarding and supports remote work by allowing immediate access to corporate systems. These advantages make it highly attractive for distributed and agile teams.
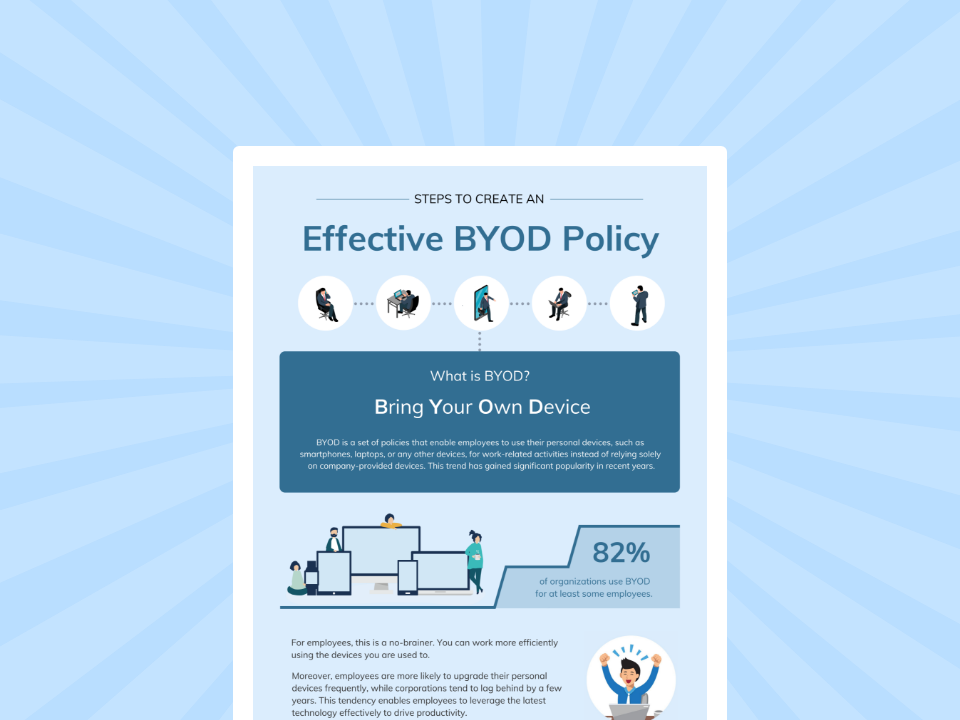
Learn how to create and implement a BYOD policy that best suits your organization.
Download the Infographic| Category | Pros of BYOD | Cons of BYOD |
| Flexibility | Employees can use familiar devices, improving productivity and user satisfaction | Blurs boundaries between personal and corporate usage, increasing risk exposure |
| Cost Efficiency | Reduces hardware procurement and maintenance costs for organizations | Hidden costs in securing, monitoring, and managing diverse devices |
| Security | Can be secured with proper management tools and policies | Data leakage risks due to personal apps and uncontrolled data sharing |
| Visibility | Minimal intrusion into personal usage improves employee trust | Limited visibility creates blind spots in monitoring and threat detection |
| Application Usage | Users can customize apps to suit their workflow | Installation of unverified apps increases vulnerability to malware |
| Network Access | Enables work from anywhere, supporting remote productivity | Use of unsecured networks increases risk of interception and attacks |
| IT Management | Reduces burden of device provisioning | Difficult to enforce policies without impacting user privacy |
BYOD environments expand the attack surface because organizations do not fully control endpoint configurations. Corporate data coexists with personal data, making separation and protection more complex. Devices may lack updates or proper encryption, increasing vulnerability. Without structured controls, enforcing compliance and monitoring threats becomes inconsistent. These risks make BYOD management heavily dependent on advanced endpoint management solutions.
Corporate-owned devices provide organizations with full ownership and control over endpoints, enabling consistent policy enforcement and improved security outcomes.
Organizations can standardize configurations, enforce updates, and maintain full visibility across all devices. IT teams can deploy applications, restrict usage, and monitor activity without limitations. This consistency reduces operational complexity and improves overall security posture. Corporate-owned models also simplify onboarding and lifecycle management.
Full control allows organizations to enforce encryption, restrict app installations, and implement strong authentication measures. IT teams can respond immediately to incidents using remote lock, wipe, and reconfiguration capabilities. This significantly reduces risks related to data leakage and unauthorized access. Compliance requirements are also easier to meet due to centralized control and auditing.
Corporate-owned devices require higher upfront investment and ongoing maintenance. Employees may experience reduced flexibility, which can impact satisfaction and productivity. Managing large device fleets still requires scalable infrastructure and automation. Without proper tools, operational overhead can increase despite the control advantages.
Each model introduces distinct BYOD vs corporate-owned devices security challenges, but these can be addressed effectively with the right strategies and tools.
In BYOD environments, corporate data resides on personal devices where organizations have limited control over how that data is accessed, stored, or shared. Employees may unintentionally transfer sensitive information through personal email, third-party apps, or unsecured cloud services. The lack of clear boundaries between personal and corporate data increases the risk of accidental exposure. Additionally, organizations cannot fully prevent users from backing up corporate data to personal storage systems. This creates significant challenges in maintaining data integrity and confidentiality across endpoints.
BYOD introduces inherent limitations in monitoring because organizations must respect user privacy on personal devices. IT teams cannot fully track user activity, installed applications, or network behavior without risking privacy violations. This results in blind spots that make it difficult to detect anomalies, unauthorized access, or potential threats in real time. Without complete visibility, incident response becomes slower and less effective. Over time, these gaps can lead to undetected vulnerabilities within the enterprise environment.
A BYOD environment consists of a wide range of devices with different operating systems, versions, and security configurations. Some devices may lack the latest patches, while others may not meet minimum security requirements. This inconsistency makes it difficult to enforce uniform policies across all endpoints. As a result, even a single vulnerable device can become an entry point for attackers. Maintaining a consistent security baseline across such a fragmented environment becomes a persistent challenge for IT teams.
Employees using personal devices often install a variety of applications, many of which may not be verified or secure. These applications can introduce malware or create backdoors into corporate systems. Additionally, users frequently connect to public or unsecured Wi-Fi networks, increasing the risk of interception and man-in-the-middle attacks. Since organizations do not control these behaviors, enforcing safe usage practices becomes difficult. This significantly increases the overall attack surface.
Regulatory frameworks such as GDPR, HIPAA, and others require strict control over how data is stored, accessed, and transmitted. BYOD complicates compliance because organizations cannot fully enforce these controls on personal devices. Data may be stored in unauthorized locations or accessed outside approved environments. Auditing and reporting have also become more complex due to limited visibility. Failure to meet compliance requirements can result in legal penalties and reputational damage.
Personal devices are more likely to be lost or stolen because they are used across both personal and professional contexts. If such a device contains corporate data without adequate protection, it can lead to unauthorized access. Weak authentication mechanisms or lack of encryption further amplify this risk. In many cases, delayed response to such incidents increases the potential impact. This makes device-level security a critical concern in BYOD environments.
BYOD creates a fundamental conflict between enterprise security requirements and employee privacy expectations. Organizations need to monitor and control devices to protect data, but excessive oversight can lead to resistance from employees. This tension limits the extent to which security measures can be enforced. As a result, IT teams often have to compromise between visibility and user trust. Striking the right balance remains one of the most complex challenges in BYOD implementation.
| Aspect | BYOD | Corporate-Owned Devices |
| Control | Limited | Full control |
| Security Enforcement | Complex | Strong and consistent |
| Cost | Lower upfront | Higher investment |
| User Experience | High flexibility | Moderate flexibility |
| Compliance | Difficult | Easier |
To address these challenges, organizations must adopt a structured and technology-driven approach that ensures consistent security across all device types.
Containerization creates a secure, isolated workspace on the device where corporate apps and data reside, completely segregated from personal content. DLP policies can be enforced within this container to restrict actions such as copy-paste, screen capture, file sharing, and data transfer to unauthorized applications or cloud services. Administrators can also control data flow between managed and unmanaged apps using techniques like app wrapping and secure gateways.
Policy standardization involves defining and enforcing baseline security configurations across all enrolled devices. This includes mandatory encryption, minimum OS version requirements, patch management, password complexity rules, and biometric authentication. Automated compliance engines continuously evaluate device posture against these policies and trigger remediation actions such as restricting access and notifying users of non-compliant devices. This approach ensures consistent security posture across a fragmented device ecosystem.
Application management includes whitelisting approved apps, blacklisting risky applications, and controlling app permissions to prevent unauthorized data access. Managed app configurations can enforce secure data handling within enterprise applications. On the network side, organizations can mandate the use of secure VPN tunnels, enforce Wi-Fi policies, and block access from unsecured or unknown networks. Techniques such as per-app VPN and secure web gateways further enhance protection by isolating corporate traffic from general internet usage.
Continuous compliance monitoring ensures that devices adhere to regulatory and organizational standards at all times. UEM systems generate detailed audit logs capturing device activity, policy enforcement actions, and access events. These logs support reporting requirements for frameworks such as GDPR, HIPAA, and ISO standards. Automated reporting and alerting mechanisms help organizations quickly identify violations, conduct forensic analysis, and demonstrate compliance during audits.
Remote management enables IT teams to respond instantly to security incidents involving lost, stolen, or compromised devices. Capabilities include remote lock, full or selective wipe (corporate data only), device tracking, and remote troubleshooting. These actions can be triggered manually or automatically based on predefined conditions such as non-compliance or suspicious activity. This minimizes the risk window and ensures rapid containment of potential threats.
Role-based access control (RBAC) restricts administrative privileges based on user roles, ensuring that only authorized personnel can access specific device data or management functions. This minimizes unnecessary exposure of sensitive information. Transparent policy communication ensures that employees understand what data is monitored and what remains private. Combining RBAC with user-facing privacy controls helps organizations enforce security measures while maintaining trust and regulatory compliance.
Selecting the right device strategy depends on multiple factors, including workforce requirements, regulatory obligations, and budget constraints. Organizations with highly mobile workforces may benefit from BYOD, while those in regulated industries may prefer corporate-owned or COPE models. In reality, most enterprises adopt a hybrid approach that combines elements of all three.
A successful strategy requires more than choosing a model; it demands a robust management solution that ensures consistency and security across all devices. Hexnode enables organizations to implement such strategies effectively by providing centralized control, automation, and scalability.
Hexnode stands out as the right choice for enterprises navigating BYOD and corporate-owned device strategies because it delivers unified endpoint management without adding operational complexity. It enables IT teams to enforce consistent security policies across diverse device environments while maintaining a clear separation between corporate and personal data.
Key capabilities include:
By supporting BYOD, COPE, and corporate-owned models within a single platform, Hexnode empowers enterprises to adopt flexible mobility strategies without compromising security or user experience.
BYOD and corporate-owned devices each offer distinct advantages and challenges. While BYOD enhances flexibility, it introduces security risks that organizations must address proactively. Corporate-owned devices provide stronger control but require higher investment. Ultimately, enterprises need a unified solution to manage these diverse environments securely. Hexnode stands out as a reliable platform that enables organizations to secure, manage, and scale their device strategies with confidence.
Manage and secure BYOD and corporate devices with ease using Hexnode.
Start Your Free Trial!What is the main difference between BYOD and corporate-owned devices?
The main difference lies in ownership and control. BYOD devices belong to employees, limiting organizational control, while corporate-owned devices are fully managed by the organization, enabling stronger security enforcement.
Is BYOD less secure than corporate-owned devices?
BYOD can be less secure if not properly managed, as organizations have limited control over personal devices. However, with the right tools like Hexnode, enterprises can mitigate these risks effectively.
What is corporate owned personally enabled (COPE)?
COPE is a model where organizations provide devices but allow limited personal use. It combines the control of corporate-owned devices with the flexibility of BYOD.
How can enterprises secure BYOD devices effectively?
Enterprises can secure BYOD devices using containerization, strong authentication, encryption, and unified endpoint management solutions like Hexnode.
Which model is best for enterprise security?
There is no one-size-fits-all answer. A hybrid approach supported by a robust UEM platform like Hexnode offers the best balance between security and flexibility.