The True TCO of Unified Endpoint Management: A Financial Model for 2026
Learn the hidden costs in UEM tools, comparing Intune and Hexnode to optimize IT spending.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

SAP SQL Injection 2026 is a critical vulnerability disclosed during SAP’s April 2026 Security Patch Day. Officially tracked as CVE-2026-27681, it affects SAP Business Planning and Consolidation (BPC) and SAP Business Warehouse (BW).
This vulnerability brings renewed focus to how enterprise systems are accessed. While SAP provides the necessary patch, organizations still need to evaluate the security posture of the endpoints interacting with these systems. Hexnode plays a key role here by enabling compliance enforcement, access control integration, and endpoint-level security policies that help reduce overall exposure.
SAP SQL Injection 2026 is a critical vulnerability (CVSS 9.9) in SAP BPC and SAP BW that allows authenticated users to execute unauthorized SQL queries due to insufficient authorization checks.
This vulnerability allows attackers to read, modify, or delete sensitive enterprise data in SAP BPC and BW systems.
As a result, organizations may face:
Therefore, this vulnerability presents a high-impact risk, especially in environments where SAP supports financial planning and reporting.
This works by allowing crafted SQL queries to execute due to missing or insufficient authorization checks.
In practice, the process works as follows:
To fix it, apply SAP Security Note 3719353 and restrict unnecessary access to affected systems.
Specifically, teams should:
SAP has recommended prioritizing this patch due to its critical severity.
This vulnerability requires authenticated access, which makes endpoint security an important factor in reducing risk.
For example, risk increases when:
Therefore, endpoint posture directly influences overall risk exposure.
Hexnode helps reduce this risk by enforcing device compliance, strengthening endpoint controls, and supporting access decisions through device posture.
Hexnode allows administrators to define compliance policies across platforms.
If devices fail checks, such as outdated OS versions or disabled encryption, the system marks them as non-compliant.
Hexnode integrates with Microsoft Entra ID Conditional Access.
As a result:
Hexnode supports several controls that strengthen endpoint security, including:
In addition, Hexnode supports patch and update management which helps IT teams keep devices secure and up to date.
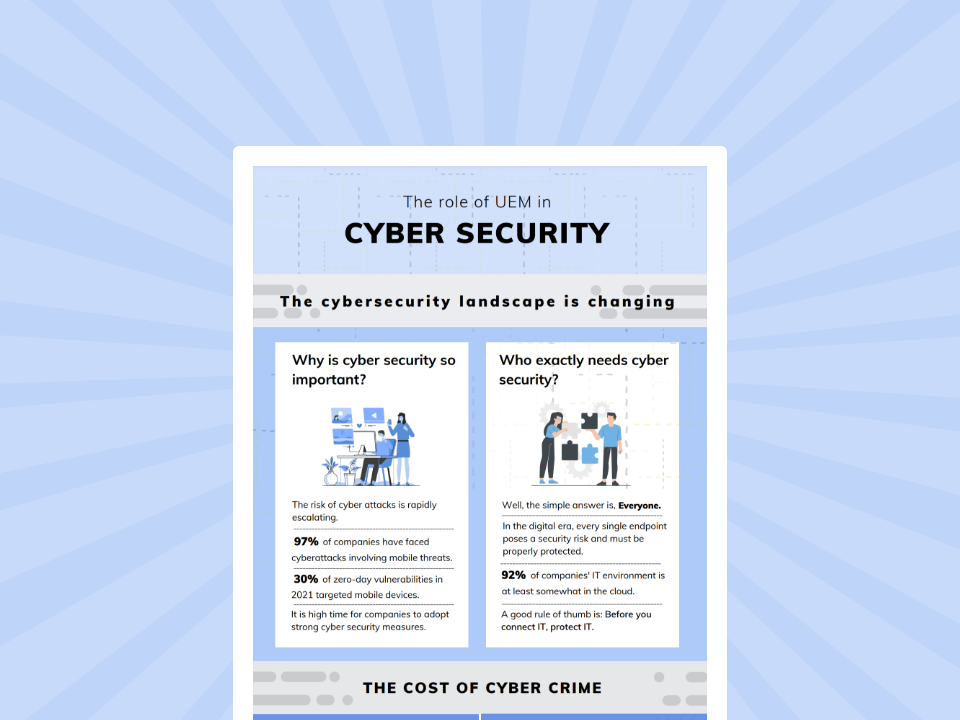
See how UEM strengthens cybersecurity by securing endpoints, enforcing policies, and reducing enterprise attack surfaces.
Featured resource
The role of UEM in cyber security
SAP SQL Injection 2026 is a critical vulnerability that must be patched immediately, but risk reduction also depends on controlling access and maintaining secure endpoints.
Ultimately, the most effective approach combines:
Learn how Hexnode helps strengthen endpoint security posture
Sign up now