Operating in the DACH region means navigating some of the world’s most stringent data protection mandates.
For IT leaders in risk-averse industries, the fear of crushing GDPR non-compliance penalties is a constant, looming pressure. However, what if you could transform this regulatory burden into a powerful business asset?
This article explores the realities of modern GDPR enforcement and demonstrates how organizations can shift from reactive panic to proactive security.
The High Stakes of Non-Compliance in the DACH Region
When it comes to data privacy, Germany, Austria, and Switzerland (the DACH region) operate under a magnifying glass.
The baseline is the European Union’s General Data Protection Regulation (GDPR), but local enforcement is often amplified by national laws such as Germany’s Federal Data Protection Act (BDSG) and Switzerland’s recently revised Federal Act on Data Protection (nFADP). Together, these frameworks create an environment where data protection is not just a suggestion, but a foundational requirement for doing business.
For many IT and security officers, the immediate pain point is the financial threat. The realities of recent GDPR enforcement actions highlight a critical trend: data protection authorities (like the BfDI in Germany) are no longer just levying fines against companies that suffer massive data breaches. Increasingly, heavy penalties are being handed down for failing to demonstrate compliance. If a regulatory body audits your organization and you cannot explicitly prove that proper Technical and Organizational Measures (TOMs) are in place to protect endpoint data, you are liable, even if a breach hasn’t occurred.
| Risk Area | Immediate Impact | Long-Term Consequence |
|---|---|---|
| Regulatory | GDPR Fines (up to €20M or 4% of global turnover). | Increased audit frequency; mandatory operational changes. |
| Reputational | Public notification of breach/failure; negative press. | Permanent loss of client trust; difficulty acquiring new business in DACH. |
| Operational | Court orders halting data processing; device seizures. | Total business standstill during investigation; massive remediation costs. |
However, regulatory fines are only the tip of the iceberg. The secondary costs of non-compliance can be catastrophic, particularly for risk-averse industries such as finance, healthcare, and legal services.
A public compliance failure leads to severe reputational damage, the immediate loss of client trust, and crippling operational downtime while regulators dissect your IT infrastructure. In the DACH market, where privacy is culturally ingrained, losing trust often means losing the business entirely.
Reframing Compliance: From Burden to Competitive Edge
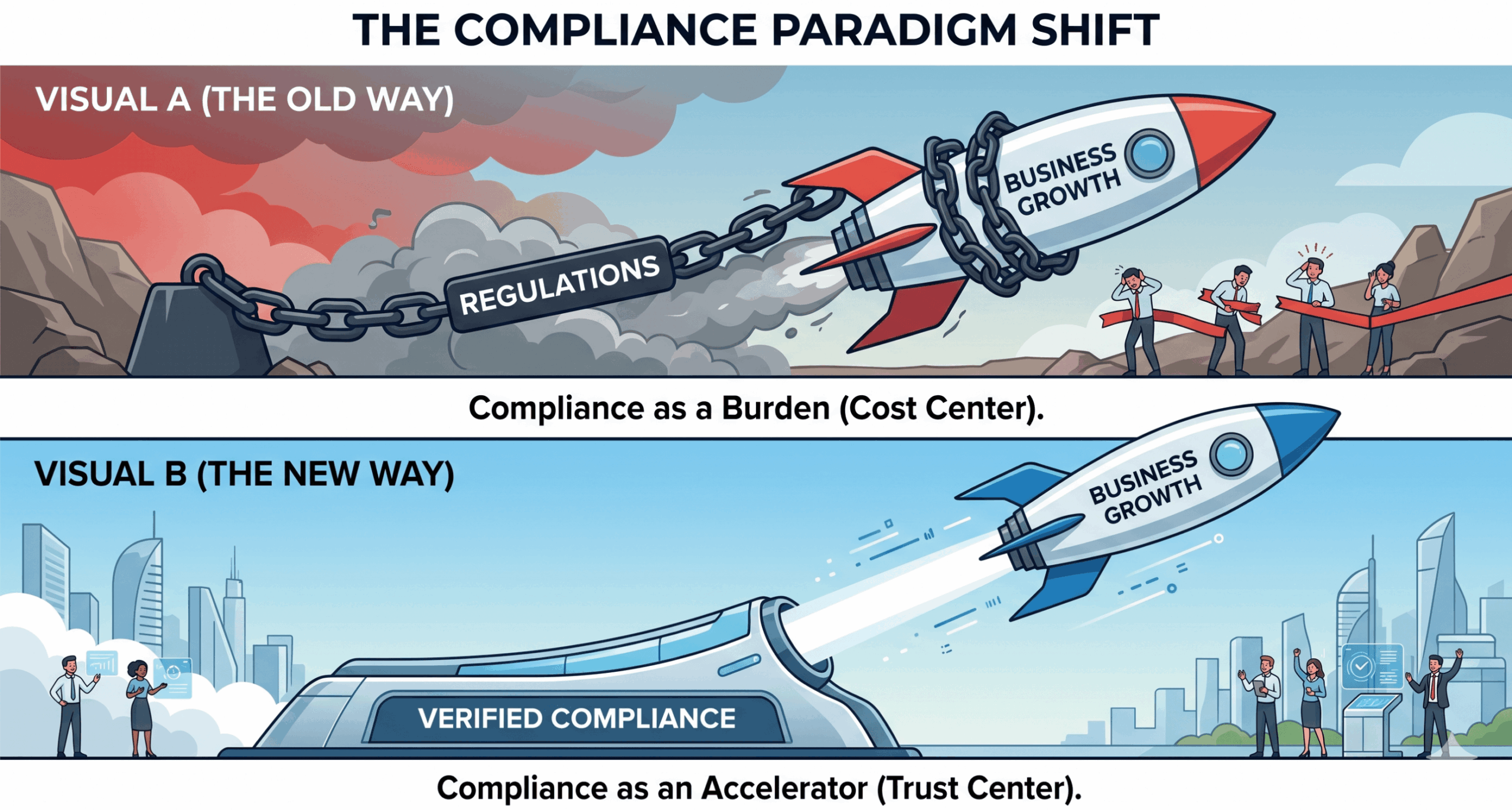
The sheer volume of red tape often causes organizations to view compliance as a heavy tax on their time and resources. But savvy IT leaders are flipping this narrative.
By establishing a robust, easily demonstrable compliance posture, businesses can turn regulatory adherence into a distinct market differentiator.
In today’s B2B ecosystem, large enterprises and risk-averse partners actively seek vendors with impeccable security credentials. When pitching to a major German bank or a Swiss pharmaceutical company, the vendor risk assessment phase can drag on for months. If your IT infrastructure is highly transparent, secure, and compliant by design, you drastically accelerate these sales cycles. You transition from being a vendor that merely “checks the boxes” to a strategic partner that mitigates risk.
The Role of Endpoint Visibility as Indisputable Evidence
Abstract privacy policies written in a company handbook mean very little without the technical infrastructure to enforce them. In the context of IT, endpoint management is where the rubber meets the road. Total endpoint visibility is the core requirement for proving regulatory adherence.
You Can’t Protect What You Can’t See
The shift toward distributed workforces, hybrid environments, and Bring Your Own Device (BYOD) policies has created a massive blind spot for IT teams.
Shadow IT, where employees use unsanctioned apps or unmanaged devices for corporate work is a compliance nightmare waiting to happen. You cannot guarantee the security of a file if you do not know which device it is saved on, or whether that device is operating on a secure network.
| Visibility Metric needed | Regulatory Context (GDPR/nFADP) | How UEM Provides Evidence |
|---|---|---|
| Encryption Status | Ensure Confidentiality (Art. 32 GDPR) | Real-time report showing BitLocker/FileVault active on all devices. |
| OS Patch Level | Maintain Integrity & Resilience (Art. 32 GDPR) | Dashboard view of devices lacking critical security updates. |
| App Inventory | Data Minimization; Prevent unauthorized processing. | List of all installed apps; instant alerts for blacklisted software. |
| Device Location | Cross-border data transfer restrictions. | Geofencing logs proving devices containing sensitive data stayed within the EU/DACH. |
Real-time endpoint visibility acts as your most tangible evidence during a compliance audit. When an auditor asks how you protect customer data, you need to be able to show them a live dashboard, not a static spreadsheet. Visibility means tracking data flow, monitoring app installations, and ensuring device health across the entire corporate fleet.
Automating Audit Trails and Reducing Human Error
Even with the best intentions, maintaining compliance manually is a losing battle. The sheer volume of endpoints, operating system updates, and user activities makes human oversight fundamentally unscalable. To truly master DACH regulations, organizations must rely on automation.
The Danger of Manual Compliance
Relying on spreadsheets, periodic manual checks, and employee self-reporting inevitably leads to critical oversights. Humans are inherently prone to error.
An IT admin might forget to log a retired laptop, or an employee might postpone a crucial security patch for weeks. In the eyes of a GDPR auditor, a forgotten security patch that leads to a vulnerability is a massive compliance failure.
Automation cures these operational bottlenecks. By implementing continuous, automated logging, organizations can generate instant, accurate audit trails on demand. Automation enforces baseline security policies without relying on end-user intervention. For example, if a device falls out of compliance (e.g., an employee disables their firewall), automated remediation protocols can instantly restrict that device’s access to corporate servers until the issue is fixed.
Furthermore, automating these processes drastically streamlines reporting. Instead of spending weeks preparing for an external audit, compliance officers can pull comprehensive reports with a few clicks, proving that technical safeguards are not just documented, but actively and uniformly enforced.
Hexnode: Your Enabler for Frictionless Endpoint Compliance
To achieve this level of visibility and automation, organizations need the right toolset. This is where Hexnode’s Unified Endpoint Management (UEM) steps in, not just as a device manager, but as a strategic compliance partner tailored for the demands of the DACH market.
Centralizing Policy Enforcement
Hexnode allows IT teams to apply zero-trust principles and granular security configurations from a single, centralized console across all operating systems (Windows, macOS, iOS, Android).
This unified approach ensures that a security policy created for your Munich headquarters is flawlessly enforced on a remote worker’s tablet in Zurich. Through Hexnode, IT can mandate device encryption (like BitLocker for Windows and FileVault for macOS), configure strong passcode policies, and enforce app blacklisting to prevent data leakage via malicious or unsanctioned applications.
Out-of-the-Box Reporting
Proving compliance is just as important as being compliant. Hexnode shines in its ability to generate automated, out-of-the-box reports that satisfy strict DACH auditors. IT teams can instantly pull reports on device encryption status, patch levels, and policy violations.
| Feature | Description | Compliance Benefit |
|---|---|---|
| Remote Wipe/Lock | Instant repurposing or sanitization of lost/stolen devices. | Prevents data breaches, satisfying Art. 32 GDPR immediately. |
| Kiosk Mode | Restricts devices to specific apps/webpages. | Ensures devices are used only for intended, secure business purposes. |
| Patch Management | Automates OS and app updates. | Eliminates vulnerabilities; proves proactive technical measures. |
| BYOD Containerization | Separates corporate data from personal data on user devices. | Satisfies data segregation requirements without invading user privacy. |
Consider a hypothetical scenario: A wealth management firm based in Zurich is undergoing a rigorous compliance audit under the new FADP guidelines. The auditors demand proof that client financial data is protected on mobile devices. Using Hexnode, the firm’s IT director instantly pulls a report showing that 100% of the company fleet has mandatory encryption enabled, geofencing is active to restrict access outside approved regions, and any lost devices are configured to auto-wipe. What could have been a stressful, multi-week investigation is resolved cleanly and confidently in a matter of hours.
Conclusion: Securing Your Future in the DACH Market
In the highly regulated landscapes of Germany, Austria, and Switzerland, compliance is far more than an exercise in avoiding hefty fines; it is an opportunity to prove your reliability and secure your future. By adopting proactive endpoint visibility and automating your audit trails, you eliminate human error and safeguard your most critical data.
Leveraging a powerful UEM solution like Hexnode automates the heavy lifting, turning complex regulatory requirements into seamlessly executed IT policies. When you can definitively prove your security posture, you don’t just survive an audit, you win the trust of your market.
Experience Frictionless DACH Compliance with Hexnode
Secure your devices, protect your data, and turn your compliance posture into your strongest asset.
Start Your Free Trial




