IT Admin’s Guide to Patch Management with Hexnode
Hexnode combines UEM and patch management to simplify patch identification, deployment, rollback, and reporting,

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

In 2024, the cybersecurity industry hit an alarming milestone: over 40,000 Common Vulnerabilities and Exposures (CVEs) were published in a single year. That is an average of 108 new vulnerabilities every single day.
For the average IT Operations team, this number isn’t just a statistic; it is a tidal wave.
Most organizations are currently stuck in a “Scan and Scramble” loop. The Security team runs a scanner and hands over a 300-page PDF report to the IT team. This report contains thousands of “Critical” and “High” alerts. The IT Administrator, already buried in helpdesk tickets, looks at this massive backlog and asks the impossible question: “Where do I even start?”
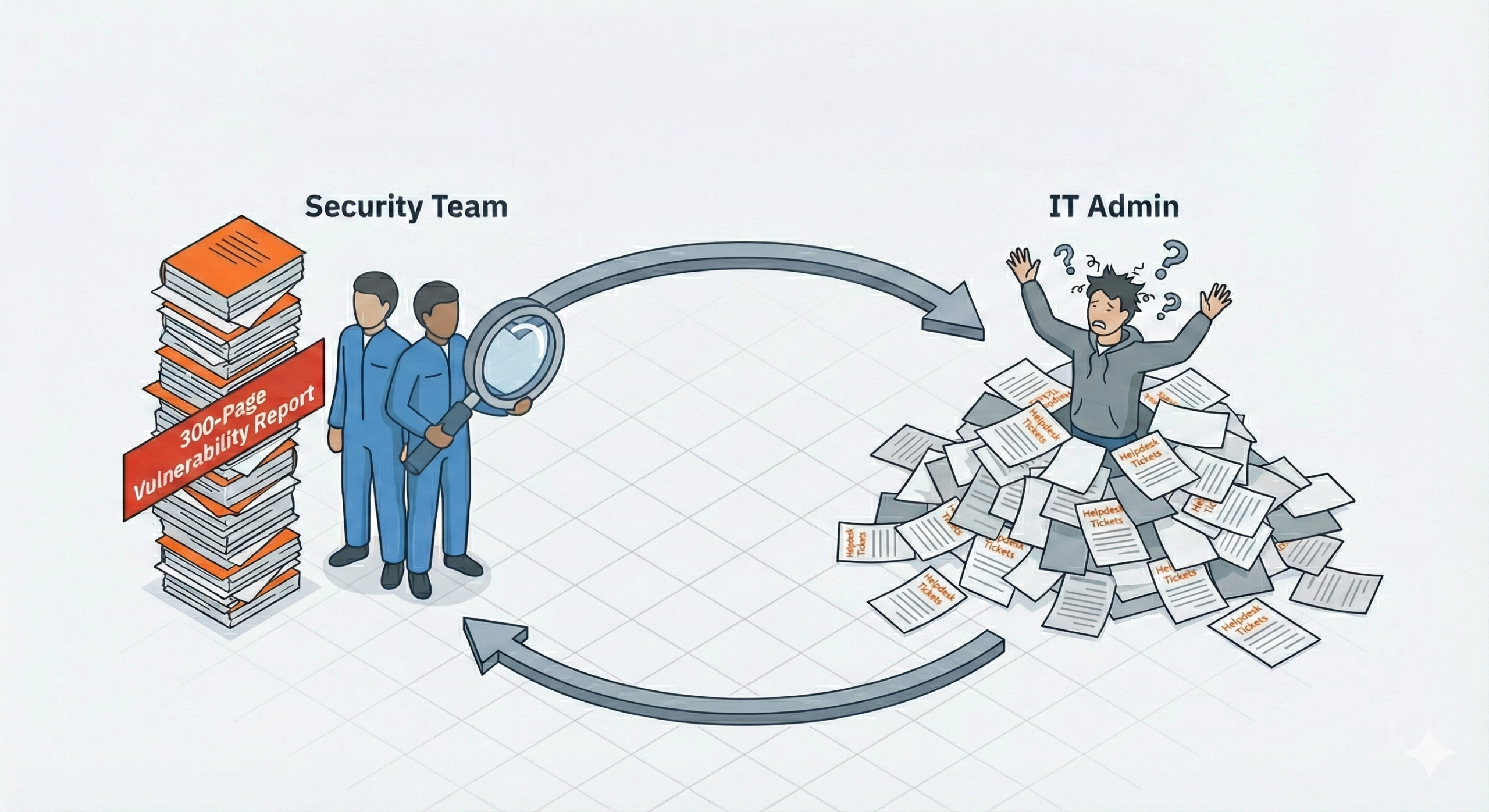
In this blog, we dissect the operational silo between Security and IT, explain why “scanning” is not “fixing,” and demonstrate how to move from a reactive “Scan and Scramble” model to a proactive, automated patching architecture.
Vulnerability Management (VM) is the strategic process of identifying, categorizing, and prioritizing security risks, whereas Patch Management (PM) is the tactical execution of code deployment to remediate those risks. Confusing the diagnosis (VM) with the cure (PM) is the primary reason why organizations fail to close the remediation gap, leaving them exposed to known exploits.
To solve the backlog, we first have to agree on what we are actually doing. In many organizations, “Patch Management” and “Vulnerability Management” are used interchangeably in budget meetings. In the server room, however, they are two completely different architectural disciplines.
| Feature | Vulnerability Management (VM) | Patch Management (PM) |
|---|---|---|
| Primary Goal | “What is broken?” (Discovery & Risk Scoring) | “How do we fix it?” (Deployment & Verification) |
| Typical Owner | CISO / Security Operations (SecOps) | IT Operations / SysAdmins |
| The Output | A list of CVEs and Risk Scores (e.g., CVSS 9.8) | A deployed .msi, registry change, or kernel update |
| The Limitation | It generally cannot fix the problem; it only alerts you to it | It doesn’t always know which patch is the highest priority; only what is available |
If you want to know where your next breach is coming from, look at the patch you ignored three months ago.
The industry data is damning: 60% of data breaches involve vulnerabilities for which a patch was already available but not applied. We call this the Remediation Gap, the deadly window of time between when a vendor releases a fix and when you actually deploy it.
If we understand the risks, why are we still slow to patch? In most organizations, it comes down to three common challenges.
Many patch tools treat these as equal priorities. In reality, the exposed server is the urgent threat. Without risk-based prioritization, teams may focus on low-impact systems while high-risk assets remain vulnerable.
The old mantra of “patch everything within 30 days” is dead. It is mathematically impossible. When you have 500 servers and 10,000 vulnerabilities, trying to fix everything means you fix nothing of importance in time.
The solution is not to patch faster; it is to patch smarter. This is the shift to Risk-Based Vulnerability Management (RBVM).
RBVM moves the goalpost from “Patch Everything” to “Patch What Matters.” It acknowledges that a CVSS 9.8 vulnerability on a test server behind a firewall is less dangerous than a CVSS 7.5 vulnerability on an exposed VPN gateway that is currently being exploited in the wild.
To bridge the gap, you need to integrate threat intelligence into your patching workflow. You can no longer rely on a simple list of CVEs. You need a prioritization logic that triangulates three data points:

This is where the architecture comes together. Your Vulnerability Management (VM) tool provides the intelligence (the “What”), but it lacks hands. Hexnode UEM acts as the Execution Arm of your VM strategy.
The VM tool sees the threat; Hexnode delivers the payload. By mapping your “High Risk” vulnerability reports directly to Hexnode’s smart device groups, you turn a passive PDF report into an active defense posture.

Download the one-pager to discover how Hexnode simplifies patch management and strengthens device security.
Get the one pagerBridging the remediation gap requires moving away from manual, click-to-install patching and toward automated, policy-driven deployment. The goal is not just to detect vulnerabilities, but to operationalize response at scale.
Here’s what that looks like in practice.
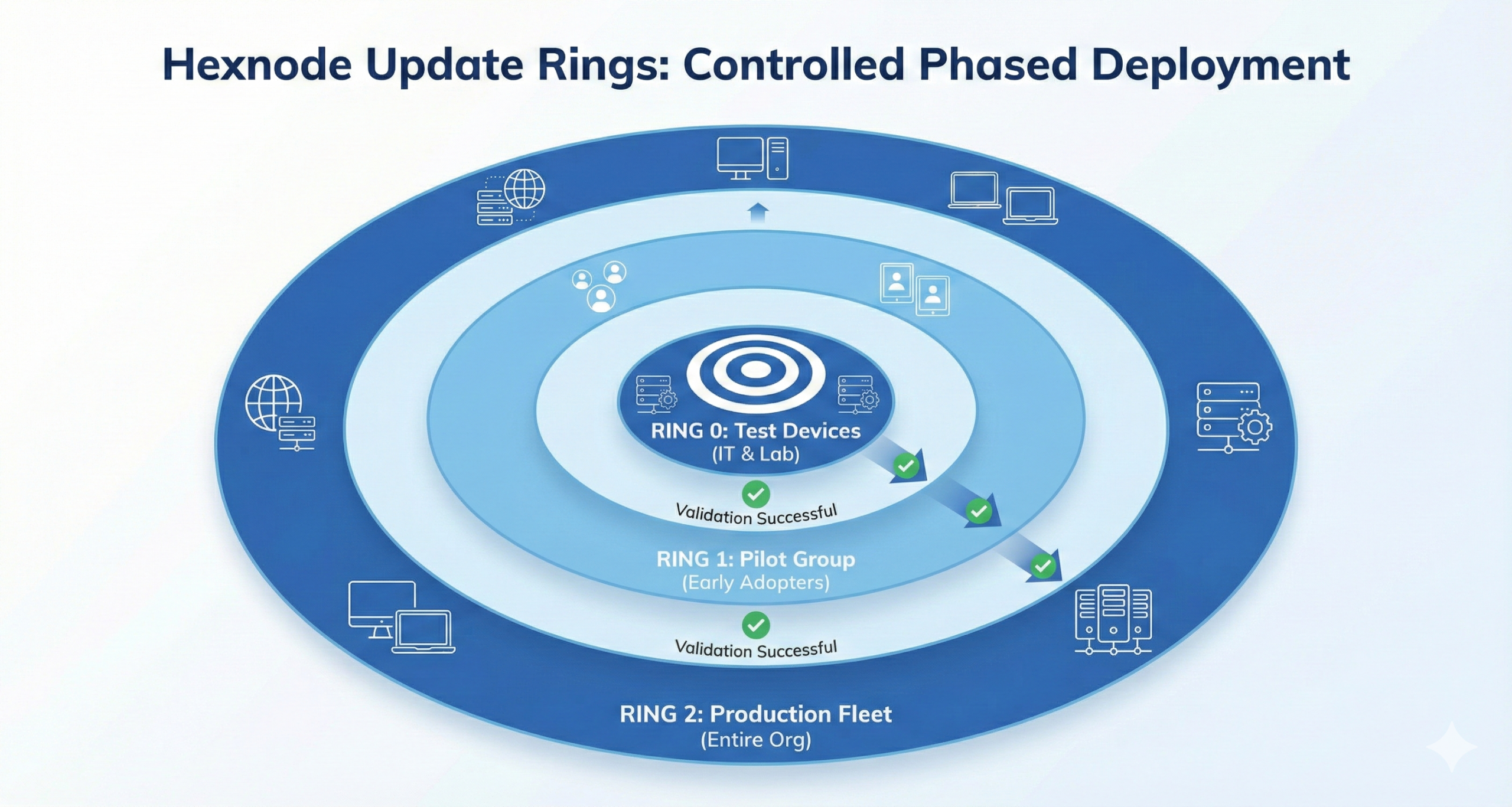
This approach transforms patching from a high-risk event into a controlled rollout. By the time updates reach mission-critical devices, they have already been tested in real-world conditions.
This capability buys valuable time, shrinking the attacker’s window of opportunity while maintaining operational control.
If you secure the operating system but ignore the applications, your system is still exposed.
While most IT teams have a handle on Windows and macOS updates, the real “Shadow IT” risk lies in third-party software, browsers, PDF readers, and conferencing tools. In 2024, Google Chrome alone saw a staggering 1,840% increase in exploited vulnerabilities, while Microsoft Office exploits spiked by 433%.
OS updates are relatively easy; they come from a single, trusted pipe (Apple or Microsoft). Third-party apps are chaotic.
This inconsistency creates a “Patch Gap” where critical software remains outdated simply because the user clicked “Remind Me Later.”
To close this gap, you must remove the user from the equation. Hexnode allows you to treat 3rd party apps with the same rigor as OS updates using Mandatory App Policies and Silent Installation commands.
Stop relying on “Auto-Update” checkboxes inside apps. Centralize your 3rd party patch management in Hexnode to ensure that your browser security is as robust as your kernel security.
We need to fundamentally change how we measure success in cybersecurity. For too long, the industry has worshiped the “Clean Scan”, the idea that if we just buy enough tools, we can reach zero vulnerabilities.
That era is over. In a world with 108 new CVEs a day, a clean scan is impossible.
Security audits care about what you know (Vulnerability Management). Hackers care about what you haven’t fixed (Patch Management). You can have the most expensive Tenable dashboard in the world, but if your Mean Time to Remediate (MTTR) is 60 days, you are just as exposed as the company that scans nothing.
The goal of 2026 is not perfection; it is resilience. It is building an architecture where the time between detection and correction is measured in minutes, not months.
Automate your patch deployment and close the remediation gap with Hexnode.
Sign Up TodayQ: What is the difference between patch management and vulnerability management?
A: Vulnerability Management is the strategic process of identifying and prioritizing security risks (the diagnosis), whereas Patch Management is the tactical execution of code deployment to remediate those risks (the cure). While vulnerability management focuses on discovery and risk scoring (e.g., CVSS), automated patch management ensures the actual fix is delivered to the endpoint to close the security hole.
Q: Can patch management tools detect vulnerabilities?
A: Generally, no. Patch management tools identify “missing updates,” but they lack the context of a true vulnerability scanner. They cannot tell you if a missing patch is a low-risk bug or a critical exploit actively used by hackers. This is why organizations must adopt Risk-based vulnerability management (RBVM) strategies, which combine threat intelligence with patching workflows to handle CVE prioritization effectively.
Q: How does Hexnode help with Zero-Day vulnerabilities?
A: When a vendor patch is not yet available for a critical threat, Hexnode patch policies allow administrators to deploy Zero-day mitigation tactics immediately. Using the “Execute Custom Script” feature, IT teams can disable vulnerable services, change registry keys, or block specific ports to neutralize the threat vector until the official patch is released.
Q: Why is Mean Time to Remediate (MTTR) important?
A: Mean Time to Remediate (MTTR) is the critical metric that measures how long your infrastructure remains exposed after a vulnerability is detected. A high MTTR means a wider window of opportunity for attackers. The goal of integrating Hexnode with your security stack is to shift from a “clean scan” mentality to a resilient architecture that drastically reduces MTTR.