What is Zero Trust Network Access (ZTNA) and why is it the future of cloud network security?
Master the essentials to replace outdated VPNs with a secure, identity-driven framework for your workforce.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

Mobile devices now sit at the center of most enterprise workflows. That also makes them the center of most modern breaches. In 2026, the biggest mobile security threats don’t always look like “malware on a phone.” Instead, they look like AI-powered phishing, session hijacking, and fleet-wide misconfiguration that spreads in minutes.
If you manage a large, dedicated deployment like POS terminals, warehouse scanners, kiosks, rugged handhelds, or healthcare tablets, you already know the truth: security failures become operational outages.
This guide breaks down the top mobile device security threats of 2026 and shows how IT Ops managers and MSPs can defend at scale using Hexnode, modern identity controls, and a Zero Trust Mobile approach.
Recent global data shows that 85% of organizations report a significant surge in mobile-targeted attacks. Hackers have realized that hardened servers are difficult to crack, but the mobile device carrying active OAuth tokens, biometric data, and persistent cloud sessions is the path of least resistance to identity compromise.
As a result, mobile is no longer one of many endpoints. It’s often the fastest path to identity compromise, and identity compromise is often the fastest path to everything else.
Managing a fleet of POS terminals, warehouse scanners, or healthcare tablets creates unique vulnerabilities. A single configuration drift across 10,000 devices isn’t just a security risk; it’s a potential operational blackout.
Without mobile threat protection, a single Zombie Device (an unpatched or forgotten endpoint) can provide a permanent foothold for lateral movement within your network.
A large fleet creates unique failure modes:
Without automation, even small mobile risks become big incidents.

Mobile risks have evolved. Attackers don’t need to deploy noisy malware on every device.
Instead, they can:
In short, the modern attacker scales. Your defense must scale, too.
In 2026, the consequences of a breach are no longer confined to data loss; they manifest as immediate operational paralysis. As enterprises transition to hyper-connected fleets, the blast radius of a single exploit has expanded.
For industries like logistics, retail, and healthcare, dedicated devices are the primary engines of revenue. When these devices face mobile security threats, the result is not just a digital risk; it is a total business stoppage.
In a mobile-first enterprise, rugged device security is the literal equivalent of operational uptime.
Modern adversaries have abandoned the pursuit of encrypted files in favor of session hijacking. By targeting active OAuth tokens and session cookies, attackers can bypass traditional MFA and gain legitimate access to:
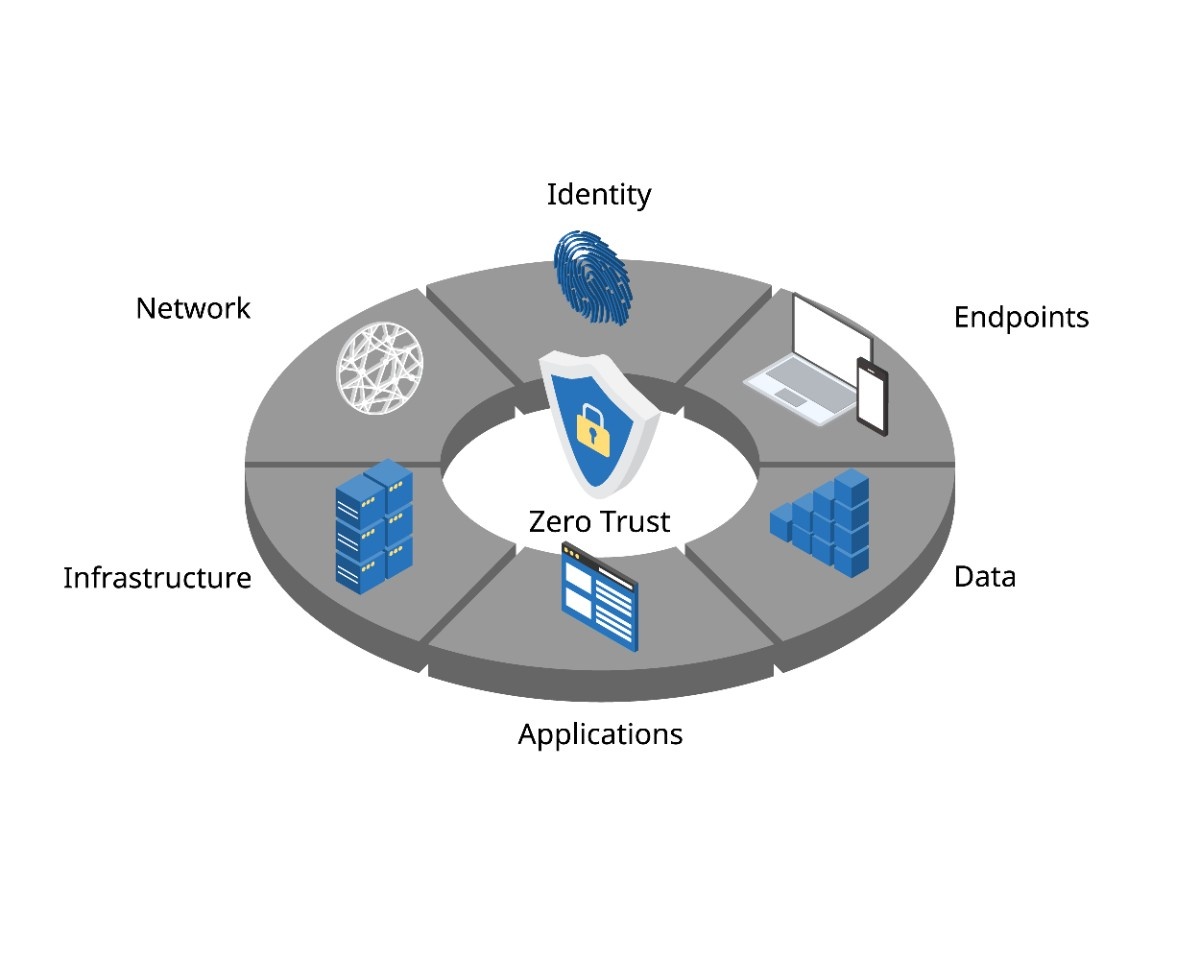
To counter this, a Zero Trust Mobile strategy is mandatory. Organizations must transition from static passwords to continuous conditional access and hardware-attested device trust.
While security awareness training remains a baseline requirement, it is increasingly ineffective against the interactive nature of 2026 exploits. Attackers now leverage AI to create high-pressure, multi-vector scenarios:
The solution is not more training, but autonomous Mobile Threat Protection. You need system-level controls that refuse high-risk actions by default ensuring that security is never dependent on human judgment during a crisis.
Attackers use Generative AI to clone executive voices (Vishing) and craft hyper-realistic Smishing (SMS) campaigns to trick admins into approving rogue device enrollments.

Malware like RatON intercepts NFC signals to facilitate unauthorized payments or badge cloning on customer-facing handhelds.
Attackers force 5G devices to downgrade to legacy, unencrypted protocols to intercept field telemetry and operational data.
Forgotten, unpatched devices remain connected to the network, serving as silent entry points for lateral movement.
Attackers steal OAuth tokens or session cookies to bypass MFA and gain legitimate access to admin consoles and SaaS portals.
In 2026, mobile security threats move too fast for manual oversight. A reactive strategy is no longer viable for IT Operations Managers, especially for dedicated fleets where high device counts and constant physical exposure make the cost of downtime immediate and severe.
To stay resilient, you need a living security posture focused on:
Hexnode’s shift toward AI-assisted operations, specifically through Hexnode Genie, reflects the future of fleet security. By utilizing natural language scripting and automation, Hexnode delivers faster enforcement and better outcomes with fewer clicks.
Fleet security in 2026 is never “set and forget.” It is a continuous, automated, and identity-driven process. Leveraging an advanced UEM platform transforms your mobile fleet from a potential liability into a secure, high-performance asset.
Join Hexnode on neutralizing AI-driven social engineering and securing Zombie devices.
Try Hexnode nowFor enterprise fleets, the most dangerous risks typically include:
These threats focus on identity, sessions, and operational disruption—not just classic malware.
A UEM can’t block a phone call. However, it can dramatically reduce the impact.
Hexnode UEM helps by:
In other words, UEM turns a convincing call into an unapproved request that fails by design.
A zombie device is an endpoint that stays online but falls out of normal operational oversight. It may be unused, rarely patched, or poorly monitored.
It’s risky because it becomes an unnoticed entry point. The best fix is automation:
Yes. Dedicated and rugged devices often:
That’s why Rugged Device Security needs specialized controls like kiosk lockdown, peripheral restrictions (NFC/USB), and hardened network policies.