Have you ever wondered how challenges operate? They are often two-sided, advantageous for some while being disastrous for some others at the same time! The covid-19 pandemic, which we are still struggling to conquer, is no different. Well, you guessed it right, the pandemic isn’t “disastrous for some”; it’s, in fact, “disastrous for all yet favoring some in certain non-related aspects.” This was particularly true for IT models that supported remote work. With the shelter-in-place order and commuting becoming impossible, remote work adoption became ubiquitous. But, that’s not all; it also witnessed a new IT model called “anywhere operations,” extending far and wide and not just restricted to remote work and support for the same.
What is meant by anywhere operations?
Anywhere operations model- a less heard term during the pre-covid times, was brought to the limelight as the “answer” that helps ensure post-Covid-19 productivity. However, the implementation of the anywhere operations model was not at all a well-planned one. Instead, the sudden outbreak of the pandemic and the subsequent shift in workspaces brought by it left IT companies with no choice but to go forward with its implementation.
With this model, a blended virtual and physical experience is created for employees and customers alike. Overall, it is an integrated system that focuses on clients and employees while ensuring businesses accessibility from anywhere in the globe.
“According to a recent report published by Gartner, by the end of 2023, close to 40% of companies will have implemented anywhere operations to provide an optimized experience among their employees and consumers.”
Technology building blocks for anywhere operations
Anywhere operations model consists of certain technology building blocks that help create an unrestrained digital workspace.
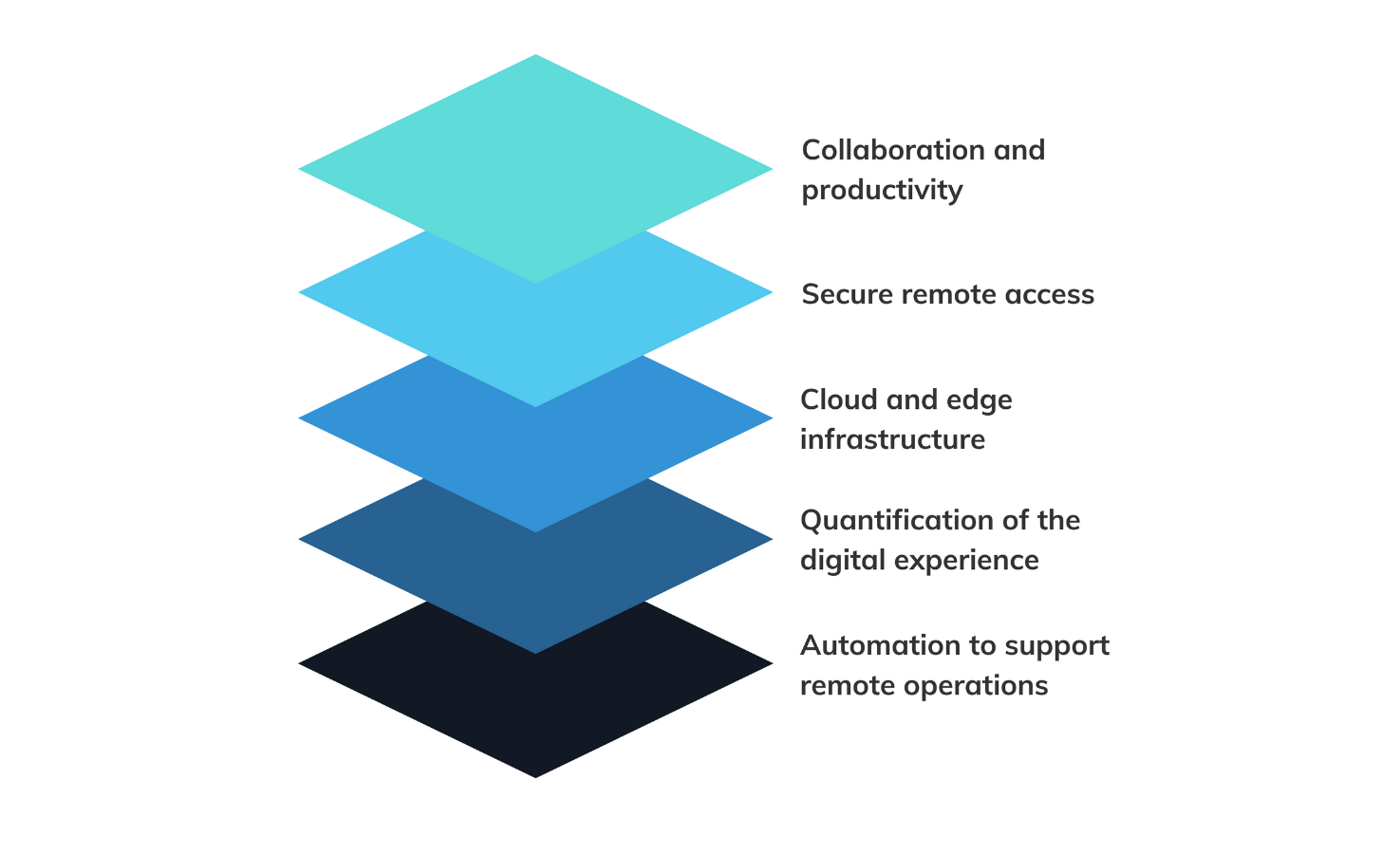
Collaboration and productivity
It comprises workstream collaboration, meeting solutions, cloud office suites, digital whiteboarding and innovative workspaces
Secure remote access
Password-less and multi-factor authentication, zero-trust network access (ZTNA), secure access service edge (SASE), and identity as the new security perimeter are its key elements
Cloud and edge infrastructure
This includes distributed cloud, the internet of things (IoT), API gateways, artificial intelligence (AI) at the edge and edge processing.
Quantification of the digital experience
This is mainly about digital experience monitoring, workplace analytics, remote support and contactless interactions.
Automation to support remote operations
Its components are AI for IT operations (AIOps), endpoint management, SaaS management platforms, self-service, and zero-touch provisioning.
Benefits of anywhere operations model
Anywhere operations model offers a lot of benefits. Some of these include:
Remote work and anywhere operations- A comparison

Sometimes when we hear the term anywhere operations, we often have this tendency to mistake it for remote work. Well, let me rectify that. As clearly indicated by the term, the anywhere operations model follows an operate-from-anywhere strategy. This includes a wide range of aspects like employees working from home, but the difference is that it is not just restricted to that.

How Hexnode supports an anywhere operations model?
Anywhere operations model mainly aims to break all location barriers when it comes to providing services, be it for employees, customers or a mix of both. Most modern Unified Endpoint Management solutions follow and even support similar modes of operation. With Hexnode, you can easily support and even secure an anywhere operations model. Some of the managed aspects include:
Enrollment methods

While considering an anywhere operations model, the importance of remotely deploying and onboarding devices need no further emphasis. Hexnode’s Hexnode’s no-touch enrollment options make remote device deployment and enrollment options a no-brainer.
With Apple Business Manager (ABM), you can easily deploy devices in bulk with automatically applied settings and configurations upon initial device startup making it possible to use it right out of the box. Apple School Manager (ASM) also has a similar approach allowing you to deploy devices to organizations and assign them to the required individuals. Here, all you need to do is enroll your institution in Apple school manager and enroll your devices in your portal. You can directly purchase your devices from Apple or an authorized reseller.
Yet another notable enrollment method is the Knox Mobile Enrollment (KME) offered by Samsung Knox. With this method, you have an automated enrollment method that helps you enroll enterprise devices in bulk with minimal effort from the user end. And lastly, there is ROM-based enrollment. This method is the result of the collaboration of UEM and the OEM vendor. With the specially configured ROM granting privileges to UEM, the device will be enrolled automatically when the user first turns on the device.
Automated MDM enrollment: Your key to easy device deployment
Remote access features
When you manage a fleet of devices from a distant location, chances of device issues or failures are something you can never ignore. In a world where time is money, a downtime is never a feasible option. This is precisely where remote view and control become significant.
The remote view feature allows the admin to view user devices in real-time from the Hexnode portal. With such a feature in place, you can remotely find the device issues and give appropriate guidance, eliminating the need for technicians to physically reach the device location to solve problems. It also allows you to monitor devices and keep track of user actions. With Hexnode, you can remotely view the devices enrolled in Android Enterprise as Device owner, non-Android Enterprise devices running version 5 and above and macOS devices. Next comes remote control, allowing you to control and perform actions on user devices right from the Hexnode portal. This is advantageous as it will enable you to perform actions on the end device and solve issues as and when they appear without relying on the end-user.
MDM remote access: The essential tool for real-time troubleshooting
Security management

Security always comes first in enterprises. With the widespread adoption of practices like work from home, we can now access corporate data from literally anywhere. Though it makes remote work easier, it has also created a need to focus more on the vulnerable factor-security.
With Hexnode, you can easily safeguard your devices. The features like passwords and encryption allow you to secure your end devices and ensure device access to authorized users alone. In the present scenario, we can’t predict the entry points of vulnerabilities, so it’s often advisable to safeguard them from all potential threats. For this, the best option is setting restrictions on devices connecting to user devices. Imposing restrictions on USB, other data transfer, copy-paste options, limiting your devices to trusted Wi-Fi and enforcing the use of VPN can help ensure your device security. Further, with automated compliance scans and reports, you can closely monitor the activities at the user end and take appropriate measures to satisfy the compliance criteria in case the device falls out of compliance.
App management
In this internet-centric world, what we should never forget is that the malicious actors and the vulnerabilities they have created are so prominent that it’s often hard to distinguish between what’s genuine and what’s compromised. This is applicable even for apps. Hexnode makes it possible to deploy secure applications to managed devices remotely.
Hexnode’s integration with Apple Volume Purchase Program (VPP) has made Zero-touch app deployment possible. Now enterprises can purchase, deploy and manage applications in bulk and install them on the user devices with zero user intervention. Well, it also includes extensive app management capabilities with in-app configurations allowing you to pre-configure apps with credentials, data, access management, app tunnel or even other mandatory requirements like the Single Sign-On. You can also blacklist applications to restrict one or a group of apps; not trusted by the organization from being run on the end-user device. Whitelisting, on the other hand, allows the device to run only a set of pre-selected applications on the end-user device, blocking all the other applications. With blacklisting and whitelisting, you can be sure that your device is well shielded from most app-based vulnerabilities. Also, you have the custom app store feature whereby you can easily download the required enterprise apps securely.
Hassle free app management with Android Enterprise & Hexnode
OS update management

We all have this strange habit of delaying updates, isn’t it? Sometimes the reason we procrastinate this process is because we are not well acquainted with its drawbacks. We often overlook the significant roles that updates play in sealing most of the vulnerabilities. So, by timely updating, we are equipping our devices to fight vulnerabilities more effectively, in addition to unlocking advanced management capabilities and increasing the overall productivity of the users.
With Hexnode, you can easily enforce updates on your iOS, Android or macOS devices. In iOS devices, you have options like download only or download and install, giving you the flexibility to install updates automatically once they’re downloaded or just download the update and install it as and when required. Android devices also allow you to either “Automatically install the update” silently or enable the users to install them by prompting them to install the update. Mac devices also offer options similar to iOS devices, allowing you to download or download and install updates as per your requirements.
The bottom line
It’s no doubt that the anywhere operations model is here to stay. With this model, you can easily reach customers, deploy products, and access services from literally ‘anywhere.’ However, a system that is open to access from anywhere can also be exposed to vulnerabilities ‘from anywhere.’ And with Hexnode’s easy enrollment methods, remote access features, security, app and update management, creating a secure environment has become even easier.
Begin your journey with Hexnode
Strengthen your anywhere operations model with extensive management strategies of Hexnode
START YOUR 14 DAY FREE TRIALShare this Infographic on your site
Copy the code to embed this infographic on your website -







