Linux Device Management 101
Tricky Linux hardware? Our Device Management 101 tutorial breaks down udev rules and the /dev filesystem into simple steps.

Get fresh insights, pro tips, and thought starters–only the best of posts for you.

When public-access machines, whether in retail stores, libraries, or airports are left unrestricted, users can tamper with the settings, browse off-limits websites, or even compromise system data. Businesses need a way to lock down these devices for a specific purpose, say, displaying digital signage, running a check-in system, or powering on information terminal, without sacrificing performance or usability.
That’s where Linux kiosk mode comes in. This blog explores how you can leverage Linux’s flexibility to create a secure, single-purpose environment that keeps users focused on exactly what you want them to access and nothing else.
By the end, you’ll not only know how to enable Linux kiosk mode, but also about how Hexnode assists in its setup, management and security while also optimizing it for reliability, security, and real-world usability.
At the core, Linux kiosk mode refers to configuring a Linux device, so it runs a single application, or a restricted set of applications, while ensuring users have a focused experience within a controlled environment. Unlike a generic locked-down interface or a system in secure mode, a Linux kiosk setup is intentionally minimal.
A kiosk device is a computing system configured to serve a single, well-defined purpose with a locked-down interface. When it comes to implementing kiosk mode, Linux has become a platform of choice. Its strengths lie in flexibility, low cost, and the fact that it’s open source.
Depending on the deployment environment, Linux kiosk mode can take several forms:
Like any deployment strategy, Linux as a kiosk terminal brings notable benefits and a few challenges:
Pros
Cons / Challenges
The many ways of Linux kiosk mode make it a natural fit across industries. From digital signage kiosks to secure testing terminals, organizations rely on Linux to deliver stable, locked-down environments that are lightweight yet customizable. Below are some of the real-world applications.
Linux-powered kiosks can run in single-app mode, looping browser-based content or signage software in full-screen. They’re widely adopted for:
Key Benefits: Lightweight OS, remote content updates, and minimal maintenance. This makes Linux digital signage kiosks highly scalable for enterprise environments.
A Linux kiosk setup can streamline customer interactions by powering POS systems, self-checkout counters, or ordering stations. Common deployments include:
Why Linux: Stable under heavy workloads, hardware-agnostic, and easy to customize for branding and workflows.
Hospitals and clinics implement Linux kiosks to improve patient service efficiency while maintaining compliance. Typical use cases:
Security Note: With the right lockdown policies, Linux kiosk mode can be hardened to align with HIPAA or local data compliance frameworks.
Academic institutions use Linux as a kiosk terminal to provide controlled access to educational tools. Examples include:
Why It Works: Restricts misuse, prevents distractions, and reduces IT maintenance overhead.
Enterprises leverage embedded Linux kiosks to display real-time data in workspaces or production floors. These include:
Advantage: Minimal overhead, fast boot, and automatic lockdown for continuous uptime.
Tourism boards and municipalities adopt Linux digital signage kiosks to help visitors navigate spaces. Examples:
UX Consideration: Linux enables full UI customization and multilingual support, improving accessibility.
In R&D and industrial labs, Linux single-app mode is often used to isolate testing systems. Applications include:
This ensures only designated apps run, minimizing risk of tampering or accidental interruptions.
Before diving into setup, a successful Linux kiosk mode implementation depends majorly on planning. From hardware selection to recovery strategies, each choice determines the kiosk’s reliability, performance, and security. Below are the critical factors to evaluate before deployment.
The foundation of a Linux kiosk setup begins with the right combination of hardware and operating system:
A well-designed kiosk environment minimizes user privileges and automates session handling:
At the heart of Linux single-app mode is the application users will interact with:
Network planning and lifecycle management are crucial for long-term kiosk reliability:
Resilience is key for unattended kiosks that must operate continuously:
Explore Hexnode's advanced capabilities for Linux endpoint management, focusing on how the platform delivers centralized security, configuration, and administrative control.
Download InfographicThis section covers two canonical options, a browser-based kiosk and a custom application kiosk, plus the system-level plumbing to build a fully locked-down Linux kiosk mode.
To note: The scripts below are templates. Adjust paths, user names, environment variables, and options for your Linux distro, display server (X11 / Wayland), and app requirements.
For modern desktops (Ubuntu, Fedora) running Wayland, the built-in single-application session method is preferred over custom Window Manager (WM) hacks as it’s more secure and resilient.
This method relies on setting up a custom session that runs a specific application instead of the full GNOME Shell.
1. Create a kiosk user:
|
1 2 |
sudo useradd -m -s /bin/bash kiosk sudo passwd -d kiosk # Set passwordless login |
2. Create the application desktop file:
File: /usr/share/applications/kiosk-app.desktop
|
1 2 3 4 5 6 7 8 |
[Desktop Entry] Name=Kiosk Application Comment=Starts Chromium in Kiosk Mode Exec=/usr/bin/chromium-browser --kiosk --incognito --noerrdialogs --disable-session-crashed-bubble http://your-url-here Icon=chromium Type=Application Terminal=false X-GNOME-WM-Class=kiosk-app |
3. Create a custom session file:
This file tells the display manager (GDM/LightDM) to use the Kiosk Application instead of a standard session. File: /usr/share/xsessions/kiosk.desktop (for X11/Fallback) File: /usr/share/wayland-sessions/kiosk.desktop (for Wayland)
|
1 2 3 4 5 6 |
[Desktop Entry] Name=Kiosk Mode Session Comment=Kiosk mode running a single app Exec=/home/kiosk/kiosk-wrapper.sh Type=Application DesktopNames=Kiosk |
(Note: The Exec line points to a wrapper script to handle environment setup, similar to your original Openbox script, but without the X11 specific xset commands if using Wayland).
4. Configure GDM for auto-login:
File: /etc/gdm/custom.conf
|
1 2 3 4 5 6 |
#GDM autologin is usually configured in custom.conf [daemon] AutomaticLoginEnable=true AutomaticLogin=kiosk #Optionally, set the default session for the user #Note: On many modern systems, the session is set in /var/lib/AccountsService/users/kiosk |
For digital signage and web dashboards on Ubuntu Core or Server, Ubuntu Frame is a highly recommended, purpose-built, Wayland-based solution for running a single window full-screen.
1. Install Ubuntu frame and an application snap:
|
1 2 3 4 5 |
sudo snap install ubuntu-frame # For a web kiosk: sudo snap install wpe-webkit-mir-kiosk # Connect the app to the frame sudo snap connect wpe-webkit-mir-kiosk:wayland ubuntu-frame:wayland |
2. Set the URL:
The app snap usually has a simple configuration to set the content.
|
1 |
sudo snap set wpe-webkit-mir-kiosk url='http://your-signage-url' |
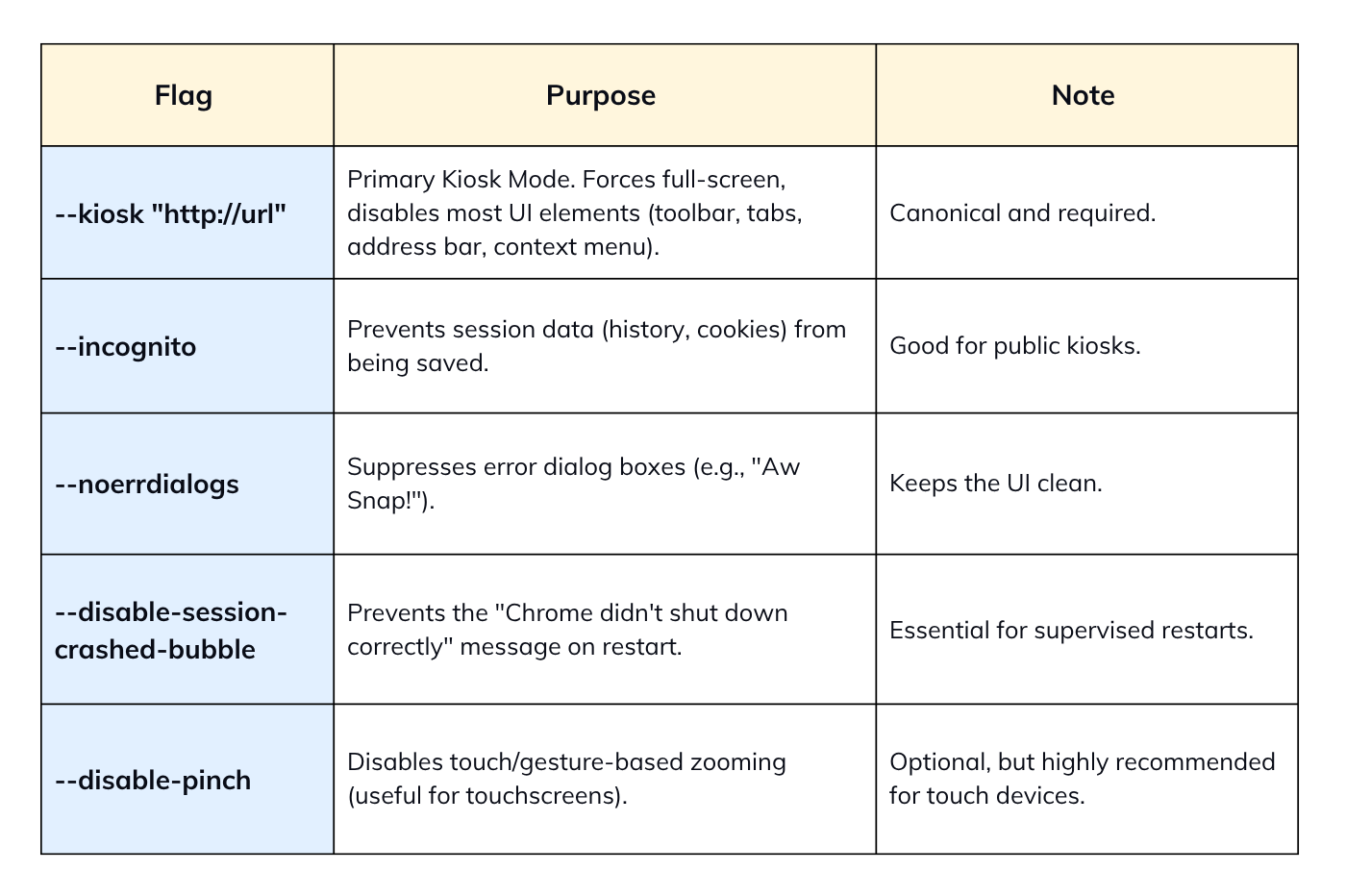
The following set of Chromium flags is current, robust, and supported.
The recommended way is to use a configuration drop-in file to avoid modifying the main /etc/lightdm/lightdm.conf.
File: /etc/lightdm/lightdm.conf.d/50-kiosk.conf
|
1 2 3 4 |
[Seat:*] autologin-user=kiosk autologin-user-timeout=0 user-session=openbox # Must match a name from /usr/share/xsessions/*.desktop |
Explicitly note the path and the use of & for running the script non-blocking.
File: /home/kiosk/.config/openbox/autostart
|
1 2 3 4 5 6 7 8 |
#!/bin/sh # Disable power management xset s off & xset s noblank & xset -dpms & # Launch your main script in the background /home/kiosk/kiosk.sh & |
The DontVTSwitch and DontZap options are valid, but must be presented as obfuscation and not as a security boundary.
File: /etc/X11/xorg.conf
|
1 2 3 4 5 6 |
Section "ServerFlags" # Prevents Ctrl+Alt+Backspace from killing the X server Option "DontZap" "true" # Prevents Ctrl+Alt+Fx from switching Virtual Terminals (TTYs) Option "DontVTSwitch" "true" EndSection |
For managed multi-app environments, using a minimal WM to launch a supervisor or using a commercial MDM/UEM solution is the secure approach.
This uses Openbox (or similar) to launch a simple, curated desktop environment you control (e.g., a custom task switcher or launcher application).
Setup Openbox/LightDM.
Modify /home/kiosk/.config/openbox/autostart to launch your supervisor app.
|
1 2 3 4 5 |
#!/bin/sh # xset commands... (if needed) # Launch a custom application that acts as a simple, full-screen menu/launcher /usr/bin/my-kiosk-supervisor & |
The my-kiosk-supervisor app must handle launching, switching, and relaunching the approved applications.
For enterprise security and policy management, a commercial solution is far more effective for multi-app control, as it uses an agent to enforce a strict allow-list and prevent process-level escapes.
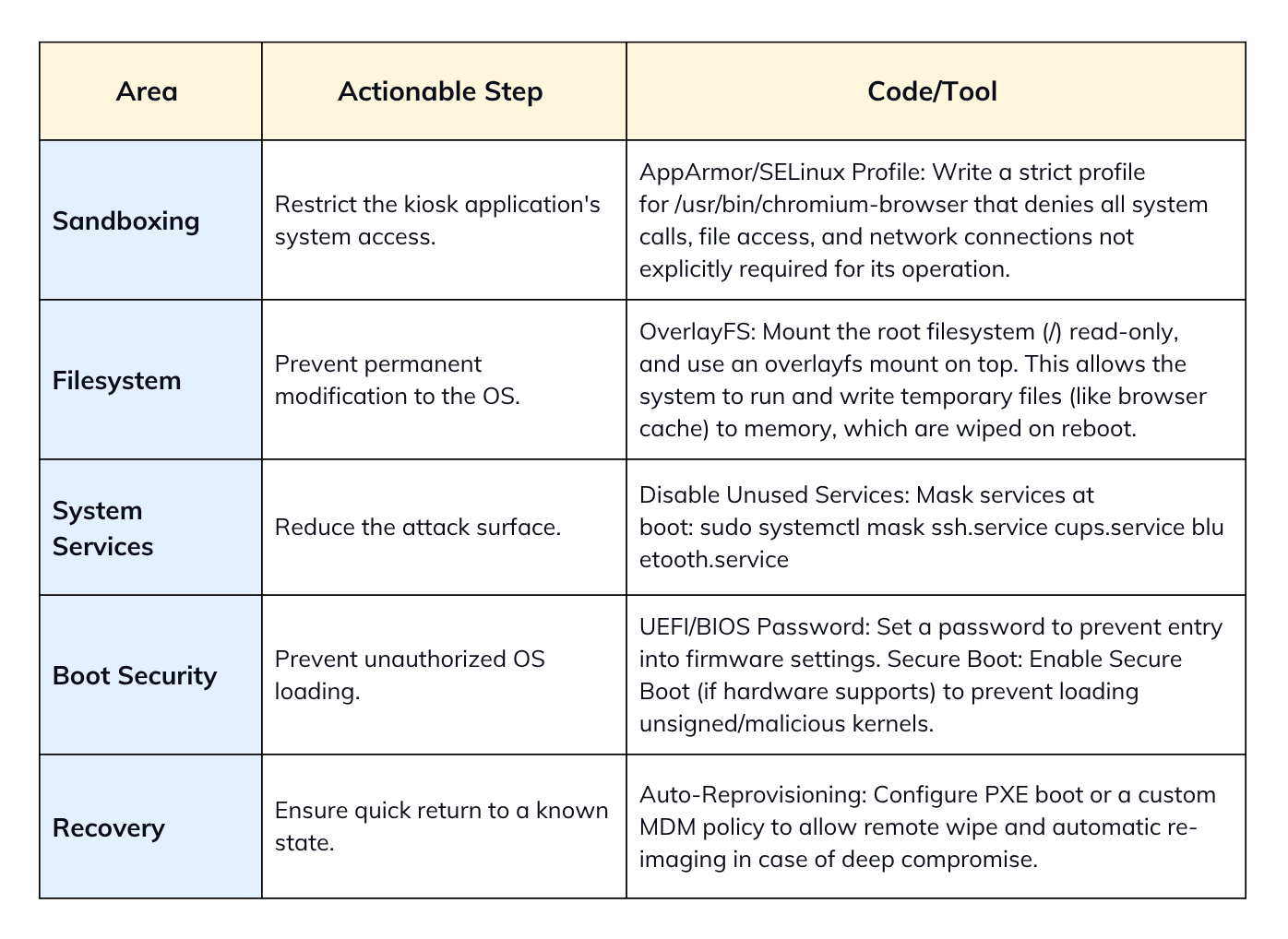
Security should focus on sandboxing and creating a read-only root filesystem.
systemd is the recommended baseline for launching and supervising the kiosk application due to its robust restart/monitoring capabilities.
File: /etc/systemd/system/kiosk-app.service
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 |
[Unit] Description=Kiosk Application Service After=network.target graphical.target [Service] Type=simple User=kiosk Environment=DISPLAY=:0 # Use the full path to your kiosk app/script ExecStart=/home/kiosk/kiosk.sh Restart=always RestartSec=5 # Optional: Enable systemd watchdog for external health check # Requires application to send sd_notify(WATCHDOG=1) signal, # or use a check script combined with Type=simple (less effective). # WatchdogSec=30s [Install] WantedBy=graphical.target |
To activate:
|
1 2 |
sudo systemctl daemon-reload sudo systemctl enable --now kiosk-app.service |
Restart=always ensures that if the app process crashes, is manually killed, or exits (as in your loop-less GNOME setup), systemd will restart it automatically after RestartSec seconds.
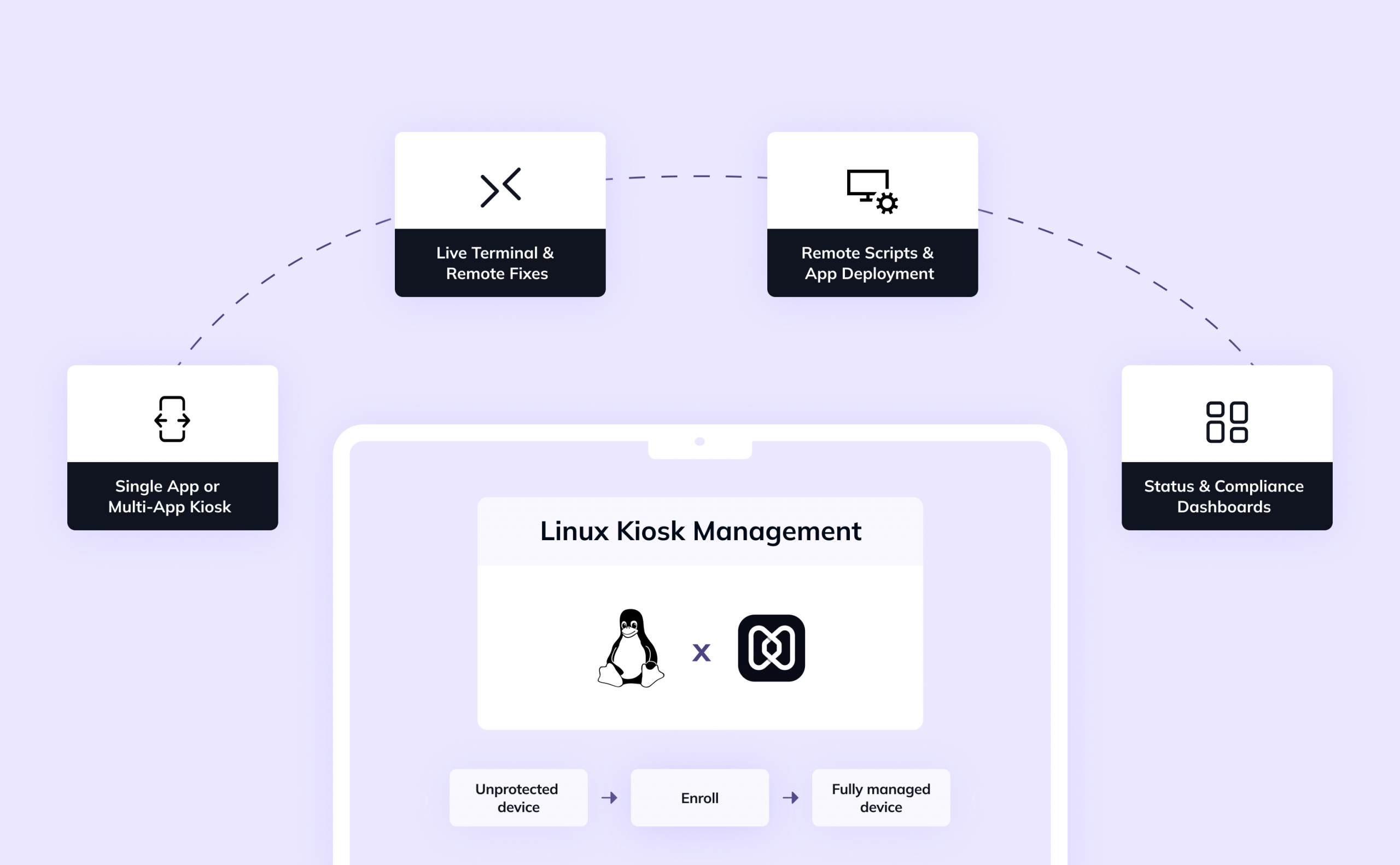
So, how you can leverage Hexnode to simplify your Linux kiosk lifecycle? Here’s how
While Hexnode has long supported kiosk lock-down for Android, iOS, and Windows, its Linux device complete kiosk management solution is increasingly robust.
Key capabilities include:
As of now, the primary mode for Linux kiosk support is single app mode configuring – a device to boot directly into one designated app (your kiosk mode) and preventing users from exiting it.
You must enroll your Linux devices into your Hexnode UEM environment, before you can manage kiosk mode:
After devices are enrolled, you can define a kiosk policy and apply it:
Once devices are managed, Hexnode offers a variety of remote tools:
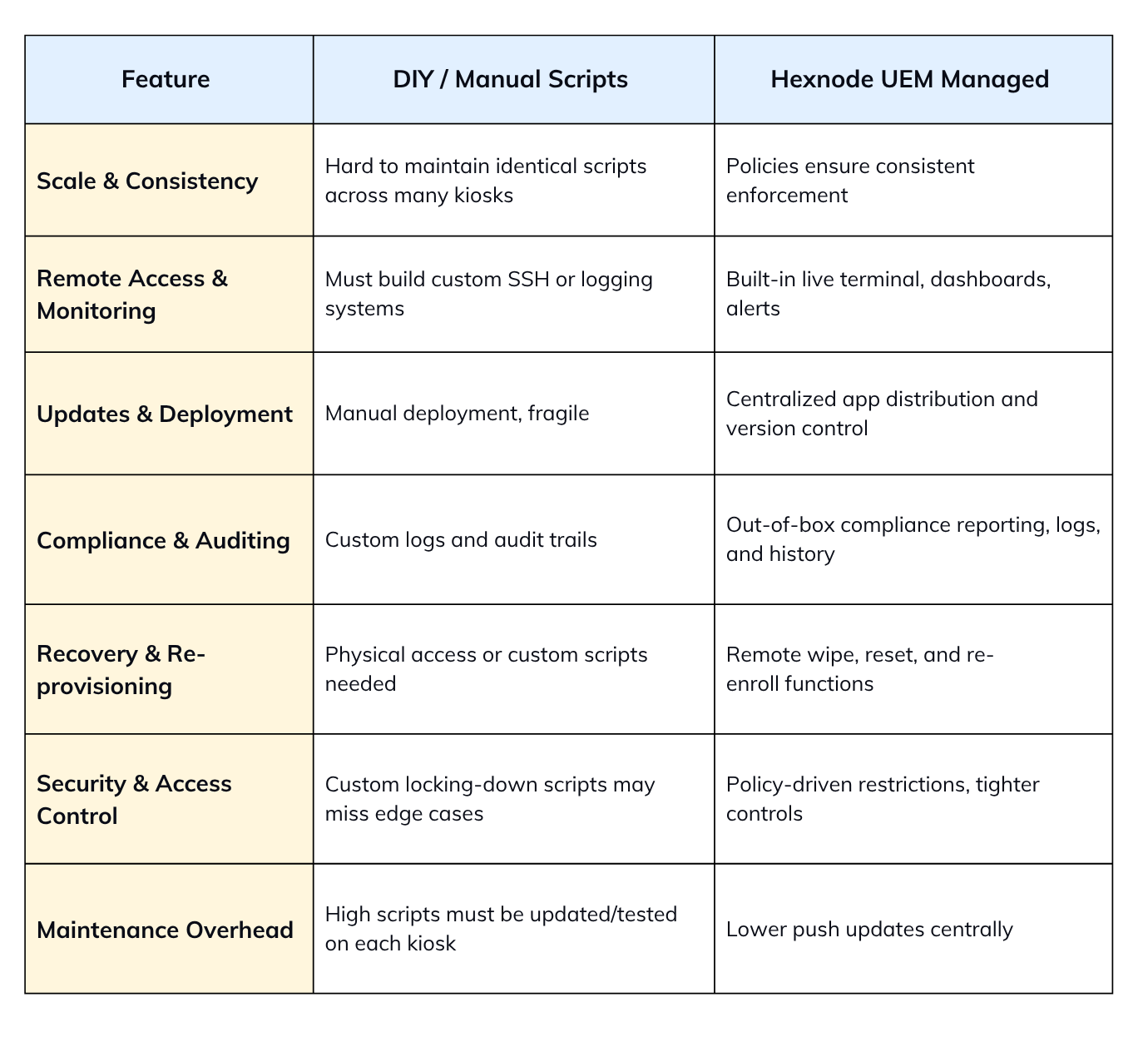
Adopting Hexnode for managing linux kiosk mode offers several advantages over a purely DIY, script-based approach:
With a good Linux kiosk setup present, the operational reliability depends on following a disciplined set of best practices. Skipping these steps often leads to avoidable downtime, security incidents, or excessive IT overhead.
Make the system accommodate only what’s necessary:
Plan for unavoidable failures:
The kiosk is as secure as its connectivity:
Visibility is much needed for uptime and compliance:
Kiosks shouldn’t crash when the network drops:
Even stable apps store memory usage over time:
Never push changes directly to production kiosks:
A kiosk is often exposed in public areas:
1. Can I exit the Linux kiosk mode?
Yes, you can but you’ll need admin control. Usually, users can’t exit due to locked hotkeys and restricted shells. Recovery is normally done through SSH, alternate TTYs, or editing startup scripts.
2. What happens if the app crashes in Linux kiosk mode?
Without safety measures, the screen may go blank or return to the desktop. Using systemd service unit configuration with Restart=always auto-restarts the app. Watchdog scripts also provide extra protection. Hexnode can enforce remote recovery.
3. Can I update the Linux kiosk app remotely?
Updates can be pushed through SSH scripts or package managers in DIY scenarios. Enterprises use UEM tools for remote app deployment.
4. Can I have multiple apps or switch between modes in Linux kiosk mode?
Linux kiosk mode is usually single-app, but multi-app kiosks are possible. A lightweight window manager can control switching securely. Hexnode profiles allow policy-based mode switching. Always ensure apps remain sandboxed.
5. Does Linux kiosk mode support touch / gestures?
Yes, if the hardware drivers are supported by the distro. Chromium, Qt, and GTK apps can handle touchscreen input natively. Kiosks often use touch for digital signage or POS. Optimize UI for gesture-friendly layouts.
6. Is Linux kiosk mode secure and tamper-proof?
It can be hardened, but no system is fully tamper-proof. Lock shells, disable hotkeys, and block unused ports. Use SELinux/AppArmor to sandbox apps. Combine with secure boot, firmware locks, and enclosures for strong protection.
Linux kiosk mode transforms a general-purpose Linux system into a locked-down, single-purpose terminal. Whether for digital signage, self-service kiosks, or enterprise dashboards, it provides a secure, minimal, and flexible environment.
If you’ve just begun, Hexnode offers a 14-day free trial for you to understand the product better. Once proven, increase gradually across your workspace and simplify policies like updates, monitoring, and compliance enforcement.
Ready to streamline your kiosk deployments? Try Hexnode’s free trial to see how easy it is to create, manage, and secure Linux kiosks at large.
1. Systemd Unit Configuration (Restart/Supervision):
Source: FreeDesktop.org – systemd.service man page
Source: Linux Kernel/Watchdog Documentation (For WatchdogSec context)
2. GNOME Kiosk Mode/Session Files:
Source: GNOME System Administration Guide – Single-Application Mode
3. Chromium Command Line Flags:
Source: Chromium Googlesource – Command Line Switches
4. LightDM Configuration (autologin):
Source: Ubuntu/Arch Linux LightDM Wiki Documentation
5. Xorg ServerFlags (DontZap, DontVTSwitch):
Source: X.Org Server Documentation (xorg.conf man page)
6. Ubuntu Frame Kiosk:
Source: Canonical/Ubuntu Frame Snap Documentation
Start your 14-day free trial now and see how easy it can be to manage your system!
Signup now!